- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GP VPN users cant connect when we run PAN-OS 8.1
- LIVEcommunity
- Discussions
- General Topics
- GP VPN users cant connect when we run PAN-OS 8.1
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 04:23 AM
Hi
Has anyone had any issues with users connecting in using global protect once they have upgraded from PAN-OS 8.0.15 to any version of 8.1?
I had a change window the other night and updated to 8.1.6 which everything worked fine except for VPN access, people connecting in would constantly be prompted to type in the token passcode. We could see errors on our RADIUS server and RSA servers but nothing in the system log on the firewall. As soon i failed back to using 8.0.15 VPN access was restored. I have logged a tech support call about this and pointed out there was a bug we had last year that was fixed but it seems that maybe in 8.1 either this fix hasnt been applied or in 8.1 GP clients log in differently? I am still waiting for TAC to get back to me but i just thought i would reach out on here as well. We are still running GP version 3.1.5-9 as well
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 07:18 AM
Thats probably because your radius name is the same as your AD name, My AD name is dotted.
so i ran a radius debug and it is not only sending dotted username bur also AD password...... read on....
OK got it sussed...
you need to change the portal app setting "use single sign on" from "yes" to "no". default is yes and this never made much difference before but I do know they made a lot of updates to SSO in 8.1 so probably fixed it too much... Ha ha.
this is now working for me and breaks again wen SSO is set to yes.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 04:46 AM
it's a shame you cannot replicate the issue on a test box.
when the users were re prompted for passcode was it for the gateway or the portal.
if the gateway only then maybe an issue with authentication overide, if portal (or web page to portal) then it may simply be an issue regarding pap/chap
what was the error on RSA/Radius servers.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 05:00 AM
Hi
from the end users perspective it was from the global protect client that kept on asking them to enter a passcode again so i would say it from the portal, NOT the gateway.
On our RADIUS server you would see 2 hits for each attempt, one success and one failure. Even though at the other end (VPN client end) the user would just be prompted for a passcode again. The RADIUS logs say user authentication failed, check RSA logs.
RSA has a bit more info but seems to point to the user not putting in the correct token code or bad PIN, which i would normally believe but we tried a couple of IT people to test and they couldn't all forget their PIN or type in an incorrect token code at the same time, but then get it working when we tried it on the firewall running 8.0.15. That's why i was thinking maybe something had changed between 8.0 and 8.1 or maybe GP version we have isnt supported in 8.1?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 05:04 AM
OK thanks for the update.
your monitor/system will show you where the auth is failing but no good to you now i suppose
when the user was prompted to re-enter the passcode, did they wait for it to change?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 05:39 AM
I even tested it at the same time tried a few things, made sure the i had the correct pin, token wasnt about to expire, even waited for a next token code but still nothing.
It seems there may be nothing obvious that has changed but i will have to wait for TAC to get back to see if they can think of anything, but i am probably going to have to schedule in some time out of hours upgrade again and test it again and again
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 05:43 AM - edited 03-13-2019 05:43 AM
sure, you do not have much choice, i have just bumped my QA pair to 8.16 from 8.10 to see what happens...
sorry... 8.16 from 8.00
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 05:48 AM
OK upgrade and re prompted for gateway auth, so something has broke... I will check the logs...
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 05:55 AM
ah ha, so im not the only one that has this issue
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 05:56 AM
well at least 2 of us are... I can see what is going wrong...
Please hold caller....
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 06:05 AM
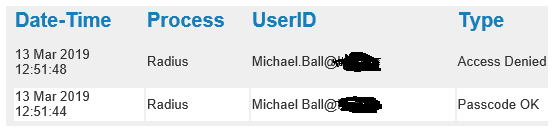
It is modifying the gateway username, i have no idea why....
it is not using the auth overide cookie and is also adding a dot (.) notation to the logon name.
as you can see below.... the first auth is OK at 12:51:44 so portal is done, 4 seconds later it tries to re-use the passcode but with a dot notation.
I'm gonna try to re configure auth overide.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 07:04 AM
My RADIUS logs doesnt seem to change the username like yours does, but there is obviously an issue. I have updated my TAC case with this info so hopefully we can get to the bottom of this soon.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 07:18 AM
Thats probably because your radius name is the same as your AD name, My AD name is dotted.
so i ran a radius debug and it is not only sending dotted username bur also AD password...... read on....
OK got it sussed...
you need to change the portal app setting "use single sign on" from "yes" to "no". default is yes and this never made much difference before but I do know they made a lot of updates to SSO in 8.1 so probably fixed it too much... Ha ha.
this is now working for me and breaks again wen SSO is set to yes.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-13-2019 07:25 AM
Brillant! OK i will need to book it this in and test it so i will come back to you soon to confirm it.
Thank you for spending time getting to the bottom of this
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-09-2019 01:51 PM
Sorry it has taken so long to reply i have only now had time to update the firewalls, this time to 8.1.7, but the difference was this time around VPN connectivity wasnt affected, so i didnt need to make your suggested changes.
I have only just finished the upgrade but i can see SSO is still set to yes, so all i am thinking is maybe this was a bug that was fixed in 8.1.7! I will check the change log
Thanks for your help with this
- 1 accepted solution
- 9631 Views
- 13 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Global Protect count current users not match statistics in GlobalProtect Discussions
- Config admin using radius group. in General Topics
- Disconnect Internally but not remotely in GlobalProtect Discussions