- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
HA Cluster Network Topology
- LIVEcommunity
- Discussions
- General Topics
- HA Cluster Network Topology
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-23-2020 11:04 PM
Hi Everyone,
I'm new to Palo Alto and now I plan to deploy 2 Palo Alto 5250 in HA Cluster mode, each firewall take place in a Data Center. This two Data Center is in same City. That why I think HA Cluster suitable in this situation. These 2 new firewalls is replace for a Cluster Check Point Firewall. After reading all document about HA Cluster I still can't imaging how the network topology gonna be so if anybody here have experience about deploy HA Cluster please share with me. Previously with Checkpoint, each firewall will have an Physical IP and choose a Virtual IP to be a gateway. All Endpoint will specific Gateway is the Virtual IP, but with Palo Alto HA Cluster it might look more complicated.
Please help share some info about topology. Thanks
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2020 07:07 PM
A few things to note with Clustering:
1) This is a stopgap and really isn't full cluster support. The feature will be fleshed out more in future releases.
2) The primary focus here is session survivability between multiple DCs, if you can support your particular deployment via Active/Passive or Active/Active that's preferred by support.
3) Clusters only support layer3 or vwire, layer2 is not supported.
4) Clusters don't syncing configuration between cluster members. Clustering in PAN sense is really just for session sync between cluster members for seamless session failover. Generally through Panorama or manual templating if you aren't using panorama.
5) Zones need to be exactly the same between cluster members, otherwise the session will be dropped when it's sync'd between peers.
If you aren't running a dynamic routing protocol this isn't going to be for you. In standalone a failure would put all device links in a non-functional state and pass session ownership to the peer member. Link and path monitoring can either be set to go NF or not depending on your requirements, but it would be recommended since clusters don't monitor of NF state and could cause looping.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-24-2020 08:24 PM
You're not really giving a lot of information to give you any help with. We don't know what the rest of your network looks like, we don't know if you're deploying active/passive or active/active, or really any information needed to help you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-25-2020 06:48 AM
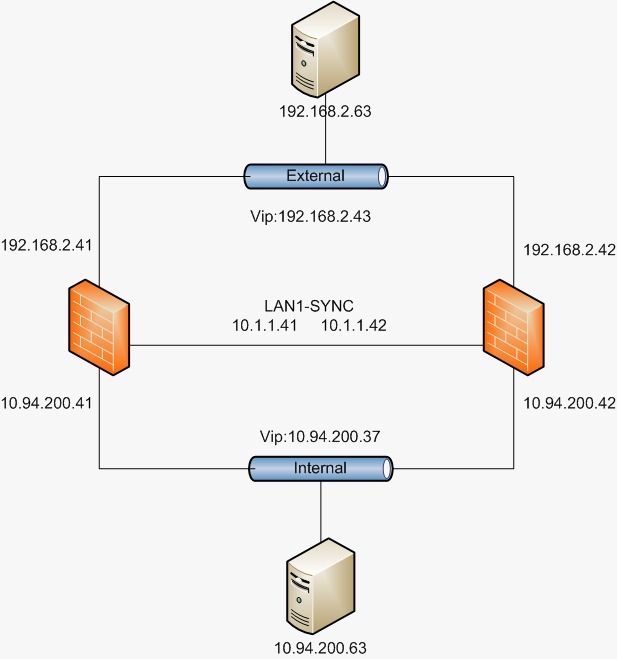
Hi @BPry , Thank you for reply me. Let me send you an example.
In current network topology, it look pretty similar to this. And I think you misunderstand something here @BPry . Because with HA Cluster, there is no Passive. All member is always Active but they can also be a part of HA Pair where we have Passive. You can check this document.
https://docs.paloaltonetworks.com/pan-os/10-0/pan-os-admin/high-availability/ha-clustering-overview....
This HA Cluster only just appear from PAN OS version 10 so I have no idea about this.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-25-2020 07:04 AM
Okay so you're talking about an actual cluster. When I see someone refer to a cluster in PAN I just assume that they are talking about an HA pair, because usually they are simply using improper terminology.
For the example that you sent over, are the two firewalls that you actually have referenced actually just two firewalls or two separate pairs? It sounds like you're just talking about having two standalone cluster members? If that's the case you won't gain anything by deploying clustering over a simple Active/Passive or Active/Active deployment.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-25-2020 06:49 PM
Hi @BPry this is the current firewall topology i have with 2 Check Point firewall and it will be replace with 2 PA 5250. With Check Point Cluster it can be Active Ative or Active Passive base on your decision. And each firewall stay in a difference DC. Let say FW1 place at DC1 and FW2 place at DC2. DC1 and DC2 is in the same city but still far form each other. The sync interface between 2 firewall is 1Gbps Fiber cable connect between 2 DC. Now when deploy new PA firewall, if using HA pair i'm not sure HA1, HA2, HA3 can use 1Gbps link or it have to be 10Gbps link which not available to me right now. So i decide to use HA Cluster where HA4 can use 1Gbps link, it also design for HA between 2 DC. But i have no idea how it work, it will have a virtual IP between two cluster member like Check Point Cluster or else. Please help share with me about this. Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2020 08:04 AM
Hello, I'm interested in this topic because I would like so set-up a lab environment to test the new cluster deployment in PAN-OS 10.
Reading the documentation, the cluster setup seems quite simple, but the admin manual lacks information about the topology in comparison to the "classic" HA Active/Passive or Active/Active deployments.
What @QuangLe is asking for (I suppose) is how to balance the traffic towards the different DCs and how one firewall takes over the other in case of a failure. If we have cluster with two "single" devices as members, what happens from a network point of view when one cluster member fails?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2020 06:18 PM
Hi @grenzi , yes you're right. That exactly what i looking for. I don't know how many ip it need for each cluster interface pair. how it load balance or take over in case one firewall down. The document give us no information.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2020 07:07 PM
A few things to note with Clustering:
1) This is a stopgap and really isn't full cluster support. The feature will be fleshed out more in future releases.
2) The primary focus here is session survivability between multiple DCs, if you can support your particular deployment via Active/Passive or Active/Active that's preferred by support.
3) Clusters only support layer3 or vwire, layer2 is not supported.
4) Clusters don't syncing configuration between cluster members. Clustering in PAN sense is really just for session sync between cluster members for seamless session failover. Generally through Panorama or manual templating if you aren't using panorama.
5) Zones need to be exactly the same between cluster members, otherwise the session will be dropped when it's sync'd between peers.
If you aren't running a dynamic routing protocol this isn't going to be for you. In standalone a failure would put all device links in a non-functional state and pass session ownership to the peer member. Link and path monitoring can either be set to go NF or not depending on your requirements, but it would be recommended since clusters don't monitor of NF state and could cause looping.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2020 06:19 PM
Hi @BPry thank you for provide very helpful information.
2) If i go with HA pair Active-Active, can i use 1 Gbps Fiber link for HA1, HA2, HA3 ?
3) That ok, i only use Layer 3 Deployment,
4) Yes, currently i don't have Panaroma.
Yes, currently i only use static route. Dynamic is really not needed in my case because i ony have 2 default route to 2 GW with difference priority.
- 1 accepted solution
- 11999 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma Access CIE and User-ID mapping not working for groups in Prisma Access Discussions
- Dynamic IP at Spoke site in PAN-OS SD-WAN Hub/Spoke topology in Next-Generation Firewall Discussions
- Paloalto NGFW - Policy-Based Forwarding (PBF) - Enforce Symmetric Return in General Topics
- Design suggestion in Next-Generation Firewall Discussions
- PANOS SDWAN Monitoring in Advanced SD-WAN for NGFW Discussions