- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
IPSec VPN with overlapping networks
- LIVEcommunity
- Discussions
- General Topics
- IPSec VPN with overlapping networks
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 06:51 AM - edited 11-02-2018 10:49 AM
To begin with I know the document Configuring IPSec VPN between overlapping networks.
Due to my lack of experience still I am not able to understand how I should create the NAT rules.
My objective is to configure the IPSec tunnel only on "my" side - one that will be accessed and should allow access to some servers in the 192.168.2.0/24 network.
Below I put some aqnonymised configuration info:
IKE Gateway
Parameter | Value |
Version | IKEv1 only mode |
Address type | IPv4 |
Local IP Address | a.b.c.99 |
Peer IP Address | x.y.z.255 |
Exchange mode | auto |
IPSec Tunnel Proxy IDs
Parameter | Value |
Local | 10.0.2.0/24 (NAT 1:1 – original subnet 192.168.2.0/24 ) |
Remote |
The overlapping network addresses are 192.168.2.0/24
I have to create a NAT rule to show them to the accessing partner as 10.0.2.0/24 network.
I would be grateful if someone could tell me how to create this NAT rule with static translation.
Thank You a LOT! 🙂
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-20-2018 03:37 AM
Below is the configuration that finally worked.
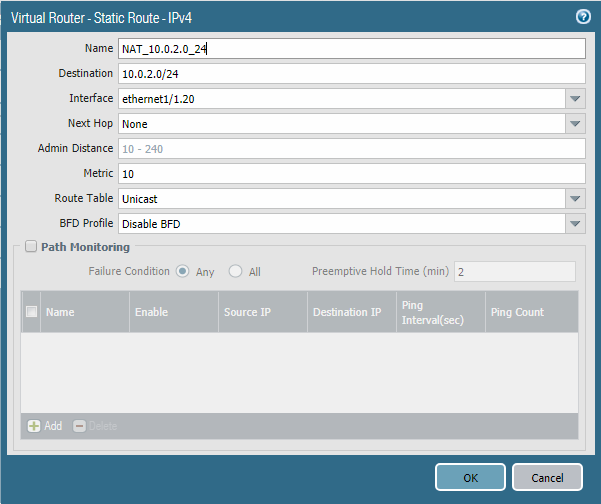
Static Route
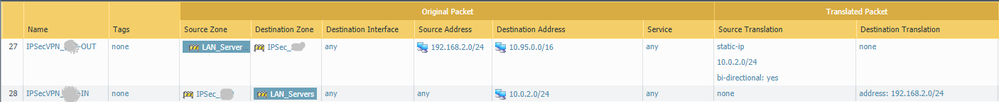
NAT
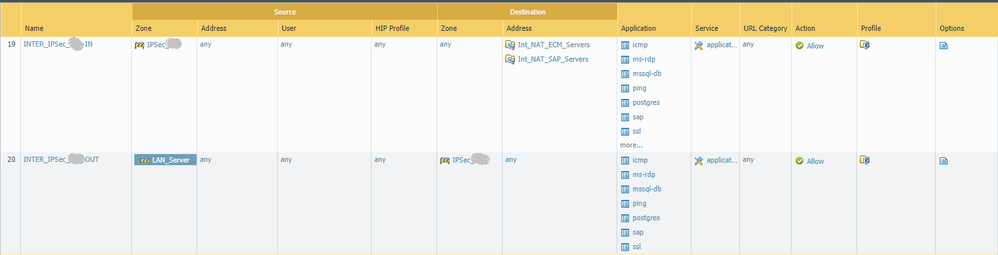
Security rules
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 07:10 AM
Let's say partners want to access server at 192.168.2.10. Chose an IP you will use for NAT, let's say it's 10.0.2.10 (though any from that network would do).
All you need is a static destination NAT: source 10.95.0.0/16, destination 10.0.2.10, Destination Address Translation 192.168.2.10 (with apropriate zones).
And also you will need a firewall rule to allow access with pre-NAT IP address and post-NAT destination zone.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 07:23 AM
I would like a rule that will translate any address in 192.168.2.0 into a coresponding address in 10.0.2.0 (192.168.2.1-->10.0.2.1, 192.168.2.2-->10.0.2.2 etc).
Can it bo done?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 08:46 AM
@Filip_Fronczak wrote:I would like a rule that will translate any address in 192.168.2.0 into a coresponding address in 10.0.2.0 (192.168.2.1-->10.0.2.1, 192.168.2.2-->10.0.2.2 etc).
Can it bo done?
Yes, this is possible.
- Destination address object: 192.168.2.0/24
- Destination translation address object: 10.0.2.0/24
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 09:53 AM
Is this enough or should there be something more?
Do I need on my side a NAT rule to translate the source too or a rule in the other direction?
Sorry for asking basic questions...
IPSecVPN_1
{
to [ LAN_Servers ]; from [ IPSec_xxx ]; source [ any ]; destination [ 192.168.2.0/24 ]; service any; disabled no; destination-translation
{
translated-address 10.0.2.0/24;
}
}
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 10:05 AM
Ignore my last post ...
The NAT rule shoild look like this
- Original source: 192.168.2.0/24
- Original destination: 10.95.0.0/16
- Type: Static IP
- Translated source: 10.0.2.0/24
- Translated destination: none
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 10:32 AM
And what about the other way?
Traffic from the oher side that wants to arrive to servers in our network - 192.168.2.0/24?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 10:55 AM
Check the bi-directional checkbox
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 11:07 AM
So, it's this, right?
IPSecVPN_xxx-1
{
to [ IPSec_xxx ]; from [ LAN_Servers ]; source [ 192.168.2.0/24 ]; destination [ 10.95.0.0/16 ]; source-translation
{
static-ip
{
bi-directional yes; translated-address 10.0.2.0/24;
}
}
}
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 06:59 AM
Something is not right.
The phase-2 config on the connecting party is like this:
config vpn ipsec phase2-interface
edit "VPN"
set phase1name "VPN"
set proposal aes256-sha256
set dhgrp 14
set keylifeseconds 3600
set src-subnet 10.95.0.0 255.255.0.0
set dst-subnet 10.0.2.0 255.255.255.0
next
end
The tunnel is established but they are not able to ping servers on our side.
I do not see any traffic even in the "Session Browser".
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 10:53 PM
Assuming you log everything; untill you don't see a packet arriving from their side it means they are not sending it correctly.
You can also try sending traffic towards them.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2018 03:19 AM
Fist I would suggest you to disable the bi-directional for the source NAT and configure manually destination NAT. The main reason for that is - What does the Bi-directional NAT Feature Provide? My phisosofy is to enable bi-directional only for static NAT going to public. NATing for VPN could be little bit tricky. So I would suggest the following:
## Source NAT
IPSecVPN_xxx-1 {
to [ IPSec_xxx ];
from [ LAN_Servers ];
source [ 192.168.2.0/24 ];
destination [ 10.95.0.0/16 ];
source-translation {
static-ip {
bi-directional no; translated-address 10.0.2.0/24;
}
}
}
#### Destination NAT
IPSecVPN_xxx-2 {
to [ Untrust ]
from [ IPSec_xxx]
source [ 10.95.0.0/16 ]
destination [ 10.0.2.0/24 ]
destination-translation {
translated-address 192.168.2.0/24;
}Note: that the to zone in your destination NAT should be zone based on your routing table for 10.0.2.0/24. If you don't have route for such network, traffic will be routed with default route to outside (or your what ever default is related). if you have route matching this network (for example 10.0.0.0/8) you need to put the zone following this route)
Remember:
• NAT rule must be configured with pre-NAT zones (zones matching the addresses before the NAT) • Security rule must be configured with pre-NAT addresses, but post-NAT zones
Having the bidirectional enabled should work indeed, so if the traffic is failing I would suggest:
- Check the rule on the Fortigate at the other end
- Check the routing on the Fortigate at the other end
- Check if encrypted packets are increasing on the Fortigate
- Check for decrypted packets on your end
- As per revious comment - check if you can send traffic
- Check the log to confirm the NAT is applied
- Check for encrypted packets at your end and decrypted packets at Forti end
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-12-2018 12:57 PM
I am still stuck here. There is not much I can check on the other side. They say that the traffic is entering the tunnel.
I do not see any traffic on my side.
In vRouter I have a static route for 10.95.0.0/16 directing it to the tunnel.
Should I have anything more there?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-12-2018 03:10 PM
Go to Network > IPSec Tunnels
In Status column of the tunnel you have "Tunnel Info"
Click on it.
While they ping does Pkt Decap counter increase?
If yes then you are receiving packets.
Have you overrided last 2 intrazone-default and interzone-default rules to log?
If yes do you see any sessions in Monitor > Traffic ?
Palo Alto Networks certified from 2011
- 1 accepted solution
- 30442 Views
- 23 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PAN-308564 Known Issue in Advanced SD-WAN for NGFW Discussions
- Unable to establish tunnel during Service Connection configuration (Details Added with Screenshot) in Prisma Access Discussions
- Request for Documentation on VPN and Routing Log Events in General Topics
- Dynamic IP at Spoke site in PAN-OS SD-WAN Hub/Spoke topology in Next-Generation Firewall Discussions
- On-Boarding of Cisco SDWAN to Prisma in Prisma Access Discussions