- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
NTP and proxy bypass
- LIVEcommunity
- Discussions
- General Topics
- NTP and proxy bypass
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
NTP and proxy bypass
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2017 02:50 PM
Hi i have a problem at the moment where it appears there is a proxy/Vpn application that is using port 123 .
as i have lots of byod devices that require access to NTP i leave the port open.
When I look at the monitor logs it source port can be anything from 123 to any other port and the dest port is 123 and P.A is letting me know the application is NTP , hence allowed
I have ssl decryption turned on .
i am slightly stuck on how i ca allow legitimate NTP traffic as opposed to vpn/proxy using port 123 ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2017 03:58 PM
Hello,
At this point it would be the application inspection. In your logs, filter by port 123 and see which applications are using that port. Then rewrite the rule to allow only NTP 'application' and remove the port 'Service'.
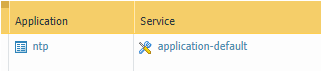
So the policy would look similar to:
If there is an app using ssl over port 123, you might need an additional policy to allow ssl over port 123.
I hope I understood your question correctly. Please let me know if I havent and i'll do my best to answer it correctly.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2017 12:57 AM
Hi @PaulBrock
Are you seeing the vpn/proxybypass be identified as NTP in the traffic logs, or are you seeing the vpn/pbp hit your NTP policy and be allowed by it?
in case of the latter, @OtakarKlier's solution will solve your issue. In case of the former you'll want to collect as much information as possible (pcaps, paket-diag log feature flow basic + appid basic) and open a support case
PANgurus - Strata & Prisma Access specialist
- 3140 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Unable to establish tunnel during Service Connection configuration (Details Added with Screenshot) in Prisma Access Discussions
- PA-415-5G not working with fresh T-Mobile SIM in General Topics
- GloablProtect + Explicit Proxy blocks WSL traffic. in GlobalProtect Discussions
- Palo Alto Unable to Download Software Updates in Next-Generation Firewall Discussions
- GRPC status UNAVAILABLE in intelligent offload in VM-Series in the Private Cloud