- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Outgoing Packet Capture To Tunnel
- LIVEcommunity
- Discussions
- General Topics
- Outgoing Packet Capture To Tunnel
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Outgoing Packet Capture To Tunnel
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-10-2013 07:26 PM
Hi all,
Is it possible to capture the traffic entering a vpn tunnel? Or can you only capture incoming traffic?
Cheers
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-10-2013 09:02 PM
Hi Agosney.
As per my knowledge, we cannot capture packet which is entering into a vpn tunnel. Also filters in PAN firewall will capture both way traffic (S to C and C to S) even though you will configure in one direction.
FYI: There is a way you can externally decrypt ESP packet and extracts the original pcap ( communication between two end point private subnet) )if you have 1) Pre-shared Key 2) IPsec parameters.
Example:How can I decrypt IKEv1 and/or ESP packets ? - Wireshark Q&A
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-11-2013 11:35 AM
Yes, we can capture the traffic entering a Vpn tunnel. But once captured we get to see the ESP packets and not any more details as they are encrypted as informed by Hulk.
We can use the filters and captures per the below doc,
https://live.paloaltonetworks.com/docs/DOC-2542
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-11-2013 04:27 PM
Thank you for your responses. I have read that document but I am still confused.
We have a tunnel to a 3rd party Cisco which is up and running but the traffic is not being received at the other end. How can I verify that the issue is at their end by confirming the traffic is leaving our end. We can see the incoming requests
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-11-2013 04:58 PM
Hi Agosney,
Please execute bellow mentioned command, if number of encapsulating bytes are increasing then firewall is sending packets out.
admin@DanPA1(active)> show vpn flow tunnel-id 5 | match bytes
encap bytes: 55006856
decap bytes: 45722708
You can find tunnel-ID from command "show vpn ipsec-sa" or "show vpn isa-sa", let me know if have difficulty with this.
Other option is to check Traffic log, if Egress interface is Tunnel interface then Firewall is certainly sending packets out.
Other option is to do flow basics on that particular traffic stream, it will show packet level debug. Which will provide if firewall is dropping any packets.
Packet Capture, Debug Flow-basic and Counter Commands
Regards,
Hardik Dinendra Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-11-2013 06:48 PM
Hello Agosney,
As per your last update, it's looking like IPSec tunnel is up but traffic is not passing through it.
A. Is traffic failing to pass in both or one direction?
To confirm which direction the traffic is failing, try pinging from a device on one LAN to the Trust interface of the other LAN. Example:
Using the drawing below, from device 192.168.10.10 ping 192.168.20.10:
Then do the same from a device on the other side of the tunnel; from 192.168.20.20 ping 192.168.10.10.

B. Is the next-hop for the route the correct tunnel interface?
C. Is there a policy that allows traffic to the zone where the tunnel interface exists?
Could you please verify below mentioned steps as well:
1. Please verify proxy ID's on both ends as SPI value will create on the basis of Proxy ID's. Make sure you have configured "private subnates" where from you are initiating traffics ( source as well as destination).
2. Take flow basic to track the return packet on the firewall.
3. Check the route to confirm that traffic is being pushed to the right tunnel interface.
4. Is there any device in front of CISCO or PAN firewall, which is doing NAT functionality. If so, please enable NAT-T on both end and test it once.
5. Go through the document Site-to-Site IPSec VPN Between Palo Alto Networks Firewall and Cisco Router using VTI Not Passing Tr... for any clue.
Thanks
Subhankar
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-11-2013 08:29 PM
Hi Hshah,
I ran the "show vpn flow tunnel-id" and the packets and bytes were 0 so it looks like the traffic isn't making it out.
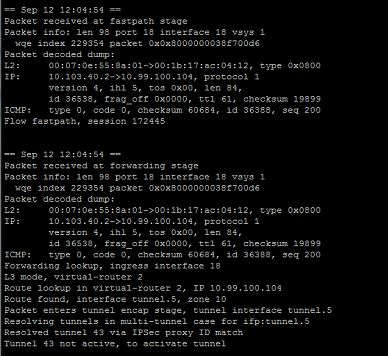
Here is a portion of the basic flow with the last 2 lines suggesting an error with proxy ID:
There is also the following repeating message in syslog:
IKE protocol notification message sent: NO PROPOSAL CHOSEN (14)
Hi Hulk,
I will look into your suggestions.
Cheers
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2013 07:25 AM
Hi Agosney,
I have a doubt phase-I or Phase-II may be down. If "show vpn flow tunnel-id" has encapsulated packets 0 means packets are not going out.
Please attach complete output for "flow basics" and ""show vpn flow tunnel-id"" along with "show vpn ike-sa"/"show vpn ipsec-sa".
Regards,
Hardik Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2013 01:00 PM
Hello Agosney,
Could you please confirm whether the IPSec tunnel is UP or not. Because mentioned 2 parameters 1. NO PROPOSAL CHOSEN 2. Proxy-ID is an essential parameter during tunnel establishment. (" Proposal" for both Phase 1 and 2 , proxy ID for Phase-2 negotiation).
Please apply below mentioned command and repeat every 10 seconds.
> test vpn ike-sa gateway XYZ
> test vpn ipsec-sa tunnel < tunnel name>
Capture the output and share with us.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-15-2013 08:17 PM
admin@pa-datacentre1> show vpn ike-sa
phase-1 SAs
GwID/client IP Peer-Address Gateway Name Role Mode Algorithm Established Expiration V ST Xt Phase2
--------------- ------------ ------------ ---- ---- --------- ----------- ---------- - -- -- ------
1 203.97.206.16 vpn-wellington Resp Main PSK/DH2/3DES/SHA1 Sep.16 08:47:42 Sep.16 16:47:42 v1 12 2 0
2 12.34.80.194 vpn-la Resp Main PSK/DH2/3DES/SHA1 Sep.16 12:51:35 Sep.16 20:51:35 v1 12 2 0
3 203.220.19.18 vpn-edge Init Main PSK/DH2/A256/SHA1 Sep.16 12:48:10 Sep.17 12:48:10 v1 12 3 38
Show IKEv1 IKE SA: Total 3 gateways found. 3 ike sa found.
phase-2 SAs
GwID/client IP Peer-Address Gateway Name Role Algorithm SPI(in) SPI(out) MsgID ST Xt
--------------- ------------ ------------ ---- --------- ------- -------- ----- -- --
1 203.97.206.16 vpn-wellington Init /tunl/ESP/3DES/SHA1 F0A14ED5 A2096317 6F8F0784 9 1
2 12.34.80.194 vpn-la Init /tunl/ESP/3DES/SHA1 FED5193F A179D123 DF25CC5E 9 1
3 203.220.19.18 vpn-edge Init / / / / 00000000 00000000 1DBCF6BE 5 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 D20088F4 00A6886E 52C2701E 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 BA4883A9 AFC99F71 1E5B5F53 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 9528665C 685C1AD3 47F57995 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 E279C9BC FFE5BEAA F1A7E1D6 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 CBD93CE9 34C8D1A8 DF0BBF8A 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 EC876237 140A4AD1 D2AA4A52 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 F0D70E27 B6516AC0 2DE56394 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 DAC18371 36E018D2 367D6000 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 8A49D309 56D1A552 6D097D14 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 FE78D28D D82B1B3E 3B803EDE 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 C2BB17F6 21122A80 A4B76EB9 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 9104EB4F 9DD3DA70 3CAC2222 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 C89E5A5A 4ED74F8D 25411B90 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 D64BB885 BB73D709 C0B51D37 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 A35445D9 223D4ADC A3F908C0 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 D5F80223 5B2F4AF4 79DE58F7 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 8126C837 1B364569 509D8648 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 A61C721B B0799B8D 45EFB3D4 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 E150FA69 58CA7D05 03FF6038 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 DE227759 A186021A 5F0AAB12 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 C17A6CCE E06B103E B12F0B76 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 8D179519 E52966D5 0D6EC957 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 9B14A1F7 68E63C13 31A5B050 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 E30BBD4F 2D15F335 ECBC8BAE 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 F668B7EA 3888BBFA 2C2F4E0E 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 DA737ECC 52F1D005 617F21D4 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 99A0CC75 35BFF829 DA6F10A3 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 9FAE763C BB4E170D 7583FDF6 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 CDB669C9 B3EB3AF8 A2E59E69 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 C2859446 250CD66D 2811E1F3 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 8E3CBDDE 3E4FD2BC 4AC2CE32 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 83BFBA70 795B41B1 441F4744 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 87213AB5 3D9F9CAF DCBE8046 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 BD70E616 65DCB18F 9774457B 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 F8C13DD8 24DE5AAF 2651FED9 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 A87D978F 4660AC81 0E4C1D27 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 AAB15287 18408D7F 5F165719 9 1
3 203.220.19.18 vpn-edge Init DH2 /tunl/ESP/3DES/MD5 BD5457D5 CF1E1E11 89E932A8 9 1
Show IKEv1 phase2 SA: Total 3 gateways found. 41 ike sa found.
admin@pa-datacentre1> show vpn ipsec-sa
GwID/client IP TnID Peer-Address Tunnel(Gateway) Algorithm SPI(in) SPI(out) life(Sec/KB)
--------------- ---- ------------ --------------- --------- ------- -------- ------------
1 3 203.97.206.16 tunnel-wellington(vpn-wellington) ESP/3DES/SHA1 F0A14ED5 A2096317 11684/0
2 4 12.34.80.194 tunnel-la(vpn-la) ESP/3DES/SHA1 FED5193F A179D123 11624/0
3 7 203.220.19.18 tunnel-edge:melton-1(vpn-edge) ESP/3DES/MD5 BD5457D5 CF1E1E11 28464/0
3 8 203.220.19.18 tunnel-edge:melton-2(vpn-edge) ESP/3DES/MD5 AAB15287 18408D7F 28464/0
3 9 203.220.19.18 tunnel-edge:Auburn-1(vpn-edge) ESP/3DES/MD5 A87D978F 4660AC81 28464/0
3 10 203.220.19.18 tunnel-edge:Auburn-2(vpn-edge) ESP/3DES/MD5 F8C13DD8 24DE5AAF 28464/0
3 11 203.220.19.18 tunnel-edge:Belmont-1(vpn-edge) ESP/3DES/MD5 BD70E616 65DCB18F 28464/0
3 12 203.220.19.18 tunnel-edge:Belmont-2(vpn-edge) ESP/3DES/MD5 87213AB5 3D9F9CAF 28464/0
3 13 203.220.19.18 tunnel-edge:Bundaberg-1(vpn-edge) ESP/3DES/MD5 83BFBA70 795B41B1 28464/0
3 14 203.220.19.18 tunnel-edge:Bundabert-2(vpn-edge) ESP/3DES/MD5 8E3CBDDE 3E4FD2BC 28464/0
3 15 203.220.19.18 tunnel-edge:Charlestown-1(vpn-edge) ESP/3DES/MD5 C2859446 250CD66D 28464/0
3 16 203.220.19.18 tunnel-edge:Charlestown-2(vpn-edge) ESP/3DES/MD5 CDB669C9 B3EB3AF8 28464/0
3 17 203.220.19.18 tunnel-edge:ChrinsidePark-1(vpn-edge) ESP/3DES/MD5 9FAE763C BB4E170D 28464/0
3 18 203.220.19.18 tunnel-edge:ChrinsidePark-2(vpn-edge) ESP/3DES/MD5 99A0CC75 35BFF829 28464/0
3 19 203.220.19.18 tunnel-edge:Dandenong-1(vpn-edge) ESP/3DES/MD5 DA737ECC 52F1D005 28464/0
3 20 203.220.19.18 tunnel-edge:Dandenong-2(vpn-edge) ESP/3DES/MD5 F668B7EA 3888BBFA 28464/0
3 21 203.220.19.18 tunnel-edge:Dubbo-1(vpn-edge) ESP/3DES/MD5 E30BBD4F 2D15F335 28464/0
3 22 203.220.19.18 tunnel-edge:Dubbo-2(vpn-edge) ESP/3DES/MD5 9B14A1F7 68E63C13 28464/0
3 23 203.220.19.18 tunnel-edge:Elizabeth-1(vpn-edge) ESP/3DES/MD5 8D179519 E52966D5 28464/0
3 24 203.220.19.18 tunnel-edge:Elizabeth-2(vpn-edge) ESP/3DES/MD5 C17A6CCE E06B103E 28464/0
3 25 203.220.19.18 tunnel-edge:Epping-1(vpn-edge) ESP/3DES/MD5 DE227759 A186021A 28464/0
3 26 203.220.19.18 tunnel-edge:Epping-2(vpn-edge) ESP/3DES/MD5 E150FA69 58CA7D05 28464/0
3 27 203.220.19.18 tunnel-edge:HarbourTown-1(vpn-edge) ESP/3DES/MD5 A61C721B B0799B8D 28464/0
3 28 203.220.19.18 tunnel-edge:HarbourTown-2(vpn-edge) ESP/3DES/MD5 8126C837 1B364569 28464/0
3 29 203.220.19.18 tunnel-edge:Maitland-1(vpn-edge) ESP/3DES/MD5 D5F80223 5B2F4AF4 28464/0
3 30 203.220.19.18 tunnel-edge:Maitland-2(vpn-edge) ESP/3DES/MD5 A35445D9 223D4ADC 28464/0
3 31 203.220.19.18 tunnel-edge:Mandurah-1(vpn-edge) ESP/3DES/MD5 D64BB885 BB73D709 28464/0
3 32 203.220.19.18 tunnel-edge:Mandurah-2(vpn-edge) ESP/3DES/MD5 C89E5A5A 4ED74F8D 28464/0
3 33 203.220.19.18 tunnel-edge:Redbank-1(vpn-edge) ESP/3DES/MD5 9104EB4F 9DD3DA70 28464/0
3 34 203.220.19.18 tunnel-edge:Redbank-2(vpn-edge) ESP/3DES/MD5 C2BB17F6 21122A80 28464/0
3 35 203.220.19.18 tunnel-edge:Rhodes-1(vpn-edge) ESP/3DES/MD5 FE78D28D D82B1B3E 28464/0
3 36 203.220.19.18 tunnel-edge:Rhodes-2(vpn-edge) ESP/3DES/MD5 8A49D309 56D1A552 28464/0
3 37 203.220.19.18 tunnel-edge:RouseHill-1(vpn-edge) ESP/3DES/MD5 DAC18371 36E018D2 28464/0
3 38 203.220.19.18 tunnel-edge:RouseHill-2(vpn-edge) ESP/3DES/MD5 F0D70E27 B6516AC0 28464/0
3 39 203.220.19.18 tunnel-edge:Sunbury-1(vpn-edge) ESP/3DES/MD5 EC876237 140A4AD1 28464/0
3 40 203.220.19.18 tunnel-edge:Sunbury-2(vpn-edge) ESP/3DES/MD5 CBD93CE9 34C8D1A8 28464/0
3 41 203.220.19.18 tunnel-edge:Townsville-1(vpn-edge) ESP/3DES/MD5 E279C9BC FFE5BEAA 28464/0
3 42 203.220.19.18 tunnel-edge:Townsville-2(vpn-edge) ESP/3DES/MD5 9528665C 685C1AD3 28464/0
3 45 203.220.19.18 tunnel-edge:WestLakes-1(vpn-edge) ESP/3DES/MD5 BA4883A9 AFC99F71 28464/0
3 46 203.220.19.18 tunnel-edge:WestLakes-2(vpn-edge) ESP/3DES/MD5 D20088F4 00A6886E 28464/0
Show IPSec SA: Total 42 tunnels found. 40 ipsec sa found.
admin@pa-datacentre1> show vpn flow tunnel-id 7
tunnel tunnel-edge:melton-1
id: 7
type: IPSec
gateway id: 3
local ip: 202.59.229.114
peer ip: 203.220.19.18
inner interface: tunnel.5
outer interface: ethernet1/2
state: active
session: 227770
tunnel mtu: 1436
lifetime remain: 28261 sec
latest rekey: 539 seconds ago
monitor: off
monitor packets seen: 0
monitor packets reply: 0
en/decap context: 282
local spi: BD5457D5
remote spi: CF1E1E11
key type: auto key
protocol: ESP
auth algorithm: MD5
enc algorithm: 3DES
proxy-id local ip: 10.103.40.0/24
proxy-id remote ip: 10.99.100.0/24
proxy-id protocol: 0
proxy-id local port: 0
proxy-id remote port: 0
anti replay check: yes
copy tos: no
authentication errors: 0
decryption errors: 0
inner packet warnings: 0
replay packets: 0
packets received
when lifetime expired:0
when lifesize expired:0
sending sequence: 0
receive sequence: 537
encap packets: 0
decap packets: 23064
encap bytes: 0
decap bytes: 2398608
key acquire requests: 0
== Sep 16 13:00:06 ==
Packet received at ingress stage
Packet info: len 98 port 4 interface 260 vsys 1
wqe index 229004 packet 0x0x8000000038fdc8c6
Packet decoded dump:
L2: 00:1b:90:34:e9:5b->00:1b:17:ac:04:11, type 0x0800
IP: 10.99.100.104->10.103.40.2, protocol 1
version 4, ihl 5, tos 0x00, len 84,
id 0, frag_off 0x4000, ttl 64, checksum 39285
ICMP: type 8, code 0, checksum 43635, id 19539, seq 4114
Tunnel inbound. Protocol is ICMP, intercept it
Flow lookup, key word0 0x4c531012000a0100 word1 0
No active flow found, enqueue to create session
== Sep 16 13:00:06 ==
Packet received at slowpath stage
Packet info: len 98 port 4 interface 260 vsys 1
wqe index 229004 packet 0x0x8000000038fdc8c6
Packet decoded dump:
L2: 00:1b:90:34:e9:5b->00:1b:17:ac:04:11, type 0x0800
IP: 10.99.100.104->10.103.40.2, protocol 1
version 4, ihl 5, tos 0x00, len 84,
id 0, frag_off 0x4000, ttl 64, checksum 39285
ICMP: type 8, code 0, checksum 43635, id 19539, seq 4114
Session setup: vsys 1
PBF lookup (vsys 1) with application ping
Session setup: ingress interface tunnel.5 egress interface ethernet1/3 (zone 1)
Policy lookup, matched rule index 5
DoS policy lookup, no rule matched, let pkt go
DP0 is selected to process this session.
Allocated new session 210695.
Created session, enqueue to install
== Sep 16 13:00:06 ==
Packet received at fastpath stage
Packet info: len 98 port 4 interface 260 vsys 1
wqe index 229004 packet 0x0x8000000038fdc8c6
Packet decoded dump:
L2: 00:1b:90:34:e9:5b->00:1b:17:ac:04:11, type 0x0800
IP: 10.99.100.104->10.103.40.2, protocol 1
version 4, ihl 5, tos 0x00, len 84,
id 0, frag_off 0x4000, ttl 64, checksum 39285
ICMP: type 8, code 0, checksum 43635, id 19539, seq 4114
Flow fastpath, session 210695
== Sep 16 13:00:06 ==
Packet received at forwarding stage
Packet info: len 98 port 4 interface 260 vsys 1
wqe index 229143 packet 0x0x8000000038fdc8c6
Packet decoded dump:
L2: 00:1b:90:34:e9:5b->00:1b:17:ac:04:11, type 0x0800
IP: 10.99.100.104->10.103.40.2, protocol 1
version 4, ihl 5, tos 0x00, len 84,
id 0, frag_off 0x4000, ttl 64, checksum 39285
ICMP: type 8, code 0, checksum 43635, id 19539, seq 4114
Forwarding lookup, ingress interface 260
L3 mode, virtual-router 2
Route lookup in virtual-router 2, IP 10.103.40.2
Route found, interface ethernet1/3, zone 1, nexthop 10.200.200.254
Resolve ARP for IP 10.200.200.254 on interface ethernet1/3
ARP entry found on interface 18
Transmit packet on port 18
== Sep 16 13:00:06 ==
Packet received at fastpath stage
Packet info: len 98 port 18 interface 18 vsys 1
wqe index 229143 packet 0x0x8000000038f2e8d6
Packet decoded dump:
L2: 00:07:0e:55:8a:01->00:1b:17:ac:04:12, type 0x0800
IP: 10.103.40.2->10.99.100.104, protocol 1
version 4, ihl 5, tos 0x00, len 84,
id 38968, frag_off 0x0000, ttl 61, checksum 17469
ICMP: type 0, code 0, checksum 45683, id 19539, seq 4114
Flow fastpath, session 210695
== Sep 16 13:00:06 ==
Packet received at forwarding stage
Packet info: len 98 port 18 interface 18 vsys 1
wqe index 229143 packet 0x0x8000000038f2e8d6
Packet decoded dump:
L2: 00:07:0e:55:8a:01->00:1b:17:ac:04:12, type 0x0800
IP: 10.103.40.2->10.99.100.104, protocol 1
version 4, ihl 5, tos 0x00, len 84,
id 38968, frag_off 0x0000, ttl 61, checksum 17469
ICMP: type 0, code 0, checksum 45683, id 19539, seq 4114
Forwarding lookup, ingress interface 18
L3 mode, virtual-router 2
Route lookup in virtual-router 2, IP 10.99.100.104
Route found, interface tunnel.5, zone 10
Packet enters tunnel encap stage, tunnel interface tunnel.5
Resolving tunnels in multi-tunnel case for ifp:tunnel.5
Resolved tunnel 43 via IPSec proxy ID match
Tunnel 43 not active, to activate tunnel
admin@pa-datacentre1> test vpn ike-sa gateway
vpn-edge vpn-edge
vpn-la vpn-la
vpn-wellington vpn-wellington
<value> test for given IKE gateway
admin@pa-datacentre1> test vpn ike-sa gateway
vpn-edge vpn-edge
vpn-la vpn-la
vpn-wellington vpn-wellington
<value> test for given IKE gateway
admin@pa-datacentre1> test vpn ike-sa gateway vpn-edge
Initiate IKE SA: Total 1 gateways found. 1 ike sa found.
admin@pa-datacentre1> test vpn ipsec-sa tunnel
tunnel-edge tunnel-edge
tunnel-la tunnel-la
tunnel-wellington tunnel-wellington
<value> test for given VPN tunnel
admin@pa-datacentre1> test vpn ipsec-sa tunnel tunnel-edge
Initiate IPSec SA: Total 40 tunnels found. 40 ipsec sa found.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2013 05:54 PM
Hello,
It will be better to open a case with PAN support and share the case ID here. We will discuss this issue more in details and ensure that everything is running smoothly at your site, and, minimize any business impact, the problem caused.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2013 09:27 PM
Thanks for your update. The return packet has been received by the firewall but unfortunately getting dropped due to error " no active tunnel found".
Packet enters tunnel encap stage, tunnel interface tunnel.x
Resolving tunnels in multi-tunnel case for ifp:tunnel.x
Resolved tunnel AB via IPSec proxy ID match
Tunnel AB not active, to activate tunnel >>>>>>>>>>>>>>>> point of failure.
Looking like a bug in a previous version, I have updated the same information into the case as well.
Please upload the tech-support file for further analysis.
Thanks
- 14154 Views
- 12 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- IPSEC to Azure establish but cannot use traceroute in General Topics
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- S2S between PA3250 and Azure VPN Gateway -1 way traffic in Next-Generation Firewall Discussions
- IPSec VPN not getting any response from peer in General Topics
- Byte swapping needed on packet captures taken from tunnel interfaces in Next-Generation Firewall Discussions




