- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
PA sending TCP RST for a NAT rule
- LIVEcommunity
- Discussions
- General Topics
- Re: PA sending TCP RST for a NAT rule
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-20-2020 03:26 AM
Hi everybody,
Adding a bidirectionnal NAT rule for an ssl web server and the according security rule, connections from outside are dropped as "Incomplete". Traffic capture show that first SYN packet received is directly rejected by PA with a RST response. What does it mean ?
Regards.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-22-2020 03:37 AM
Hi,
Thank you very much for your advice on NAT rules.
After another check of our configuration, it seems that another host in the same NML subnet not crossing the Palo appliance was using the same IP address ... Everything works as expected now, sorry for the time spent on this obvious problem.
Rodjeur68
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-20-2020 04:33 AM
As session is incomplete, there is no response/reply from destination end.
Please check few configurations like,
1. Routing for destination server
2. If service is up and running on the server.
Mayur
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-20-2020 04:54 AM
Thx for the response.
* There's no routing issue: server can access Internet via the PA using the NAT IP address
* service is up and running, accessible from internal networks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-20-2020 05:27 AM
Are you seeing issues with inbound or outbound traffic?
Mayur
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-20-2020 05:35 AM
Globally ? Not at all.
Rodjeur68
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-20-2020 08:43 AM - edited 04-20-2020 08:47 AM
Is it possible to share traffic logs for affected traffic? Also is it app-id based security policy ?
As you said in your post, you have bi-directional NAT and you are facing issues with connections from outside on one ssl web server. You are trying to externalize web-server probably on 443 port. As session is seems to be incomplete, just check if web-service is running on server that you want to externalize. Check if you are able to telnet internal server on web-service port from LAN. As you are seeing incomplete session, most of the time it happens when there is no response from the server. That's why i asked to check reverse routing for web server subnet on firewall and application running status on web server.
Mayur
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-20-2020 10:51 AM
Agreed with @SutareMayur .
Most of the time session shows incomplete when there is no reply back from server side. Routing issues mostly causes this.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-21-2020 01:23 AM
Hi everybody,
Thanks for your time. As I mentionned in a previous post, I think we don't have any issue with routing and service is up and running:
* I can ping server from appliance
* show routing route gives a correct route for my internal subnet
* from server, I'm able to browse Internet using the external NAT IP choosen for service
* from internals subnets, I can access the https service on the server (nginx)
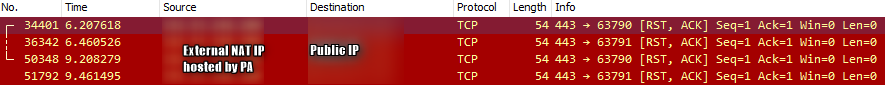
When I capture the traffic I can see RST tcp packet immediatly send by PA on external interface and nothing on the internal interface.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-21-2020 08:16 PM
It is always safer to create 2 NAT policies for DNAT and SNAT than bi-direcitonal.
If you check bi-directional NAT rule in cli you can see that for DNAT source zone will be "any".
For your TCP RST problem. Most likely your security policy is incorrect.
Are you using pre-nat IP and post-nat zone in security policy?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-22-2020 03:37 AM
Hi,
Thank you very much for your advice on NAT rules.
After another check of our configuration, it seems that another host in the same NML subnet not crossing the Palo appliance was using the same IP address ... Everything works as expected now, sorry for the time spent on this obvious problem.
Rodjeur68
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-13-2020 01:06 PM
Hi, can you elaborate a little more about the "It is always safer to create 2 NAT policies for DNAT and SNAT than bi-direcitonal"
I do have most of mine NAT rule is currently provisioned bi-directional and we are seeing issue with client server session reset. So, I searched and see this thread but do not understand about the statement you metioned. Thanks much for your help and if you could help and give a sample practical NAT rule using two separates policies instead of one as you said.
- 1 accepted solution
- 9982 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Crowdstrike Integration to XSIAM in Cortex XSIAM Discussions
- XSIAM Analytics rules Dashboard in Cortex XSIAM Discussions
- Cannot add BIOC rule to restriction profiles in Cortex XDR Discussions
- Cortex XDR MITRE ATT&CK v16 -- We're Now on v19. Can We Talk About This? in Cortex XDR Discussions
- Quarantined Files not appearing in Action Center in Cortex XDR Discussions