- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
PAN-OS and Global Protect software
- LIVEcommunity
- Discussions
- General Topics
- PAN-OS and Global Protect software
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2015 12:44 PM
There is a change in the default behaviour in the global protect from 2.3.0
In Global protect 2.2 and previous version if the Trust CA is configured in the Portal then only the agent will validate the gateway certificate.
From agent 2.3 the agent will always check the validity of the gateway server certificate and if the agent cannot validate the certificate, it will not connect to the GlobalProtect gateway.
Validate means whether the certificate is signed by a CA which is trusted by that machine.
Other thing is If the CN of certificate have IP address then it should match to the IP address of the interface used in the portal. If the CN is domain name then the IP it resolves to should match to the IP address of the interface used in portal.
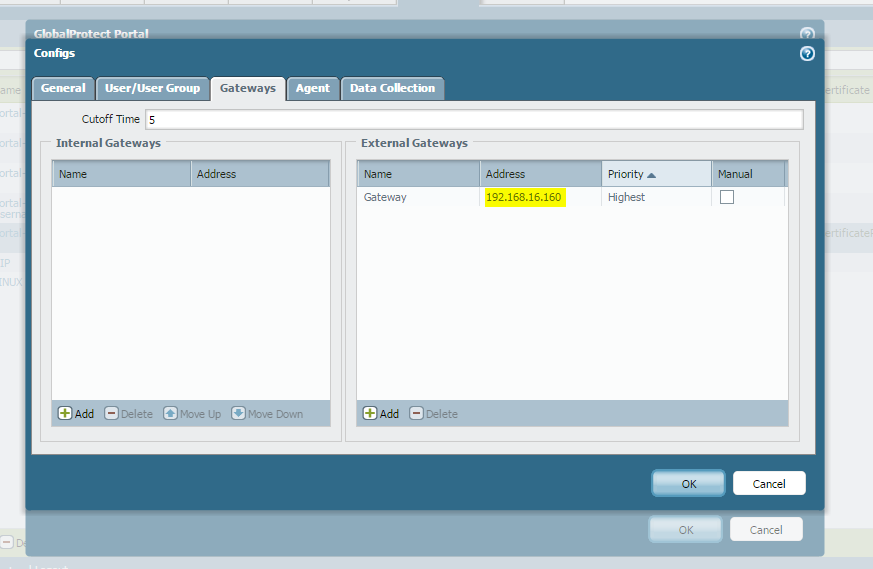
When defining the gateways (External/Internal) under the portal configuraiton. If CN have FQDN then specify the FQDN, If CN have IP address then specify IP address.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2015 02:27 PM
Thank you for that.
How doe sthis apply to a wildcard cert?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2015 12:46 AM
Hi,
If you really need GP, it can be interesting for you to upgrade to V7. In this release, licence had been simplify.
According the VY RN: "You can now use GlobalProtect to provide a secure, remote access or virtual private network (VPN) solution via single or multiple external gateways, without any GlobalProtect licenses. The portal license, which was required to enable this functionality, has been deprecated. However, advanced features including Host Information Profile (HIP) checks and support for the GlobalProtect mobile app for iOS and Android still require a gateway subscription. To take advantage of the new license structure, you need to upgrade only the device running the GlobalProtect portal to PAN-OS 7.0 or later."
We are in 7.0.2 and everything works well 🙂
Hope help.
V.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2015 02:11 AM
If you are using a certifiacte signed by a trusted CA so you don't have to worry about it.
Just take care of the following part
If the CN of certificate have IP address then it should match to the IP address of the interface used in the portal. If the CN is domain name then the IP it resolves to should match to the IP address of the interface used in portal.
When defining the gateways (External/Internal) under the portal configuraiton. If CN have FQDN then specify the FQDN, If CN have IP address then specify IP address.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2015 12:05 PM
Thanks, V., but PA tech support didn't sound as convincing as you ;^).
I'll consider... perhaps there are others seeing this who share your experience? (holla!)
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2015 12:10 PM
Forgive my limited knowlegde of certs, Pakumar. Are you saying that the GP config on the remote device should match what is on the cert?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2015 12:19 PM
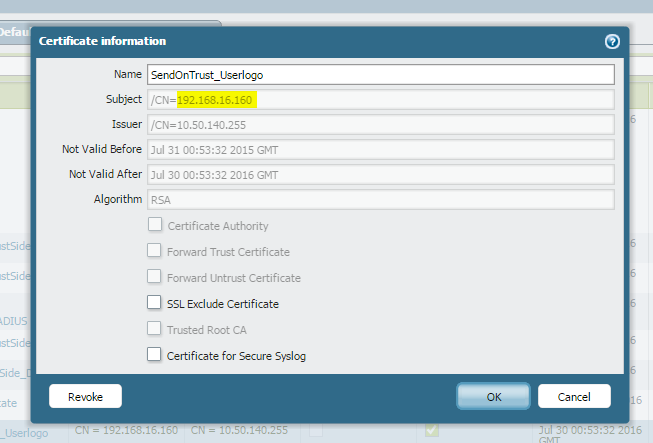
Check the highlihted area the CN name is a IP address so in the portal config I have sepecified IP address for gateway.
If thhe CN is vpn.abc.com then I have to specify vpn.abc.com in the portal config for gateway.
and the nslookup for vpn.abc.com should map to the IP address that you are using for portal.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2015 01:48 PM
crystal clear! thanks....
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-12-2015 01:08 PM
A note to all - the upgrade to 6.1.6 only worked on one of my 2 PA-5020s. The dataplane kept crashing on my primary (Dataplane is down: too many dataplane processes exited). has anyone experienced similar? Rebooting with the interfaces disconnected (all except managment and HA) did not solve.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-13-2015 01:17 PM
Try to upgrade to 6.1.7 where multiple dataplane restart issues were solved
Check the release notes for the following IDs and try to match them with your enviroment,
80720
82370
80251
79719
76875
66681
If that doesn't solve your issue, opean a TAC case,
Regards,
Gerardo.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-14-2021 10:01 PM
Hi Team,
I am facing the same issue, I have global protect installed, the version is 5.2.8-23, on the gateway i am using FQDN.
when i try to connect GP i am getting the error "the certificate is not signed by a trusted certificate authority". if i install the root certificate on the local machine, it works fine. but I am not doing any certificate based authentication. Could you please tell me is it mandatory to install the root certificate on all the end machines to connect global protect.?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-15-2021 08:22 AM
Hi @CHANDRASHEKHAR.BRAMAPRAKASH ,
When you configure GlobalProtect Portal and Gateway, you need to assign SSL certificate that firewall will provide as server certificate when connecting to GP. It looks like you are using certificate that is self-signed or signed by internal PKI, that is not trusted by default. You have few options:
- Request SSL server certificate from public Certificate Authority.
- If you are using self-signed server certificate you must install the root CA (that was used to generate the server cert) to each machined that will connect to GP
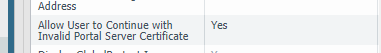
- Strongly against this option, but if you still want to use self-signed certificate, without installing the root CA - there is an option to ignore the invalid SSL certificate and continue with vpn connection. This is under GP portal -> Agent Config -> App
I would recommend to use this option only in test/PoC environment, because it will completely bypass certificate validation, which is only protection agains man-in-the-middle attack
- 16662 Views
- 12 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- I'd like to download global protect 6.2.6-838 in General Topics
- MacOSX Tahoe 26.4.1 (25E253) / Global Protect 6.3.3: Network is unreachable in GlobalProtect Discussions
- failure to connect in GlobalProtect Discussions
- Global Protect is having issues with newer MACOS version. in Next-Generation Firewall Discussions
- connecting to global protect in GlobalProtect Discussions