- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
SSL Decryption: ERR_HTTP2_INADEQUATE_TRANSPORT_SECURITY
- LIVEcommunity
- Discussions
- General Topics
- Re: SSL Decryption: ERR_HTTP2_INADEQUATE_TRANSPORT_SECURITY
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
SSL Decryption: ERR_HTTP2_INADEQUATE_TRANSPORT_SECURITY
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-13-2020 02:48 AM
Hi paloalto community,
we're currently still testing ssl decryption and discovered a new error, which I can't google to find a solution.
If we're visiting the following site, we get an "ERR_HTTP2_INADEQUATE_TRANSPORT_SECURITY" error. Site: https://www.1erforum.de/
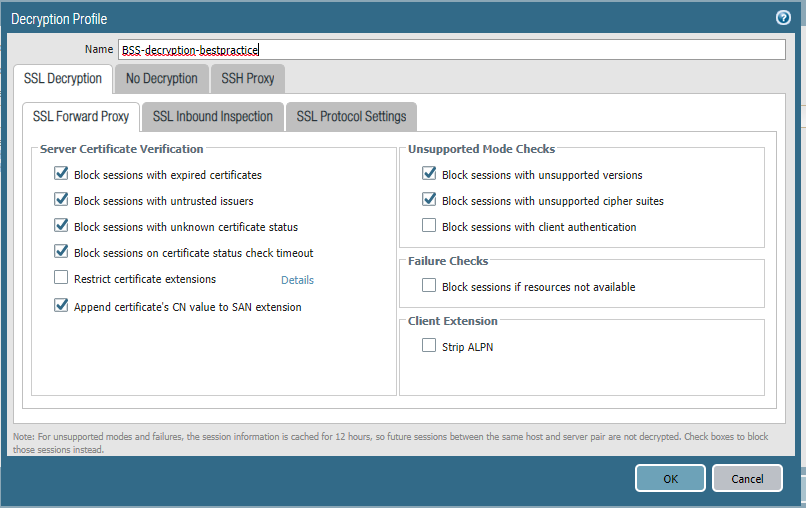
See attached our configuration and ssl information without decryption enabled.
Firmware and Specs:
PA 850 - FW 9.0.5
Settings:
Decryption disabled:
Decryption enabled:
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2020 10:58 PM
Same issue for us also ....
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-06-2021 04:33 PM
This is what we also did. So far, just a handful of sites. As somebody else pointed out, this article is helpful https://tools.ietf.org/html/rfc7540
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-23-2021 01:24 AM
Same issue here with this URL
PA 220 and 3220 with PanOS 9.1.8 ... any solution ???
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-23-2021 01:28 PM
For quick tls checks I often use https://www.ssllabs.com/ssltest/ .
So far I have seen the error in this topic only with servers that do not have a preference with the configured ciphersuites - like this webserver https://svp.protectionone.de/ . The tls 1.2 ciphersuites look like this on ssllabs:
So as far as I know when a browser connects directly to such a webserver it chooses the strongest ciphersuites. When paloalto connects to this webserver with tls1.2 (as 9.1 does not support tls1.3) I assume the order of ciphersuites that the firewall sends to the server is not "correct" for h/2. This means that the order in the client hello probably has not the stronges ones in the first places but then the first one is chosen from that client hello and this one is one of them which are not allowed for h/2. With servers that have a preference, they almost always prefer the strongest ones so the order in the client hello does not matter and the decryption works properly without this error.
With tls1.3 (supported in PAN-OS 10) the situation changes completely as there weak ciphers aren't even part of the specs. So when viewing again this example webserver, with tls1.3 it supports these ciphersuites:
The server still has no preference for the ciphersuites, but as all 3 of them are allowed for h/2 this isn't an issue when decrypting the connection with PAN-OS 10.
So as far as I see it, the solution would be to change the order of ciphersuites in the client hello and this problem would be gone in PAN-OS 9.1 ...
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-27-2021 04:58 PM
I have fixed this for some sites by removing SHA1 from the allowed auth algorithms.
Not exhaustively tested but works so far!
- 65127 Views
- 36 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- SSL certificate has expired end date after PA decryption in General Topics
- Multi-VSYS 11.2.8 - How to assign a dedicated Forward Trust Certificate per VSYS for SSL Decryption in Next-Generation Firewall Discussions
- Foward Trust Cert and MacBook Pro in General Topics
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- Decryption policies and Short-Lived Certificates in Next-Generation Firewall Discussions