- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Suggestions for Splunk Search/Report
- LIVEcommunity
- Discussions
- General Topics
- Suggestions for Splunk Search/Report
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Suggestions for Splunk Search/Report
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-23-2018 06:37 AM
I have several Splunk searches that I use as indicator lists. Has someone already built a miner/prototype to retrieve these?
The generic API examples don't seem sufficient for Splunk's two-step routine (search then retrieve results).
https://docs.splunk.com/Documentation/Splunk/latest/Search/ExportdatausingRESTAPI
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-23-2018 08:17 PM - edited 12-25-2018 12:55 PM
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-11-2022 02:12 PM
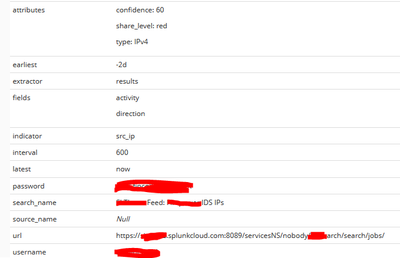
Thank you @Hugh.Kelley for creating this Miner. I'm in a similar situation on trying to ingest a saved search from our Cloud Splunk instance that we are using as a "known" blocklist which is being curated by our SOC. I'm running into a little bit of a challenge when running hte miner. It appears to fun successfully but does not seem to be pulling back any indicators. In looking at the miner configuration I didn't see a place for the "saved_serach" entry and added a variable to the configuration called saved_search. Was wondering if you would be able to provide any insight as to what I may be doing incorrectly.
age_out:
default: 7d
interval: 600
sudden_death: true
attributes:
confidence: 60
share_level: green
type: IPv4
extractor: results
fields: entity
password: <password>
prefix: None
search_name: <search_name>
url: https://<host>.splunkcloud.com:8089/services/search/jobs
username: <username>
verify_cert: false
also tried with "https://xxx.splunkcloud.com:8089/servicesNS/nobody/<APP_NAME>/search/jobs/"
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-14-2022 06:18 PM
@Joel_Fostano , it has been a few years so I've forgotten the details, but my prototype looks like yours:
It pulls the search_name setting the same way it gets the time settings (line 21 at URL below)
If you look in the _internal index of Splunk, do you see any evidence of a search?
- 5267 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cortex XDR and splunk logging in Cortex XDR Discussions
- PA 445 setup in Next-Generation Firewall Discussions
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- Regarding the issue of prohibiting the use of developer tools in Prisma Browser in Prisma Access Browser (PAB) Discussions
- Continuous Threat Logs Showing Management Server IP as Source in Next-Generation Firewall Discussions