- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Traps local analysis behavior
- LIVEcommunity
- Discussions
- General Topics
- Traps local analysis behavior
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Traps local analysis behavior
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2017 02:43 AM - edited 09-25-2017 02:46 AM
Hi,
Last week we had a problem with TRAPS. We have ESM in the cloud, and we have traps agents in diferente sites. One of these sites had a problem with the internet, so traps could not contact the cloud. The case is that we have executables that traps detect as viruses and that we allowed, so once that agent could not contact with the cloud eliminated these executables. It seems like local analysis it detects the virus and it eliminates the executables.
How local analysis works? I thought that local analysis kept signatures in case it could not contact the cloud
Thanks a a lot
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2017 05:47 AM
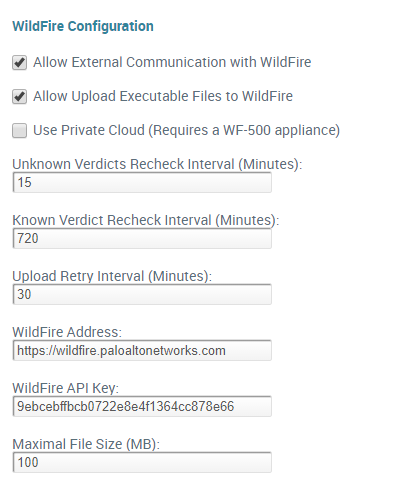
Can you verify that the effected users had actually already tried to launch these executables prior to being unable to reach the ESM? If they hadn't then this kind of makes sense and you should investigate the 'ESM Unreachable' options available within the WildFire policies tab.
If the agents didn't already lookup the verdict for that file and have it within their cache, the file would have simply done local analysis and took any action that it's told to take. With the ESM not being reachable the agent doesn't have any idea that you have 'whitelisted' these executables unless the verdict already exists in the agent cache. I'm also not positive if this cache is maintained during a restart.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2017 06:33 AM - edited 09-25-2017 06:33 AM
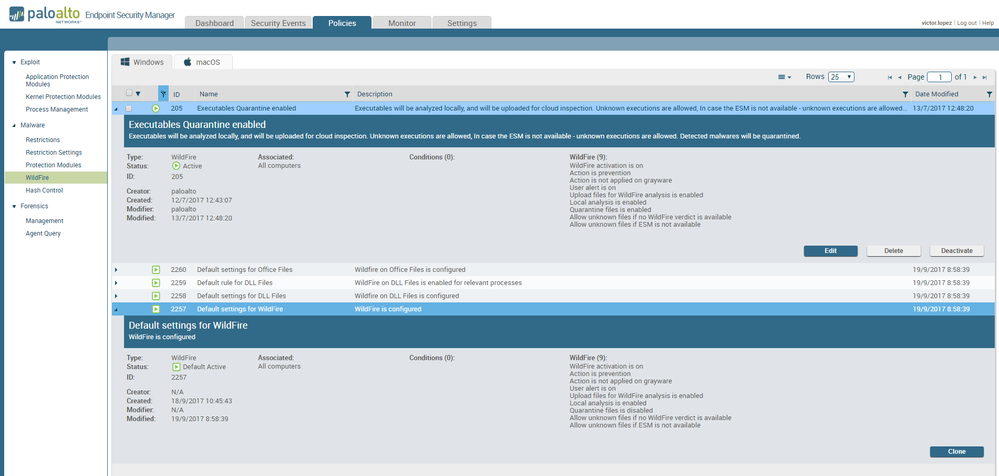
Yes, i confirm that affected users had launched these executables before. i attach a screenshot with Widlfire tab
any recommendation?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2017 11:07 AM
What version of Traps are you running?
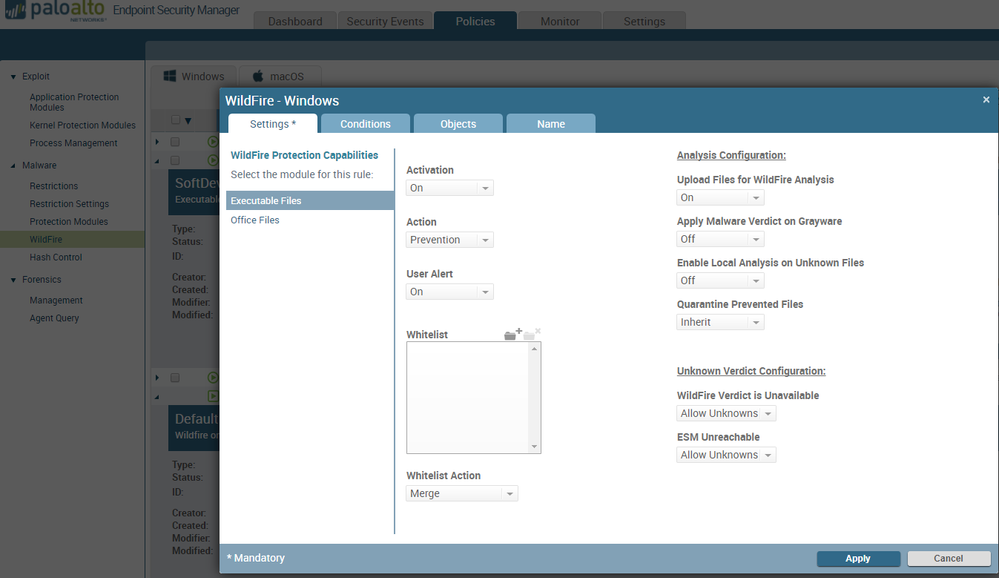
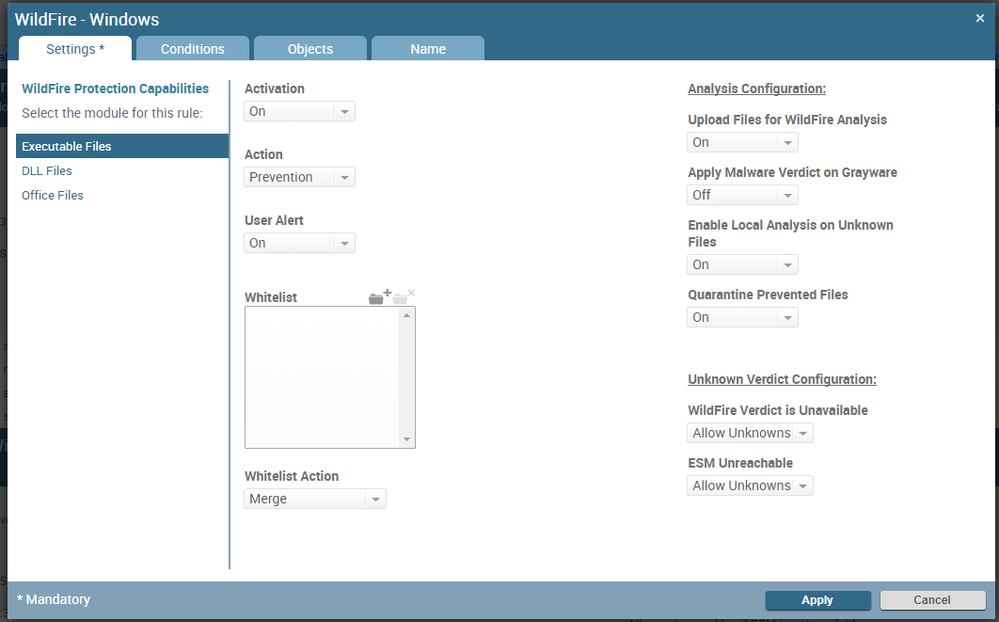
The setting that I'm talking about is actually located under the Policies tab, under the Malware section click on WildFire. The listed policies there if you click on edit on one of them it should show 'Unknown Verdict Configuration' with two options for 'WildFire Verdict is Unavailable' along with 'ESM Unreachable' like the picture below. What exactly does it show there.
If it quarantined the file I'm guessing that your 'Quarantine Prevented Files' option is currently set to On.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2017 06:30 AM
hi,
version is 4.0.4. These are the screenshots:
thanks a lot for your help
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2017 11:18 AM
So this is what I think happened.
The file wasn't in the agent cache for whatever reason; either it hadn't been opened before, the computer was restarted and the cache cleared, or the cache cleared because the user had opened enough files that the cache removed the existing verdict override cache entry to make room for additional cache information. Without knowing how long the outage is and how many files were scanned that's almost impossible to know for sure.
You have local analysis turned on for unknown files which in my mind is 'good' but you also have unreachable options set to allow unknown files. As soon as local analysis kicks in and classifies something, the file is no longer unknown. The file is known with whatever verdict the local analysis engine gives it.
Really I think it is a combination of things. The cache likely got cleared or overwritten due to one of the reasons above, and the local analysis paired with the unreachable options means that, to the best of my knowledge, you are never actually hitting those options. The file doesn't stay in an unknown state after local analysis and therefore it's following whatever the local analysis says to do with the file.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2017 11:40 PM
Perfect. Thanks a lot for your findings. Any advice in order to prevent this another time???? This problem occurred to one whole site (site with internet outage), not just one device?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2017 06:36 AM
If this is just a set of executables I would include them in the Executable Files Whitelist. This makes it so that the agent itself knows that you've whitelisted the executable and you won't have to worry about the file getting a malicious verdict. If you simply have a verdict override and you lose the connection to the ESM you are relying on the cache entry being present on the agent; if you switch any verdict override for specified executables to this whitelist then the agent doesn't have to rely on connection to the ESM or having the cache entry.
- 5208 Views
- 7 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- How to add exception for known macros detection by cortex XDR in Cortex XDR Discussions
- False positive - Wise Care 365 in VirusTotal
- [SOLVED] Panorama's SAML-Based Administrator Cannot See Other Administrators And Generate TSFs in Panorama Discussions
- Prisma Access Explicit Proxy — Anti‑Spyware behavior when DNS bypasses Prisma (logging subtype + test methodology) in Prisma Access Discussions
- Palo Alto for email security in Next-Generation Firewall Discussions