- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
VLAN entry
- LIVEcommunity
- Discussions
- General Topics
- VLAN entry
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
VLAN entry
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2020 01:12 PM
Hi
I have a network with IP addresses in the range of 192.168.100 and 192.168.130 on two singular network cards on the same machine on the local network. Port 4 on the firewall is plugged into another device with the .130 range IP. Port 1 on the firewall is plugged into the local network. I can’t contact the other device from the machine.
Any idea how I can achieve this?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2020 03:10 PM
Hello,
I think your enviroment like this;
To Check-
- İnterface types should be L3 and ip address assigned.
- Same default router shoul be used.
- Else you must crate a routing entry for each subnet in each VR.
- You can put them in different zone or same zone up to you.
- İf different zone, you have to create a rule.
- İf same zone Default allow rule will allow traffic.
- İf there is clean up rule before default rules, a permit rule must be created even if they are in same zone.
- İf there is an allow rule logging should be enabled.
- Link States must be Green not red or greyed out.
- Assingnin a ping enabled management profile to interface’s good for trouble shooting.
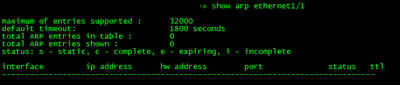
- ON cli you can check arp entry’s to verify hosts are connected properly.
- )> show arp ethernet1/1 or )> show arp ethernet1/4
- If you are using VM Palo Alto, “promiscous mode” has to be enabled all interface’s. İn ESX.
- For 100.0 network host can ping to its gateway.
- For 130.0 network host can ping to its gateway.
- Trace route can be helpful.
Have a nice and healty day.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-05-2020 12:08 AM
If i read your issue correctly you have:
a desktop computer with 2 network cards plugged in, one in range 192.168.100 and one in 192.168.130
your firewall also has 2 connected interfaces, one in 192.168.100 and one in 192.168.130
your desktop is connected with both interfaces in the same broadcast domain to the firewall on the interface with ip 192.168.100
the firewall is connected to a different broadcast domain on the 192.168.130 interface
i don't think there is a (layer3) solution to this issue as your host will always prefer the locally connected subnet over a remotely routed one so it will look for ARP rather than route
you could consider switching your firewall to two layer2 interfaces, and setting up routed vlan interfaces in each subnet
that way both broadcast domains will see eachother and a default gateway will remain available for routing
PANgurus - Strata & Prisma Access specialist
- 3353 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Windows ARP Issue - Windows Hosts Not Installing ARP info in Next-Generation Firewall Discussions
- EDL Capacity Reached but Lists Show Empty / Default Entry (0.0.0.0/32) – Panorama Multi-VSYS Setup Post: in General Topics
- traffic disruption on routing change in Next-Generation Firewall Discussions
- VPN peer ID in Next-Generation Firewall Discussions
- How to add Wildcard Domains as a destination for Firewall policy PA1420 in General Topics