- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Global Protect authentication happened twice while LDAP and Okta Auth
- LIVEcommunity
- Discussions
- Network Security
- GlobalProtect Discussions
- Re: Global Protect authentication happened twice while LDAP and Okta Auth
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Global Protect authentication happened twice while LDAP and Okta Auth
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2023 10:22 AM
Recently we moved to PA-3410 software version 11.0.1-h2 from PA-850 software version 10.2.3-h4 .
on both firewalls
| GlobalProtect Agent | 6.1.1 |
We have selected option for authentication override
On Portals
Generate cookie for authentication override
on Gateway
Accept cookie for authentication override
https://supportcases.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000boODCAY
It was working perfectly fine with single okta prompt on PA-850 but after moving onto the PA-3410 GP okta auth prompts twice.
As PAN TAC has suggested cleared GP and Laptop web browser cache.
1. Try clearing the Browser cache and Cache file by referring below document.
https://live.paloaltonetworks.com/t5/globalprotect-discussions/clearing-globalprotect-cookies/td-p/3...
2. How to uninstall GlobalProtect Agent software completely in Windows
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA14u000000oNGHCA2
Uninstall the GlobalProtect App for macOS
https://docs.paloaltonetworks.com/globalprotect/5-2/globalprotect-app-user-guide/globalprotect-app-f...
3. Form the firewall, there is a method to clear the cache of GlobalProtect for Connected users by imposing the below commands. (This might prevent you from uninstalling it on each user if it works).
> show global-protect-gateway current-user (To check connected users)
> clear user-cache all type GP ( To delete the cache for connected users).
After doing everything above mentioned, still GP Okta auth prompts twice. is there anyone have solutions and suggestion for this issue?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2023 10:58 AM
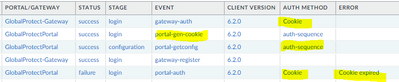
Monitor > Logs > GlobalProtect
Filter:
( eventid eq 'portal-auth' ) or ( eventid eq 'gateway-auth' )
Add "Auth Method" and "Error" columns.
What auth methods and errors you see?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2023 11:53 AM - edited 09-25-2023 11:54 AM
Example:
Client connects to portal.
Tries cookie.
Cookie is expired so uses "auth-sequence" to log in.
Portal generates new cookie for user.
Login to gateway uses new cookie and succeeds.
Your log screenshot don't reveal what is happening on your side during same process.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-25-2023 11:17 PM
I think it is better for you to go back to TAC with this info - user is not in allowlist when using cookies and let them figure out.
Without seeing more details it is hard to troubleshoot further.
You can try to set allowlist to "all" under auth profile (Device > Authentication Profile > Auth-Profile-Name > Advanced tab) and test if it starts working and go from there.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2023 08:30 PM
Hi Raido_Rattameister,
Thank you for your prompt replies and suggestions.
Its was working perfectly fine , when we upgraded PA-3410 from
| Software Version | 10.2.3-h4 |
to
| Software Version | 11.0.1-h2 |
PAN TAC came back with answer " Its KNOWN Bug on this Software Version 11.0.1-h2". They asked us to test the below scenario
1. Remove generate cookie from the portal.
2. Generate and accept cookies at the gateway only.
The above scenario will trigger the SAML redirect during the first login and from 2nd login, it will trigger a redirect to SAML only for the portal and the gateway will login as per cookie. After changing above suggested options it started working with single SAML Okta auth prompt but its temporary workaround. They are working on permanent hotfix solution on this version. I will keep updated here.
- 6387 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- [SOLVED] - NGFW The Connection To Global Protect On The IPads Times Out!! in GlobalProtect Discussions
- SAML Authentication with Shibboleth error : idp has no assertion in GlobalProtect Discussions
- Cannot Access Global Protect Portal in Next-Generation Firewall Discussions
- Packaging Global Protect in GlobalProtect Discussions
- Azure Virtual Desktops integration with Global Protect nightmare in GlobalProtect Discussions