- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Global Protect mixed internal and external gateway
- LIVEcommunity
- Discussions
- Network Security
- GlobalProtect Discussions
- Global Protect mixed internal and external gateway
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-01-2022 11:24 PM
hi everybody, i've some questions regarding global protect client and mixed environment internal / external
we have a internal campus networking infrastructure with lan and wlan (2 different subnets), so the laptop changes the ip-address if traveling around the campus, wired or unwired...
so we have installed global protect client for internal use without tunnel mode for user-id through palo firewall for internet access...this seems to work..
but now:
users want to connect with global protect from external to campus network, external access is planed with multi-factor-auth
via radius config in global protect
now i've tried several things:
2 portal-config setups (internal and external) because we need 2 different connect methods for global protect
- on demand with mfa via radius-auth (if user connects external)
- always on with ldap-auth (if user is on campus network)
and 2 gateway-config setups
- tunnel mode (if user connects external)
- no mode (if user is on campus network)
is this setup recommended?
or what would be best practise?
1 portal and mfa internal + external?
i've seen some strange behaviour with mixed portal config...sometimes client does not connect internal when last connection was external...
maybe someone can help me....
regards, fabian
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2022 07:04 AM
Hi @Land-Salzburg ,
You need to use one GP portal agent config with both the internal and external gateways configured, and the priority of the external gateway should be "Manual only".
Your GP client is always selecting the external gateway because you configured it to do so with the 1st agent config. Multiple agent configs only work if the OS and/or users are different.
With regard to mixed authentication methods for the portal and gateway, I have done that before. What version of PAN-OS do you have? What is your disconnect message?
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-11-2022 01:04 PM
for those who have the same problem:
portal with 2fa and gateway with 2fa:
if using panos 10.1.2 >> pls upgrade
PAN-177119 | Fixed an issue with the GlobalProtect gateway where SMS-message-based multi-factor authentication (MFA) did not display a prompt to enter the authentication code. |
that fixed my radius-troubles on gateway authentication
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-02-2022 10:04 AM - edited 03-02-2022 10:05 AM
Hi @Land-Salzburg ,
This document describes almost exactly what you are trying to do -> https://docs.paloaltonetworks.com/globalprotect/10-0/globalprotect-admin/globalprotect-quick-configs....
Let me highlight the main points:
- Only 1 portal is needed. It is a separate appliance in the diagram, but all portals and gateways can be on a single NGFW.
- Two gateways are used, internal and external.
- The client uses Internal Host Detection to determine whether to connect to the internal or external gateway (2nd sentence).
- The 1st note block says that the internal connections can be always-on while the external gateway can be on-demand.
You can have the portal and internal gateway authenticate with LDAP and the external gateway authenticates via RADIUS w/MFA. Assuming that the LDAP and RADIUS user/pass is the same, the authentication should be seamless with 1 MFA prompt for the external gateway.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2022 12:51 AM - edited 03-03-2022 09:13 AM
hi tom, thanks for your answers
i've already seen this diagramm / howto
nevertheless: i've some more questions:
one ngfw and i've made one portal:
first question: my dns-records (internal and official / external)
should these be the same fqdn?
- vpn.abc.com (resolves to external official ip if laptop is out of campus)
- vpn.abc.com (resolves to internal private ip if laptop is onsite)
next question: different agent config on portal configuration?
- network -- global protect -- portals -- myportal
- tab agent >>>>
- do i insert 2 agent configs and how do they differ ? where to set host detection and where not?
- where to set internal gw / external gw and where not?
- tab agent >>>>
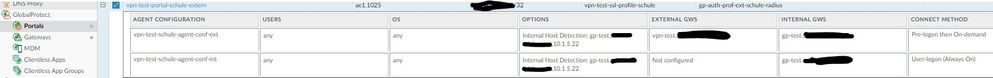
i've made a screenshot of current portal config..
with this single portal config the gp-client internal says: global protect portal does not exists...so i need 2 portals or not?
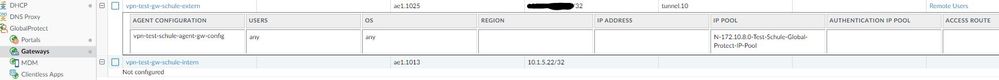
the gateways are here:
radius and ldap-server use same user-credentials, radius was only configured for mfa
maybe you can give me some advice
regards, fabian
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2022 03:41 PM - edited 03-03-2022 04:00 PM
Hi @Land-Salzburg ,
- The DNS records should be the same. Both should resolve to the public IP of the portal. The portal is configured for that IP address only, otherwise you will get the "portal does not exist" error.
- The portal agent configuration should be always-on. Under the Network > GlobalProtect > Portals > <portal-config> > Agent > <agent-config> > External tab, change the priority of your gateway to "Manual only". The doc does not tell you how to do this. This prevents the client from automatically connecting to the external gateway.
- Internal Host Detection is setup under the Network > GlobalProtect > Portals > <portal-config> > Agent > <agent-config> > Internal tab. You can click the ? button in the upper right of the box for instructions.
- The doc uses different DNS names for the 2 gateways. That is a good idea. The external gateway is configured on the external IP address, and the internal gateway is configured on the internal IP address. The DNS records should match what you configure in the portal.
I think I answered all of your questions. 🙂
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2022 10:08 PM - edited 03-04-2022 06:33 AM
hi tom, thanks for your answers
so i set 2 agent-configs on the portal
- agent-conf-external -- with option internal host detection, set ip addresses for internal and external gateway and method "on-demand"
- agent-conf-internal -- with option internal host detection, set ip addresses for internal and external gateway and method "always-on"
i've also made 2 gateways internal and external
- gw-external -- with mfa-auth and tunnel mode
- gw-internal -- with ldap and NO tunnel setting
now an interesting thing:
laptop onsite of campus: global-protect-client connects to portal, enter credentials and after that enables and establish and ipsec-tunnel...
and some other problem: radius-auth on gateway without radius-auth on portal does not work, agent keeps disconnected...
it seems the gp-agent does not recognize internal use...how can i debug this? what could be possible wrong?
regards, fabian
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2022 07:04 AM
Hi @Land-Salzburg ,
You need to use one GP portal agent config with both the internal and external gateways configured, and the priority of the external gateway should be "Manual only".
Your GP client is always selecting the external gateway because you configured it to do so with the 1st agent config. Multiple agent configs only work if the OS and/or users are different.
With regard to mixed authentication methods for the portal and gateway, I have done that before. What version of PAN-OS do you have? What is your disconnect message?
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2022 07:53 AM
hi tom,
thanks for your support....I'm not inconveniencing you, I hope, seems a difficult topic to me...
well maybe my mistake: i thought it needs 2 agent configs on the single-portal,
1st config for internal always-on
and
2nd config for external on-demand
i'll change the single-portal --> agent config to 1 config with internal and external gateways set and internal host detection activated..
i wasn't aware of the the function portal-config --> agent-config --> external gateway --> source region any and priority manual setting
mfa-topic:
current pan-os: 10.1.2
current gpa: 5.2.10
behaviour: agent connects --> enter user and pwd --> enter pin-code --> nothing happens....agent keeps trying to connect, but no
logging even in the agent-debug log....
strange...
regards, fabian
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2022 07:57 AM
Thanks @Land-Salzburg !
What do the logs say on the MFA side?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2022 08:22 AM
hi tom,
i can deliver the logs on monday, out of office now..
regards, fabian
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-11-2022 01:04 PM
for those who have the same problem:
portal with 2fa and gateway with 2fa:
if using panos 10.1.2 >> pls upgrade
PAN-177119 | Fixed an issue with the GlobalProtect gateway where SMS-message-based multi-factor authentication (MFA) did not display a prompt to enter the authentication code. |
that fixed my radius-troubles on gateway authentication
- 2 accepted solutions
- 12336 Views
- 9 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Is the unified RPC interface (MonitorDirect.enqueueLogRequest) supported for external use? in Next-Generation Firewall Discussions
- How to make Router BGP ping into IP inside Palo Alto in Next-Generation Firewall Discussions
- Palo Alto Global Protect clients failing to connect intermittently in GlobalProtect Discussions
- GlobalProtect 6.1.11-175 Connection Issues in GlobalProtect Discussions
- Disconnect Internally but not remotely in GlobalProtect Discussions