- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
DNS-base application
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- Re: DNS-base application
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-07-2022 05:36 PM
Hi ALL,
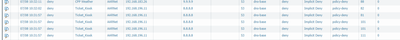
In our monitor log ,we see a lot of deny for a few PCs with "dns-base" application .
Please see below:
what is "DNS-base" and how do we allow it if needed.
Thanks
QL
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-10-2022 05:31 PM
We allow "DNS" and port TCP 53 & UPD 53 in the security rule but user still complain not working.
we change the rule for "any" service and it is working for them now.
Thank you for the insight knowledge.
Much appreciated
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-07-2022 06:46 PM - edited 07-08-2022 02:31 PM
"dns-base" is one of the subsets of the "dns" application ID. The "dns" application ID is currently being split into to separate subcategories so those who want can filter non-compliant DNS requests:
dns-base: general DNS requests
dns-non-rfc: Non-RFC complaint DNS requests
You can see the descriptions of these application IDs on your PaloAlto under:
Objects -> Applications -> search "dns" and then click the dns application names
dns-non-rfc was introduced June 21 2022 and is scheduled for activation July 19 2022. You can read more here:
If your current Security Policies allow application ID "dns", that will include both subsets. If you only want to allow RFC compliant DNS traffic, then your Security Policy should only allow "dns-base" (non-RFC compliant will be excluded after July 19).
Since your current Security Policy set is denying DNS traffic, I would start looking at your current rule to allow "dns" or "dns-base". Is it applied to the correct zones, source/destination addresses, and using "application default" or "any" Service?
IMPORTANT EDIT: Re-reading the enhancement release now, there are recent comments that people using "dns" application ID had their Security Policy broken, they had to explicitly add the subset "dns-base" to get DNS working again. See this follow up article with release information:
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-10-2022 05:31 PM
We allow "DNS" and port TCP 53 & UPD 53 in the security rule but user still complain not working.
we change the rule for "any" service and it is working for them now.
Thank you for the insight knowledge.
Much appreciated
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-20-2022 08:11 AM
I have come across the same issue. Even if you have the "DNS" application allowed, even though the dns-base is listed as a subset, it will get dropped. I had to allow both "DNS" & "DNS-BASE" and my domain authentication and lookups started to work properly again.
- 1 accepted solution
- 16241 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect is having issues with newer MACOS version. in Next-Generation Firewall Discussions
- Unable to find "Hide My IP" application on firewall (Applipedia shows it exists in Next-Generation Firewall Discussions
- Conflict between Global Protect and RedSky MyE911 application in GlobalProtect Discussions
- Potential False Positive IoC in GlobalProtect Discussions
- Issues with credit card processing terminals in Next-Generation Firewall Discussions