- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Incidents contain many alert types... but why?
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- Incidents contain many alert types... but why?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Incidents contain many alert types... but why?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2023 10:35 AM
Hello, everyone. Our product suite now includes receiving alerts from the NGFW, in addition to XDR. It seems, though, that a single incident may include several different alerts. This seems like a strange behavior, because the list of alerts come from many hosts, or threat type, or threat vector. If the Incidents are grouping unrelated alerts, we'd like to understand why.
I have one particular incident which is composed of seven wholly different alerts, and they're all being sent from the NGFW. It would seem more sensible that there would be seven different incidents which match the alerts.
I welcome your replies!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2023 06:27 AM
Hi @Eric_Geater ,
Cortex XDR console should never group unrelated alerts in the same incident. There will always be some common artifact between the alerts in order for the console to put them under the same incident. I don't believe Palo Alto are officially sharing the complete logic of alert grouping, but if you look at the documentation you can see that there are multiple factors:
"The logic behind which alert the Cortex XDR app assigns to an incident is based on a set of rules which take into account different attributes. Examples of alert attributes include alert source, type, and time period. The app extracts a set of artifacts related to the threat event, listed in each alert, and compares it with the artifacts appearing in existing alerts in the system. Alerts on the same causality chain are grouped with the same incident if an open incident already exists. Otherwise, the new incoming alert will create a new incident."
In my experience when comes to Incidents/Alerts from PAN FW usually they are:
- Same public source triggering different threat log
- Same destination targeted by different sources triggering different threat log
- and of course different addresses triggering same threat log.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2023 05:36 AM
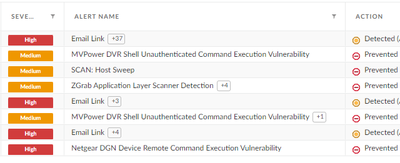
This may serve as a good example of a single alert we've received. I'm not saying all alerts look like this, because many do not. But when they do, well... it's interesting to parse. You hope that the bulk of detail is "false positive" or "other" in your resolution.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-09-2023 01:45 PM
Hi @Eric_Geater ,
Looking at the Alert names it looks like those are triggered by Inbound traffic - public addresses trying to connect to your public resources behind the FW. My guess is the XDR is grouping all of them in the same incident either because they are targeting the same destination IP, or are sourced from the same external IP or both (both).
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-26-2023 04:31 AM
Are all Alerts present within Incidents?
- 3863 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Is the unified RPC interface (MonitorDirect.enqueueLogRequest) supported for external use? in Next-Generation Firewall Discussions
- SCM Device Restart Incidents — False Positive Notification in Strata Cloud Manager
- Storage type of PA-520, PA-545-POE, PA-550, PA-555-POE in Next-Generation Firewall Discussions
- Which AWS Instance Type Meets VM-300 Requirements? Documentation Seems Inconsistent in VM-Series in the Public Cloud
- Palo alto type of license subscription in Next-Generation Firewall Discussions