- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
AWS Transit Gateway
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- AWS Transit Gateway
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
AWS Transit Gateway
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-04-2019 10:28 AM
Hello,
Is there planned AWS Transit Gateway integration? There is mention but no detail in this video:
https://www.youtube.com/watch?v=6fhwoAwYrug
Other than operational ease, the Transit Gateway advantages appear limited. Traffic between VPCs is not encrypted. VPC segmentation is via routing and does not traverse a firewall.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-04-2019 10:37 AM
Yes, we announced our intentions here.
You can build it out manually today, it works and has been tested internally. We will be releasing additional documentation and templates soon.
I would recommend reaching out to your account team for additional information.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-07-2019 07:11 AM
Thanks @jmeurer.
Is there an ETA on the documentation?
I've asked our SE for more details.
@jmeurer wrote:Yes, we announced our intentions here.
You can build it out manually today, it works and has been tested internally. We will be releasing additional documentation and templates soon.
I would recommend reaching out to your account team for additional information.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-09-2019 06:10 PM - edited 03-09-2019 06:10 PM
Hi @jmeurer
Any updates on the documentation? I'm interested in securing traffic flowing Inbound, East/West and Outbound with VPC insertion and VPN insertion. Particulary interested in taking advantage of ECMP VPN to connect the VM_SERIES to the TG. Any documentation would be greatly appreciated.
Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-09-2019 06:53 PM
Here is some information on Transit Gateway manual deployment as well as a YAML template for automated deployments. Hope this helps.
https://github.com/PaloAltoNetworks/TransitGatewayDeployment
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-11-2019 01:11 PM
Hi @jperry1 ,
My concern with this design is the VPC attachment from TGW SN to the TGW. Rather than using ECMP VPN links 'that I have been unable to find documentation on', the data sent across that connection will be in the clear; right?
What are your thoughts on that?
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-06-2020 06:21 PM
Fantastic documentation here in the manual build https://github.com/PaloAltoNetworks/TransitGatewayDeployment, I think you left out one thing. A need to add default route on FW2 pointing to eth1, otherwise the outbound traffic will be dropped by the firewall.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-10-2020 12:39 PM
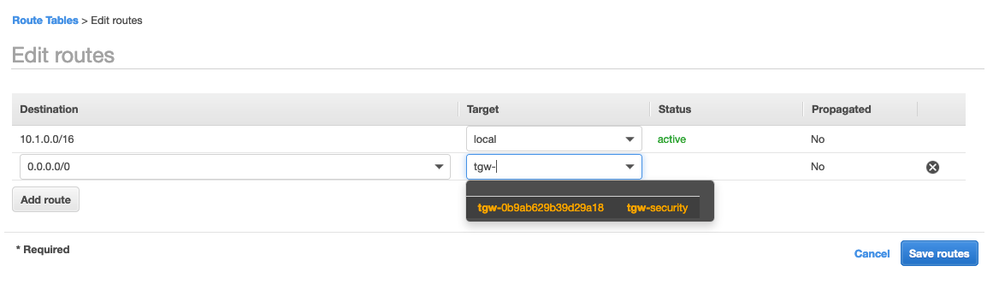
I am on my third or fourth attempt to walk through the Manual build guide and every time I reach Page 22, step 8, the TGW Attachment "attach-spoke1" is not available as a target. Only the tgw-security gateway.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-10-2020 12:44 PM
Please switch the deployment guide and reference architecture here.
https://www.paloaltonetworks.com/resources/reference-architectures/aws
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-10-2020 01:08 PM
Hi @DewhirstR ,
Hope all is well and you get this worked out.
Take a look at page 13-15 and verify the VPC attachments for both spokes to the TGW. Verify Associations in the TGW Route Table for the VPCs.
- 16013 Views
- 9 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect, same IP pool with 2 gateways on a firewall in GlobalProtect Discussions
- How does the Azure Virtual Network discovers that there is Palo Alto Gateway Interface in VM-Series in the Public Cloud
- PA Global Protect in GlobalProtect Discussions
- Adding PA DR site globalprotect SSL-VPN gateway in GlobalProtect Discussions
- Unable to reach Palo Alto - Global Protect Portal. in GlobalProtect Discussions