- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Site to Site VPN IPsec b/w Palo Alto and Cisco with only public IP as Mgmt interface on Azure
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- Re: Site to Site VPN IPsec b/w Palo Alto and Cisco with only public IP as Mgmt interface on Azure
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Site to Site VPN IPsec b/w Palo Alto and Cisco with only public IP as Mgmt interface on Azure
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2017 01:16 PM
Hi Experts,
wanclouds@panvwanclouds> show config running
config {
mgt-config {
users {
admin {
phash *;
permissions {
role-based {
superuser yes;
}
}
}
wanclouds {
phash $1$buaddxeg$F9xAm862FkTC869HKCU1e1;
permissions {
role-based {
superuser yes;
}
}
}
}
}
shared {
application;
application-group;
service;
service-group;
botnet {
configuration {
http {
dynamic-dns {
enabled yes;
threshold 5;
}
malware-sites {
enabled yes;
threshold 5;
}
recent-domains {
enabled yes;
threshold 5;
}
ip-domains {
enabled yes;
threshold 10;
}
executables-from-unknown-sites {
enabled yes;
threshold 5;
}
}
other-applications {
irc yes;
}
unknown-applications {
unknown-tcp {
destinations-per-hour 10;
sessions-per-hour 10;
session-length {
maximum-bytes 100;
minimum-bytes 50;
}
}
unknown-udp {
destinations-per-hour 10;
sessions-per-hour 10;
session-length {
maximum-bytes 100;
minimum-bytes 50;
}
}
}
}
report {
topn 100;
scheduled yes;
}
}
}
devices {
localhost.localdomain {
network {
interface {
ethernet {
ethernet1/1 {
layer3 {
ipv6 {
neighbor-discovery {
router-advertisement {
enable no;
}
}
}
ndp-proxy {
enabled no;
}
ip {
}
lldp {
enable no;
}
}
}
ethernet1/2 {
layer3 {
ipv6 {
neighbor-discovery {
router-advertisement {
enable no;
}
}
}
ndp-proxy {
enabled no;
}
lldp {
enable no;
}
ip {
}
}
}
}
tunnel {
units {
tunnel.1 {
comment ipsec-s-s;
}
}
}
}
profiles {
monitor-profile {
default {
interval 3;
threshold 5;
action wait-recover;
}
}
}
ike {
crypto-profiles {
ike-crypto-profiles {
default {
encryption [ 3des aes-128-cbc];
hash sha1;
dh-group group2;
lifetime {
hours 8;
}
}
Suite-B-GCM-128 {
encryption aes-128-cbc;
hash sha256;
dh-group group19;
lifetime {
hours 8;
}
}
Suite-B-GCM-256 {
encryption aes-256-cbc;
hash sha384;
dh-group group20;
lifetime {
hours 8;
}
}
}
ipsec-crypto-profiles {
default {
esp {
encryption [ 3des aes-128-cbc];
authentication sha1;
}
dh-group group2;
lifetime {
hours 1;
}
}
Suite-B-GCM-128 {
esp {
encryption aes-128-gcm;
authentication none;
}
dh-group group19;
lifetime {
hours 1;
}
}
Suite-B-GCM-256 {
esp {
encryption aes-256-gcm;
authentication none;
}
dh-group group20;
lifetime {
hours 1;
}
}
}
global-protect-app-crypto-profiles {
default {
encryption aes-128-cbc;
authentication sha1;
}
}
}
gateway {
ike-peer-csr {
authentication {
pre-shared-key {
key -AQ==KUGt+eZobgDsoMJzqj4Pf48NH0w=SFAlEHCj9+AttIUAYLgRUA==;
}
}
protocol {
ikev1 {
dpd {
enable yes;
}
}
ikev2 {
dpd {
enable yes;
}
}
}
protocol-common {
nat-traversal {
enable yes;
}
fragmentation {
enable no;
}
}
local-address {
interface ethernet1/1;
ip 10.0.1.4/24;
}
peer-address {
ip 52.34.x.x;
}
local-id {
id 10.0.0.4;
type ipaddr;
}
peer-id {
id 172.31.16.49;
type ipaddr;
}
}
}
}
qos {
profile {
default {
class {
class1 {
priority real-time;
}
class2 {
priority high;
}
class3 {
priority high;
}
class4 {
priority medium;
}
class5 {
priority medium;
}
class6 {
priority low;
}
class7 {
priority low;
}
class8 {
priority low;
}
}
}
}
}
virtual-router {
default {
protocol {
bgp {
enable no;
dampening-profile {
default {
cutoff 1.25;
reuse 0.5;
max-hold-time 900;
decay-half-life-reachable 300;
decay-half-life-unreachable 900;
enable yes;
}
}
routing-options {
graceful-restart {
enable yes;
}
}
}
}
ecmp {
algorithm {
ip-modulo;
}
}
interface [ ethernet1/1 ethernet1/2 tunnel.1];
routing-table {
ip {
static-route {
CSR-AWS-SYED {
path-monitor {
enable no;
failure-condition any;
hold-time 2;
}
bfd {
profile None;
}
interface tunnel.1;
metric 10;
destination 192.168.2.0/24;
route-table {
unicast;
}
}
}
}
}
}
}
tunnel {
ipsec {
ipsec-tunnel-1 {
auto-key {
ike-gateway {
ike-peer-csr;
}
proxy-id {
local-remote-subnet {
protocol {
any;
}
local 10.0.2.0/24;
remote 192.168.2.0/24;
}
}
}
tunnel-monitor {
enable no;
}
tunnel-interface tunnel.1;
}
}
}
}
deviceconfig {
system {
type {
dhcp-client {
send-hostname yes;
send-client-id no;
accept-dhcp-hostname no;
accept-dhcp-domain no;
}
}
update-server updates.paloaltonetworks.com;
update-schedule {
threats {
recurring {
weekly {
day-of-week wednesday;
at 01:02;
action download-only;
}
}
}
}
timezone US/Pacific;
service {
disable-telnet yes;
disable-http yes;
}
ip-address 10.0.0.4;
hostname panvwanclouds;
netmask 255.255.255.0;
default-gateway 10.0.0.1;
dns-setting {
servers {
primary 168.63.129.16;
}
}
}
setting {
config {
rematch yes;
}
management {
hostname-type-in-syslog FQDN;
initcfg {
type {
dhcp-client {
send-hostname yes;
send-client-id no;
accept-dhcp-hostname no;
accept-dhcp-domain no;
}
}
ip-address 10.0.0.4;
netmask 255.255.255.0;
default-gateway 10.0.0.1;
dns-primary 168.63.129.16;
username wanclouds;
hostname panvwanclouds;
}
}
}
}
vsys {
vsys1 {
application;
application-group;
zone {
untrust {
network {
layer3 [ ethernet1/2 tunnel.1 ethernet1/1];
}
}
trust {
network {
layer3;
}
}
}
service;
service-group;
schedule;
rulebase {
nat {
rules;
}
security {
rules {
ANY {
to any;
from any;
source any;
destination any;
source-user any;
category any;
application any;
service application-default;
hip-profiles any;
action allow;
}
}
}
}
import {
network {
interface [ ethernet1/1 ethernet1/2 tunnel.1];
}
}
}
}
}
}
}
wanclouds@panvwanclouds>
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-27-2017 09:14 AM
Hello @faizullah,
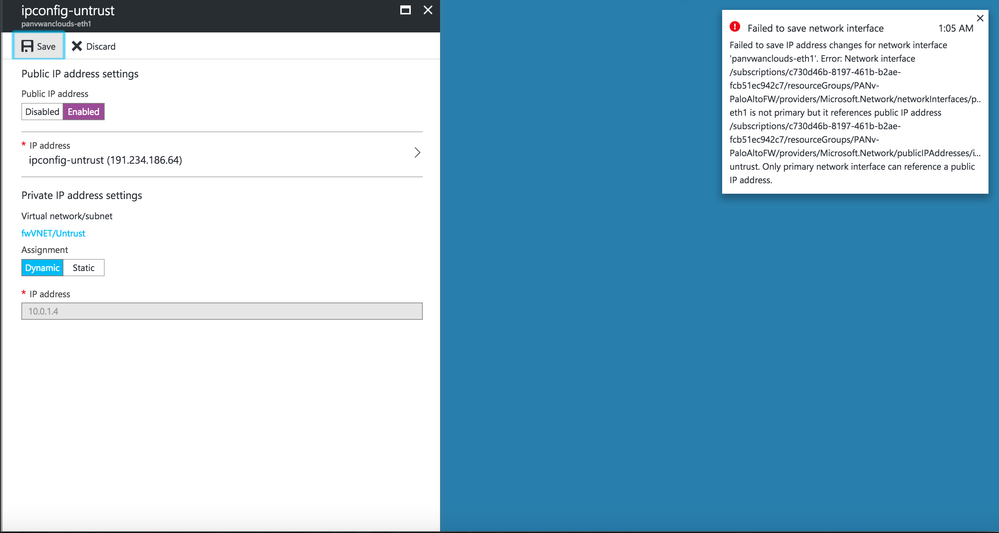
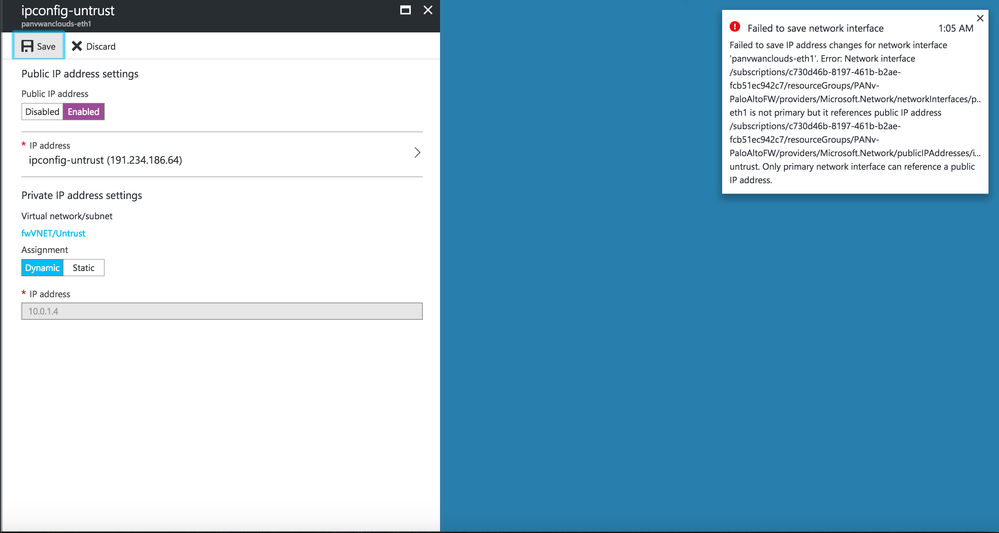
Your image is not uploaded properly. Please, can you repost it again? l am sure we can figure it out
Thx,
Myky
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-27-2017 11:30 AM
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-27-2017 01:38 PM
Thanks MyKy for looking into it please let me know if u need anything else , the only use case i want to understand here how we can configure Site-to-Site IPsec VPN b/w Palo Alto Device hosted in Azure cloud with only public IP on Mgmt Interface with ASAv hosted on Azure or AWS as ASAv honors use of MGMT interface as local address or source interface in S-S ipsec vpn.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-28-2017 12:48 AM - edited 02-28-2017 01:03 AM
Hello @faizullah,
As far as l am aware MGMT interface it is purely for the device management out-of-band traffic (getting updates, manage the device etc). To have an S2S VPN you still have to configure policy ( Palo is a zone-based firewall where Cisco ASA is an interface based). Since you cannot add your MGMT interface to the policy think it is not possible in your scenario. However, you still can manage firewall using any other interface with MGMT profiles applied allowing (HTTPS or/ and SSH).
Thx,
Myky
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 02:28 PM
If Mgmt interface is only control plane traffic how we can use Palo Alto FW deployed in AWS cloud with single public IP for S-S ipsec VPN tunnel .
I have checked this thread and used Elastic Public to asssociate with eth1 but still not working and is getting stuck in Maintaence mode .
Will really appreciate if someone can tell me if S-S IPsec vpn possible for PaloALto deployed in AWS with Single IP or not .
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2017 11:03 AM
You are going to have to set an unstrust interface to be public facing and terminate the IPsec tunnel there, and then apply a management profile to it. Using the only public IP for your management interface will not work for setting up a tunnel.
ACE 7.0, PCNSE7
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2017 10:12 AM
Hello,
Azure announced last month support for multiple public IPs per instance: https://azure.microsoft.com/en-us/updates/ga-multiple-ips-per-nic/
You can now assign a public IP to the VM-Series management interface and a separate public IP address to the dataplane and use that second IP to build your IPsec tunnel.
- 10205 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- PA 445 setup in Next-Generation Firewall Discussions
- NAT Policy Zone Selection for DNAT (and DNAT+SNAT) — Is My Understanding Correct? in Next-Generation Firewall Discussions
- How does the Azure Virtual Network discovers that there is Palo Alto Gateway Interface in VM-Series in the Public Cloud
- HA GlobalProtect firewalls in Azure in VM-Series in the Public Cloud




