- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Is there a possibility to create an IOC list to employ it in a query?
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Re: Is there a possibility to create an IOC list to employ it in a query?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2023 09:44 AM
Hello Everyone,
I'm new to Cortex XDR and looking to enhance our IOC hunting process. I want to run a scan with IOCs from our subscribed external threat feed.
I have uploaded multiple IOCs to XDR via add IOC option but only able to run the query for each at a time, is there any way to scan multiple IOC at same time, because we get the feed on daily basis and there will be more than 20-30 mixed type IOCs per feed.
Any feature to upload those IOCs in list or dataset, to employ it in a query to scan?
Your insights and guidance would be greatly appreciated.
Thanks in advance!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2023 11:18 AM
Hi @AvinashAddala ,
Greetings! Thank you for writing to live community!
When you upload IOCs to the list, the Cortex XDR scans for the last 10000 events ingested into Cortex XDR to match the value of IOC rules added to XDR instance and trigger alerts. However, if you have the list of IOCs by types listed, you can use XQL query for the same by looking into network connections for IP address, and process activity event type for processes and SHA256 and file type events for file types.
For eg.
dataset = xdr_data
| filter dns_query_name in ("goplayz.com")
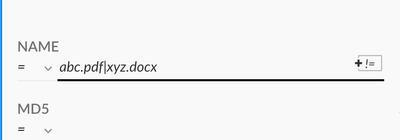
Also, when using native query builder you can add "|" as a symbol between the two indicators to combine them.
Eg screenshot below:
Hope this helps. Please mark this response as "Accept as Solution" if it answers your query.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2023 11:18 AM
Hi @AvinashAddala ,
Greetings! Thank you for writing to live community!
When you upload IOCs to the list, the Cortex XDR scans for the last 10000 events ingested into Cortex XDR to match the value of IOC rules added to XDR instance and trigger alerts. However, if you have the list of IOCs by types listed, you can use XQL query for the same by looking into network connections for IP address, and process activity event type for processes and SHA256 and file type events for file types.
For eg.
dataset = xdr_data
| filter dns_query_name in ("goplayz.com")
Also, when using native query builder you can add "|" as a symbol between the two indicators to combine them.
Eg screenshot below:
Hope this helps. Please mark this response as "Accept as Solution" if it answers your query.
- 1 accepted solution
- 2228 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!