- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Splunk Add-on XSOAR Mapping
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XSOAR Discussions
- Re: Splunk Add-on XSOAR Mapping
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Splunk Add-on XSOAR Mapping
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2024 03:04 AM
We fetch incident with Splunk Add-on. What should I do to enrich and map it? How can I run the mapper here? or do I need to proceed with setincident commands?
#SplunkAddon
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2024 08:46 AM
Hello!
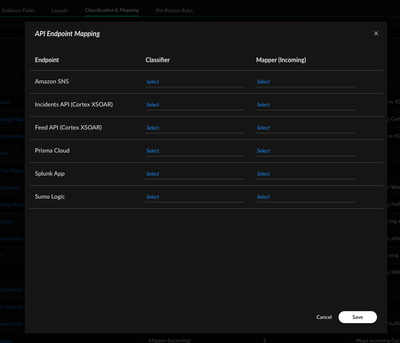
For 6.X versions, You can map these alerts by going to object Setup->Incidents and clicking on three dots on the top right and selecting API endpoint mapping and then selecting the splunk addon option there.
If you are on the newer versions, the same option is found on the classifiction and mapping page.
- 1290 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Splunk Search Result Issue in Cortex XSOAR Discussions
- Splunk integration - Mirroring not working in Cortex XSOAR Discussions
- Do we have XQL query builder feature in XSOAR in Cortex XSOAR Discussions
- How to Handle High-Volume Email Events in XSOAR Without Overloading the System in Cortex XSOAR Discussions
- How do I send an alert to XSOAR? in Cortex XSOAR Discussions