- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
2X of PA820 Active/ Passive Design question
- LIVEcommunity
- Discussions
- General Topics
- Re: 2X of PA820 Active/ Passive Design question
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
2X of PA820 Active/ Passive Design question
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 05:39 AM
Hi All
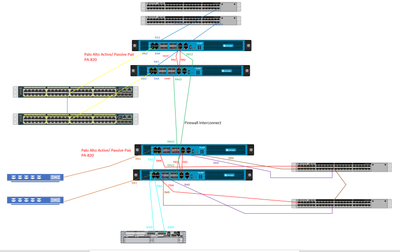
After some advice, planning to have 2 X PA820 pairs of Active/ Passives, Inner and outer firewalls protecting some internal networks.
See the diagram, Does the HA2 link pass data plane traffic at all? Or can it?
There could be a scenario that one set of FW's can failover and the primary unit of one trying to speak to the standby unit of the other.
Or is the only solution to put a switch in between the green cables FW Connect to stop this issue?
Thanks All
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 07:37 AM
1. Just curious why you are using the old school Firewall sandwich design?
2. HA2 passes sync traffic for the HA Pair.
3. Why would you put a switch between the two? Wouldn't you want a router? Otherwise everything in the middle of the sandwich would need multiple gateways/routes (Yuck, I've seen this).
4. Am I assuming too much based on your limited information?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 08:14 AM
Everything @jeremy.larsen mentioned is correct. If you have the interfaces for it and you don't want to utilize a switch/router between the networks, you would need to cable up both units to both units. So both sets of firewalls need a route to both firewalls. Every "Inner" firewall will need a link to both of your "outer" firewalls. That way if you have a failover you actually have a route for it to get there.
A lot of times people will put something like a switch or router between the two just to save on interfaces, especially on the smaller units like the 820 where interface count is minimal.
Also I'm really going to echo what @jeremy.larsen already brought up, but is something I would really be asking if someone came to me with this design, why are you still using this model? Do you actually need an "Inner" and "Outer" firewall or could you condense these into a larger HA pair.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 08:43 AM
Thanks for the replies
Ideally yes I would of used a single ha pair of 820s instead of a back to back pair. But our customer has already purchased them and have asked us to design them basically 😞
So the plan was to use a /30 between both Firewalls, since the Palo altos share the same IP address on the interfaces when in active passive mode.
The idea of putting a switch in the middle would be so the firewalls don't send packets to the passive Firewall as it will drop traffic.
So I would take both FW interconnect ports from both pairs (4 ports in total) and patch them into a new L2 vlan, then when the Firewalls arps for the address that's in the routing table it will respond with the correct active address instead of the possibly one of the active nodes paseses traffic to a passive node and will be dropped.
Does that make sense?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 09:36 AM
I'm just trying to help here. That doesn't make any sense at all unless you were running these Active/Active. But then that's another discussion. Traffic will never go to the passive firewall (it's passive after all) and the VIPs will all be on the Active firewall (ARP baby). I guess I don't really see what you are trying to accomplish here. A /30 between them doesn't give you any address space in the DMZ/Middle of the Sandwich if you are going "Old School" like this. Perhaps we are missing some piece of the design here?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 10:04 AM
Heres a better diagram of the full solution......so this is for an OT environment so sensitive networks.
So there are networks behind the Inner Palo Alto pair.....they will be accessed by the Cisco LAN behind the Outer Pair of Palo Altos
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 10:19 AM
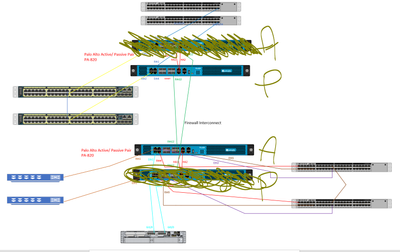
Heres another of the situation I want to aviod;
if the active FW in the bottom pair wants to send traffic north, it will send via the passive not - which will fail
And if HA2 doesnt send the traffic to the active pair....then still the traffic is dropped
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 10:33 AM
if the active FW in the bottom pair wants to send traffic north, it will send via the passive not - which will fail
And if HA2 doesnt send the traffic to the active pair....then still the traffic is dropped
Why do you thing this will ever be sent via the passive node? The passive node does not accept or forward any traffic, nothing is "alive" so to speak outside of your management interface. It has absolutely no way to send/receive traffic.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 10:39 AM
Because the active node in the latest diagram I sent only has a link to the passive node, if that was in active mode it would be fine and would pass traffic.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 10:44 AM
That would be a design flaw then. As I stated previously if you aren't going to use some sort of switch/router in the middle and directly connect these two clusters you would need to have each individual node to have it's own link to both the opposite firewalls. If that isn't done you don't have a route to the active unit and this breaks your entire design.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 10:56 AM
Yeah, thanks for clarifying.
I propose to use a switch to connect the fw interconnects together.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 12:14 PM - edited 04-08-2020 12:16 PM
If this were me (and it's not), I would STRONGLY suggest that your customer reconsider this design proposal. This looks like it could turn into a real nightmare to manage with a ton of traffic being unnecessarily processed twice by the same firewall engine. The only scenario I would even consider this in, is one where each pair is managed by a different team without overlap. Even this, would have to be a forced security requirement on me. My two cents. Good luck to you.
PS - Even better, I would talk to Palo about trading in those 4 firewalls for 2x of a more powerful model.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 01:35 PM
I may see if thats possible...but I doubt it.
very little traffic traverses the firewalls pairs.....syslog, snmp, icmp thats it basically.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 02:02 PM
Another quick question sorry...
In PA Active/ Passive - they share the same interface IP's (except the management ports)
In a Cisco ASA world, if I wanted to logon to the Passive member, I could do by using the Standby address of the firewall. But in Palo Alto world that's not possible as interfaces don't have standby address.
I'm assuming the only way I can achieve the above is by using the management ports on each of the firewalls, then I can logon to the Passive node via the management IP.
We are going to be using Panorama too
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2020 02:18 PM
I've run into this a lot. The first thing I tell people recovering from ASA... is take everything you know about firewalls and perform a memory dump. ASA is a slowly dying dinosaur that has somehow survived on the Cisco name alone. PAN operates completely different and the sooner you accept this, the sooner you will be happy, successful and never look back. Management ports on the PAN run on the Control Plane and can be thought of as running on an independent OS with it's own routing table, ACL, etc. If you have any familiarity with Juniper, it's almost the same. To answer your question, Passive Nodes are available using the Management port completely independent of the Active Firewall. If you plan on using Panorama, don't set up your firewalls and then port to Panorama later. You will regret it. Step one of my Panorama deployments is to completely wipe the config on the Firewalls. All configs/settings/updates/etc are then wholly managed and pushed from Panorama. It is a top tier product and makes life full of awesome. It really sounds to me like you guys need some PAN training. I can't recommend this enough and you should talk to your PAN Rep ASAP.
- 13482 Views
- 21 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Beginner Question Best Way to Structure Policy Design in Palo Alto Firewalls in General Topics
- Palo Alto FW manage by SCM - problem with HA in Strata Cloud Manager
- IPSEC VPN for the FW MGMT in Next-Generation Firewall Discussions
- Question about Wildfire signature updates in Palo Alto Active-Passive mode. in Next-Generation Firewall Discussions
- Unable to establish tunnel during Service Connection configuration (Details Added with Screenshot) in Prisma Access Discussions