- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Allowing ms-update on app-default, File blocking PE and therefore no windows updates
- LIVEcommunity
- Discussions
- General Topics
- Allowing ms-update on app-default, File blocking PE and therefore no windows updates
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2017 12:05 PM - edited 08-23-2017 12:07 PM
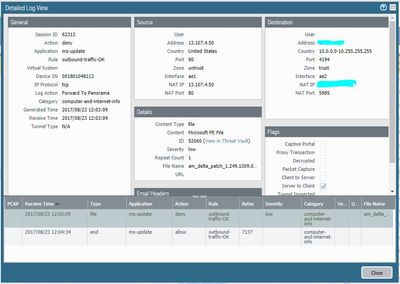
Me again and file blocking per PA best practice (PE, multi-level, etc..) and allowing ms-update on application default. However the WSUS server is not able to download any updates and its classifying a PE file as a threat. The file in question is am_delta_patch_1.249.1313.0_52b04aae0eb450654fc89884b43d10b7ed5 and threat-id is 52060 but nothing matches in the Threat Vault.
Do I need a specific rule allowing windows updates that specifically allows PE files?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 10:21 AM
- Create a custom url category with the following entries: *.update.microsoft.com, *.windowsupdates.microsoft.com, *.windowsupdate.com, windowsupdates.microsoft.com
- Create a new security policy rule and attach the custom url category from step 1 directly to this policy in the url category column
- Attach the security profiles you want to this rule but other than your normal internet access rule, allow pe files here
- (If you decrypt tls traffic) create decryption exclusion rule where you use the same custom url category from step 1
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2017 12:56 PM - edited 08-23-2017 12:57 PM
On the WSUS server you'll need to allow PE downloads, Once you have a policy allowing the WSUS server to actually download the PE files you should be good to go.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2017 01:05 PM - edited 08-23-2017 01:38 PM
What the easiest way to do that for all users, ms websites and whatever relevant file types? I read an old article about PA and MS-updates but I don't want to block web browsing.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 07:24 AM
Is your WSUS server in the same zone as your clients?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 07:47 AM
You really shouldn't have to worry about it then as the traffic wouldn't pass through your firewall so your File-Blocking profiles wouldn't effect anything. Allowing the WSUS server to go out and grab the updates should be the only step you need to take at that point.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 08:48 AM - edited 08-24-2017 09:14 AM
@BPry wrote:You really shouldn't have to worry about it then as the traffic wouldn't pass through your firewall so your File-Blocking profiles wouldn't effect anything. Allowing the WSUS server to go out and grab the updates should be the only step you need to take at that point.
It would if the machines weren't part of the domain (we have both domain and non-domain windows) and thus not getting updates from WSUS. Therefore I need to make sure its allowed through. To get it working until I (or PA support) can figure it out I just allowed PE files but that brings me to my next point which would fix this issue anyways. Albeit not in any way shape or form that I would prefer it to be done.
Another issue today with downloading large files from the internet and having any profile applied to the matching policy causes them to slow to a crawl or stop completely. The only way I can make it so the files complete is by having 0 profiles applied to the rule. PA don't know why its doing it and don't know when they can get a resolution to me because they are 'busy with other cases.' Still haven't heard back from imaps case which I opened on 8/21 (status says researching) although you guys helped me fix that one.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 10:21 AM
- Create a custom url category with the following entries: *.update.microsoft.com, *.windowsupdates.microsoft.com, *.windowsupdate.com, windowsupdates.microsoft.com
- Create a new security policy rule and attach the custom url category from step 1 directly to this policy in the url category column
- Attach the security profiles you want to this rule but other than your normal internet access rule, allow pe files here
- (If you decrypt tls traffic) create decryption exclusion rule where you use the same custom url category from step 1
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 10:28 AM
Out of curiosity what PAN-OS version are you running? 8.0.4?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 11:55 AM
In my rule I use web-browsing, ssl and ms-update. What exatly do you mean with "block everything else"?
If you added the custom category into the security policy as described, traffic will only match that rule for these URL's and nothing else.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 01:12 PM - edited 08-24-2017 01:25 PM
I was confusing URL filter with URL category. Do you do any file blocking with this specific rule?
Will give it a try.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2017 03:37 PM
No, in this case I have set the fileblocking to log all
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-25-2017 07:42 AM
Not relevant in this topic, but if you ONLY want to allow windows updates and deny everything else towards the internet, you have to add crl.microsoft.com and www.microsoft.com as microsoft hosts two CRLs there.
--> do not add *.microsoft.com to your custom url category as this will also allow the "customer experience" microsoft analysis service/spyware to send out data...
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-17-2023 07:58 AM
I have a specific rule for the wsus server to only connect to Microsoft for Windows updates (Just like the one recommend here). The issue I have encounter so far is that it only downloads the definitions but won't download the actual update when I approve the KB. Is there a specific URL where it downloads the update. I added all the URLs Microsoft recommends to the allowlist.
- 1 accepted solution
- 54495 Views
- 14 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- EDL Performance and Refresh Handling in Panorama in Next-Generation Firewall Discussions
- Cannot add BIOC rule to restriction profiles in Cortex XDR Discussions
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- Issue with IOC not blocking MyPDFSwitch executable in Cortex XDR Discussions
- E token Cortex XDR blocking in Cortex XDR Discussions