- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Can the PAN device block HTTP Dos Attacks?
- LIVEcommunity
- Discussions
- General Topics
- Can the PAN device block HTTP Dos Attacks?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2013 10:36 PM
Hello Guys,
I'm going to do some service availability test in the near future. We can't get any information of the attack pattern. The only information we know is that the tester will conduct these attack.
- HTTP CC(cache-control) attack
- Slowloris attack
- Http post attack
- Http Hash dos attack
I'm afraid that those attack patterns seem to be normal for the PAN device (It's like brute force attack, working base on the threshold value)
I've heard that the best way to block these kinds of attacks is the setting server's timeout value or threshold value.
But I have to find out some way to do this job with PAN.
Can we block those attack with IPS Dos Signature or Custom Signature? If we can, does anyone know how set-up to the custom signature for those attacks?
Regards,
- Labels:
-
Content-ID
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-26-2013 07:28 PM
Hi hjlee.
You can make a custom signature easily using as below info
But It's not important thing in real world because 7.7 DDOS attack of Korea was not related certainly above and HTTP Get flooding and UDP flooding that made it.
Thanks.
Regards,
Roh
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2013 11:02 PM
Hi
you can found explanation for DOS protection by paloalto with this doc https://live.paloaltonetworks.com/docs/DOC-5078
but there is no information in this doc about HTTP DDOS.
I'm interresting in hhtp ddos too
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2013 11:05 PM
http ddos could be limited by rate limiting
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2013 11:59 PM
I think these attacks can exhaust server resource with normal Http transaction, and before the the server reaches its max concurrent connection limits, its resource worn out ..
And PA's Dos Protection uses Layer 3~4 information, those attacks are based on Layer 7 information (Http get, post value etc...). In my opinion I should be able to set up Http get method threshold.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-19-2013 12:34 AM
I've found one IPS signatures which can block HTTP Slowloris attack.. :smileygrin:
| Attack Name | HTTP: Apache Denial Of Service Attempt |
| Description | This event indicates that someone want to exhaust the apache resources, as described by slowloris. |
| Threat ID | 40018 |
| References | https://threatvault.paloaltonetworks.com/Home/ThreatDetail/40018 |
| Severity | high |
| Category | brute-force |
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-20-2013 10:44 PM
I think it's not exact for your case. HTTP: Apache DOS signature that triggered only 40 times in 60 second and only Apache related case. In my case I created a Custom Signature for HTTP post, CC that blocked in security rule while having BMT.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-21-2013 12:07 AM
Dear My Lovely Roh..
Can you send me the custom signature information that you used for the BMT? :smileygrin:
Thanks ahead..
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-26-2013 07:28 PM
Hi hjlee.
You can make a custom signature easily using as below info
But It's not important thing in real world because 7.7 DDOS attack of Korea was not related certainly above and HTTP Get flooding and UDP flooding that made it.
Thanks.
Regards,
Roh
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-27-2013 05:21 PM
Thanks Roh,
I love You. :smileygrin:
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-28-2013 07:07 AM
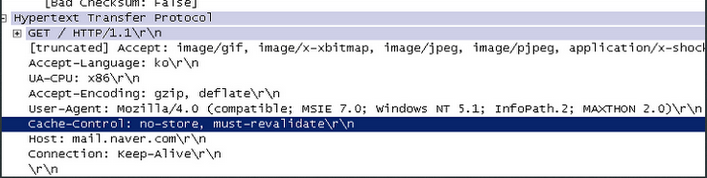
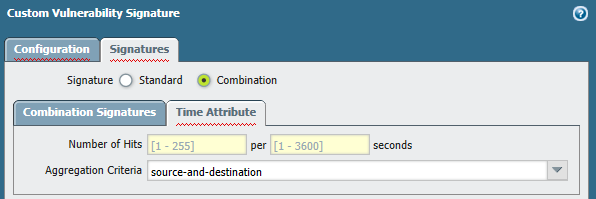
FYI, if you want the threat signature to trigger by a threshold value (i.e 30 hits in 10 sec), you can use the signature type=combination and define its time attribute. Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-03-2013 07:52 PM
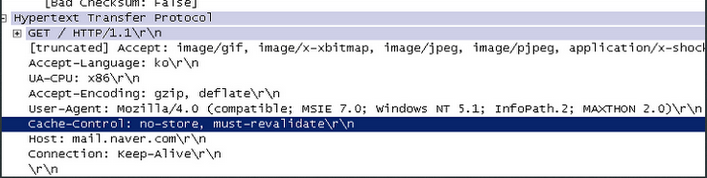
CC Attack means Challenge Collapsar Response attack. In south Korea we call this 'Cache-control attack' .
To make combination signature we need basic signature.
This is my custom signature 41023 which block cache control message based on threshold value.
So far I couldn't find any signature for Challenge Collapsar.
So I made custom signature for this attack.
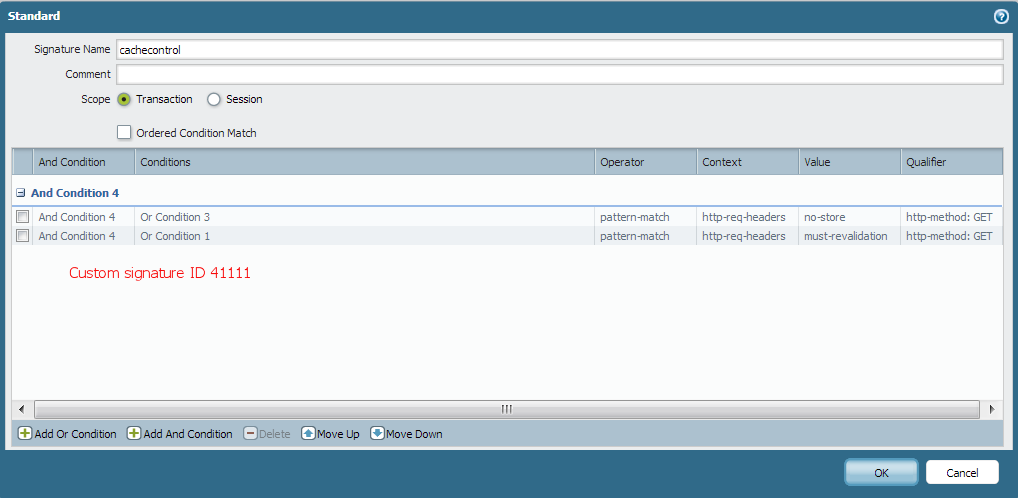
I used my custom signature 41111 to make custom signature 41023 (combination signature working on threshold value).
As you might know, the problem is signature 41111 work before 41023..
you guys have any solutions??
Regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-29-2016 09:26 AM
This is an old issue but we still don't have signature for CC right now. Actually you shoud set the action of 41111 to allow, then 41023 can be triggered when threshold been reached.
- 1 accepted solution
- 17730 Views
- 14 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Custom BIOC Rule won't apply to Prevention Profile in Cortex XDR Discussions
- Cortex XDR Device Control Violation Alerts in Cortex XDR Discussions
- GRPC status UNAVAILABLE in intelligent offload in VM-Series in the Private Cloud
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions
- Can Cortex XDR fully substitute for Microsoft Defender Attack Surface Reduction (ASR) rules? in Cortex XDR Discussions




