- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Global Protect not working with RADIUS NPS and LDAP on the same server.
- LIVEcommunity
- Discussions
- General Topics
- Global Protect not working with RADIUS NPS and LDAP on the same server.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2021 09:59 AM
Hello everyone,
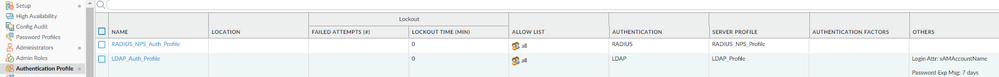
We have a Firewall configured for Authentication for LDAP and RADIUS NPS.
Both works fine when I force the authentication profile using CLI:
test authentication authentication-profile LDAP username user password
test authentication authentication-profile RADIUS username user password
However, when using Global Protect with an Authentication Sequence, I see the RADIUS Auth Denied in the Event Viewer in Windows and the connection fails in the client, so it doesn't go to the next Authentication Profile.
I also wanted to use Groups. I have 2 in Active Directory (RADIUS_Users and LDAP_Users) but I can only use Group Mapping for the LDAP, so RADIUS has no option to match a specific group. Any workaround for this?
Thanks.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2021 04:16 PM
Hi @JorgeOrtega ,
That is correct. The firewall uses LDAP for group mapping. That is the only (and correct) selection. You do not need to specify the group under the server profile. As long as you can modify the allow list in the authentication profile, it will work as desired.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2021 11:29 AM
Hi @JorgeOrtega ,
The authentication sequence should check both authentication profiles regardless of the AAA response -> https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PMdXCAW. (The link on the bottom of that link provides more details.) I would double check that the user is not failing via LDAP also.
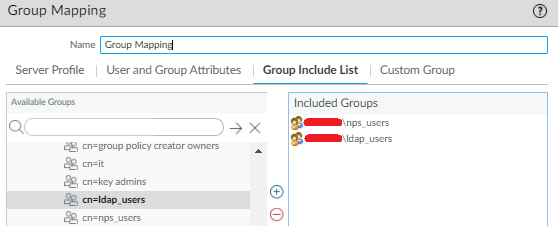
With regard to groups, you can configure groups in the authentication profile under Advanced. The groups configured under Device > User Identification > Group Mapping Settings > [edit group] > Group Include List will show in the authentication profile. The firewall does an LDAP query for the group and gets the users. If the login username matches, then the profile is used.
With regard to NPS, the Event Log > Security should tell you why it is failing.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2021 12:01 PM
Hi Tom,
Thanks for the detailed response. I have two groups and I want the RADIUS Authentication Profile to use the RADIUS_NPS group in Active Directory. I also want the LDAP Authentication Profile to use the LDAP group in Active Directory.
The Authentication sequence is using RADIUS first and LDAP second and the idea is a user that belongs to the RADIUS group in AD should hit this Authentication Profile first and users that belongs to the LDAP group in AD should bypass the RADIUS and goes to the LDAP instead. Will this work?
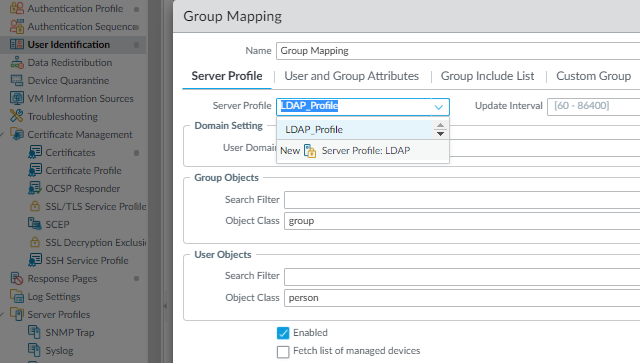
When following that link for the group mapping, I can only create one group for LDAP as this is the only Authentication Profile I can select. Now if I do this I can then select it in the Allow List under the Advanced authentication profile under Advanced tab as you mentioned, however when I do the same for the RADIUS authentication profile it only shows the LDAP group. Should I type the name of the group manually? For example: CN=RADIUS_Users,CN=Users,DC=mydomain,DC=com ?
Thanks for the guidance on this matter.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2021 12:10 PM
Hi @JorgeOrtega ,
Yes, that will worked based upon the allow list. No, you shouldn't have to type it in manually as long as you can see it under Device > User Identification > Group Mapping Settings > [edit group] > Group Include List.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2021 01:58 PM
I just checked that the only way that I can add groups to the Allow List below is by creating the Group Mapping. (right now both are using All):
However still wondering why you select the RADIUS-NPS group shown below along with the LDAP one...
When I only see the option for LDAP under the Server Profile for the same Group Mapping rule?
I have no option to do Group Mapping of my RADIUS_NPS group to be under the NPS Server Profile only under the LDAP Server Profile.
Is this correct?
Regards,
Jorge.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2021 04:16 PM
Hi @JorgeOrtega ,
That is correct. The firewall uses LDAP for group mapping. That is the only (and correct) selection. You do not need to specify the group under the server profile. As long as you can modify the allow list in the authentication profile, it will work as desired.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2021 04:38 PM
Tom, I want to thank you for your valuable help. This worked like a charm. I had some issues in my setup that I discovered while I was creating the group mapping. I could also understand how these groups works. I created an RADIUS group and left All for the LDAP, so only a specific group that belongs to this group will have 2FA. Thanks again and have a great evening.
Jorge.
- 1 accepted solution
- 8569 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- resolve hostname in logs now working in panorama in Panorama Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- return traffic being dropped, not being sent through the vpn tunnel in General Topics
- XDR Endpoint with Containers in Cortex XDR Discussions