- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How do you Commit the configuration of a Panorama to an existing HA Pair of 5060s?
- LIVEcommunity
- Discussions
- General Topics
- How do you Commit the configuration of a Panorama to an existing HA Pair of 5060s?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How do you Commit the configuration of a Panorama to an existing HA Pair of 5060s?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-05-2014 08:32 AM
I followed the instructions from “Panorama-Device-Migration-Tech_Note-revB.pdf” using the CLI method to capture the configuration of an HA Pair of 5060 running PAN OS 5.0.11 and paste it to the Panorama running PAN OS 6.0. The Migration Checklist states during the cutover process to cutover 1 firewall first. The document states after deleting the Rules, objects etc. on the FW, when committing the configuration to the HA pair, follow the documented HA procedure to minimize network impact. What are they referring to when they say “follow the documented HA procedure? I cannot find anything referencing what they mean. I figure I should leave the passive FW alone and do the Active one first because when doing a commit on the Active FW it usually pushes the configuration to the Passive FW.
But, What impact does the Device Group have when you set the FWs up as an HA pair in the Device Group? Also, when deleting the items from the Active FW, should I also delete them from the Passive FW?
Another approach that I have read is to rename the objects, policies etc. on the Panorama then commit it to the FWs. What does that do to the existing configuration on the FW? Is there now a duplicate configuration with a different set of names? Or does it overwrite the existing configuration?
Lots of questions and scenarios that I cannot find answers to anywhere.
- Labels:
-
Configuration
-
Panorama
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-05-2014 12:29 PM
Hello Nonno1,
Point-1: We will add devices into Panorama based on their Serial number, and it does not matter from Panorama point of view, whether the devices are standalone or in HA. The panorama will always treat as an individual device. Please follow the mentioned KB article to understand information synchronized in HA pair Information Synchronized in an HA Pair
NOTE: If you use untrust interface of the device as service route, the configuration will be pushed only to active device (assuming policies are configured correctly) because only 1 IP is active at a time for active/passive, even though you have the same IP on both devices. Suggested configuration would be to use management interface itself. Since the management IP address is unique for both devices, you will not have any issues and will prevent extra bandwidth consumption on untrust interface.
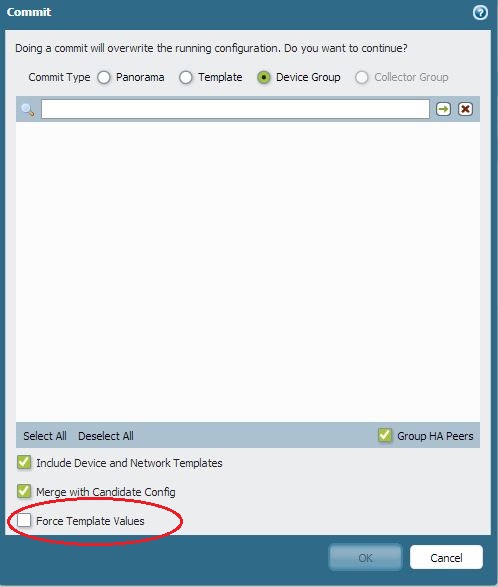
Point-2: If you want to merge the panorama pushed config with your PAN FW local config, you should use the option "merge with candidate config". But if you want to override your FW config with Panorama pushed config, then you have to check the option "Force template values".
Hope this helps.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-06-2014 05:33 AM
I will give this a try.
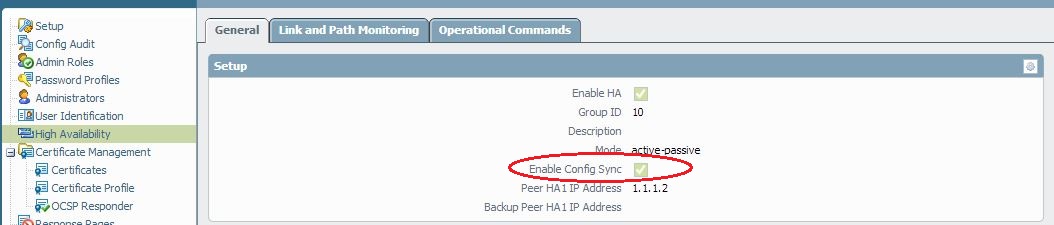
Our SE answered my question this morning also. The only addition he made was to Disable Config Sync in the FWs before pushing configuration from Panorama.
Thank You
- 2942 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Regarding existing logs when adding an extended disk to a VMFW using AWS. in VM-Series in the Private Cloud
- Rename security zones on panorama and push it to the firewalls in Panorama Discussions
- Onboard production firewall to STRATA CLOUD MANAGER in Strata Cloud Manager
- Request for SD-WAN Deployment Documentation in Azure in Advanced SD-WAN for NGFW Discussions
- createNewIndicator - IP is not an existing indicator type in Cortex XDR in Cortex XDR Discussions




