- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to limit concurrent GlobalProtect connections per user
- LIVEcommunity
- Discussions
- General Topics
- Re: How to limit concurrent GlobalProtect connections per user
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How to limit concurrent GlobalProtect connections per user
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-24-2018 03:06 AM - edited 05-17-2021 02:13 PM
Hi communit
So far it isn't possible to limit the concurrent GlobalProtect connections per user directly in PAN-OS. There is a feature request #4603 for which you can vote and wait/hope that this will be implemented.
If you need a solution (workaround) right now, once more the PAN-OS API is your friend. Because we (like probably some or a lot og admins here) had the problem, that we had users, specially from external suppliers, who shared their accounts and so they logged in multiple times. So I wrote this little powershell script. The script needs to be configured as scheduled task to run every minute for example. Every time the script runs it checks the connected Global Protect users and then kicks out users that are logged in multiple times. If you want, you can also specify the number of allowed concurrent logins per user with the variable $maxlogins. This way you're able to kick out users that are logged in more than 3 times for example.
[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12;
$apikey = "INSERT_API_KEY_HERE"
$firewall = "FIREWALL_HOSTNAME_OR_IP"
$gpgateway = "GLOBAL_PROTECT_GATEWAY_NAME"
$maxlogins = 1
Function callApiOp ($firewall, $param) {
$request = New-Object System.Net.WebClient
$apiurl = "https://" + $firewall + "/api/?key=" + $apikey + "&type=op&cmd=" + $param
return [xml]$request.DownloadString($apiurl)
}
$param = "<show><global-protect-gateway><current-user><gateway>" + $gpgateway + "</gateway></current-user></global-protect-gateway></show>"
$logins = callApiOp $firewall $param
$logins = $logins.response.result.entry | sort 'login-time-utc'
$loginevents = @{}
foreach ($event in $logins) {
$username = $event.username
if ($loginevents.ContainsKey($username)) {
$loginevents.($username) = $loginevents.($username) + 1
}
else {
$loginevents.Add($username,1)
}
}
foreach ($user in $loginevents.GetEnumerator()) {
$forcelogout = $logins | Where-Object {$_.username -eq $user.key}
$userstologout = $user.Value - $maxlogins
for ($i=0;$i -lt $userstologout; $i++) {
if ($forcelogout.count -eq $null) {
$domain = $forcelogout.domain
$computer = $forcelogout.computer
$username = $forcelogout.username
}
else {
$domain = $forcelogout[$i].domain
$computer = $forcelogout[$i].computer
$username = $forcelogout[$i].username
}
$logoutparam = "<request><global-protect-gateway><client-logout><gateway>" + $gpgateway + "-N</gateway><reason>force-logout</reason><user>" + $username + "</user><computer>" + $computer + "</computer>"
if ($domain -ne "") {
$logoutparam += "<domain>" + $domain + "</domain>"
}
$logoutparam += "</client-logout></global-protect-gateway></request>"
$status = callApiOp $firewall $logoutparam
if ($status.response.result.response.status -eq "success") {
write-host "Logged out user $username from computer $computer"
}
else {
$msg = "Could not logout " + $username + " from computer " + $computer + " because of the following error: " + $status.response.result.response.error
Write-Host $msg
}
}
}
Maybe this helps at least some of you, or at least gives another idea for the almost countless use cases of the PAN-OS API.
Feedback is appreciated 😉
Regards,
Remo
- Labels:
-
GlobalProtect-COVID19
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-29-2020 07:53 AM
This script is awesome, thank you for such a contribution. Let me ask you something, it is possible the script disconnect the second connection not the first one? I was making some test and it disconnects the first connection and the company requirement is the second one.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-13-2021 01:24 PM
Hi everyone
Until now there is not a way to limit user with the NFGW.
We are trying to use this script, but we cannot logout the users.
the script runs and also display the users that are logout, but we made some test and the users are still conected. Could you help us with this? We try with On demand configuration and User-Logon on the APP of Global Protect but nothing happens.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2021 10:15 AM
Whith PAN-OS version are you using? I created the script already quite a while ago, so it might be possible that the logout API call is no slightly different and because of that the logout does not work. Maybe tomorrow I can do some short tests with PAN-OS 9.1.8 and if required I can update the script.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-17-2021 02:40 PM
Hi all
I updated the script slightly with some more lines and a hopefully helpful output in case of errors. I tested the script on a firewall running PAN-OS 9.1.9 with a global protect deployment that has SAML as authentication configured. With another check regarding other authentication methods where the domain attribute may be is there it should still work in such deployments. So if anyone is going to use the script, feel free to get back to me in case of problems or other feedback.
(I updated the script in the first post of this topic)
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-19-2021 07:45 AM
hello,
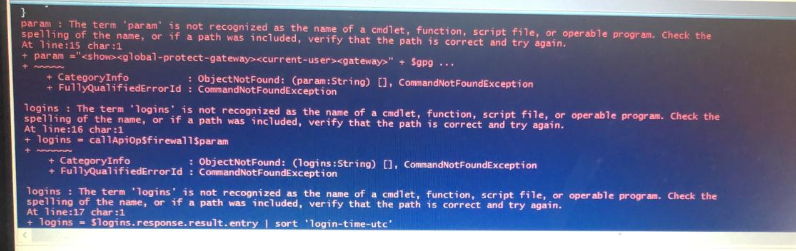
I am running the script the same as the one you posted but I have some errors.
that script still works with version 9 of palo alto and from a powershell 2016
hola,
yo estoy ejecutando el script igual al que publicaste pero tengo algunos errores.
ese script aun te funciona con la version 9 de palo alto y desde un powershell 2016
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-07-2023 11:48 AM
An alternative python based solution to the same problem is here:
https://live.paloaltonetworks.com/t5/api-articles/limit-maximum-globalprotect-vpn-sessions/ta-p/3328...
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-29-2024 12:14 PM - edited 08-29-2024 12:21 PM
Yet another easy-to-deploy, dependency/installation free, cross-platform and open-sourced go based modern solution available here:
https://live.paloaltonetworks.com/t5/general-topics/pan-gplimiter-limit-concurrent-globalprotect-ses...
The project can be directly reachable here as well: https://github.com/enginy88/PAN-GPLimiter
BTW Thank you @Remo for the inspiration!
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-03-2024 07:47 PM
@Remo I adhere to the colleague's comment, the script is great. But it would be very useful for me if I disconnected the second user who logs in and not the one who was previously logged in
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-11-2024 04:29 AM
Hi @R.Girard888323 !
If you would use either one of two more advanced solution, it can be parametrically defined which one should be kicked: oldest or newest sessions. Please check the last 2 post above your comment.
In @fyousuf 's implementation, "remove_new_sessions" config parameter controls that behavior. In my implementation "PANGPLIMITER_KICK_OLDEST" config parameter controls that behavior.
Hope it helps!
- 53782 Views
- 39 replies
- 16 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GP with saml authentication always redirects to idp in General Topics
- Global Protect Internal Detection in GlobalProtect Discussions
- GlobalProtect 6.1.11-175 Connection Issues in GlobalProtect Discussions
- Stealth Rule Question in Next-Generation Firewall Discussions
- GlobalProtect Always-On (6.3.3-c711) – Users Stuck in “Connecting” State but Still Have Internet Access in General Topics