- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to set up two HA (active / passive mode) firewalls to be managed by panorama
- LIVEcommunity
- Discussions
- General Topics
- Re: How to set up two HA (active / passive mode) firewalls to be managed by panorama
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How to set up two HA (active / passive mode) firewalls to be managed by panorama
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2020 01:01 AM
Hi All,
I already have two firewalls to set HA and use Active / Passive mode.
But when I put both devices into the same Device Groups and Templates and push the configuration file to both devices, the HA settings of the second device will be overwritten by the HA settings of the first device.
I saw this "Migrate a Firewall HA Pair to Panorama Management"
It mentioned that it seems to set variables
Please help me.
Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2020 06:31 AM
Hi @HankHsieh
I would configure the HA config locally on the devices and not in the template on panorama. This way you will have a lot less troubles. Some of the HA config you can configure in panorama with different device specific templates so that both devices have different configurations, but at least the HA IP addresses you must configure locally on the device (https://docs.paloaltonetworks.com/panorama/9-0/panorama-admin/manage-firewalls/manage-templates-and-...) so I recommend to simply configure HA completely local.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2020 01:26 AM
Hello
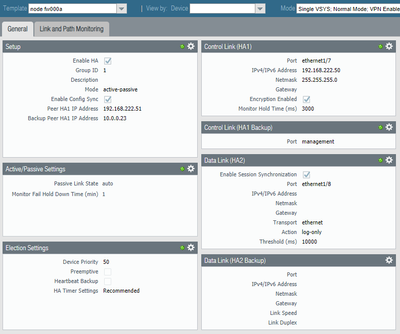
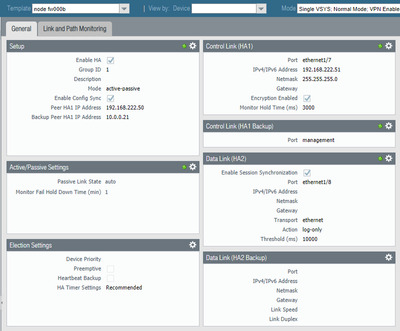
We are creating template stacks, one dedicated stack per node
1) node specific template
2) system specific template
3) general template
In the node specific themplate the HA settings are set. Everything else is configured in the system specific template. This ensures that no config (except mgn interface related one) needs to be done on the firewall nodes, everything is managed by panorama.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2020 12:08 PM
@JoergSchuetter how did you manage to configure the HA IP adresses in a template on panorama? I would also prefer to use the template for everything but because of the HA IP addresses there was such a mess that I simply changed to configure everything HA related locally.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2020 05:29 PM
After I managed the device from panorama,
I used the same template and device group for both HA devices, and set all HA configs of this template to variables, and manually set the HA settings locally on the passive device, which works normally!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-22-2020 08:50 AM
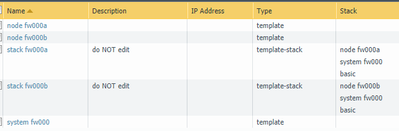
The setup looks like this:
Besides this, there is only a config for the management interface certificate in the node template.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-22-2020 10:13 AM - edited 01-22-2020 11:41 AM
Thanks for sharing. In this case I will give it another try.
The question now is why does paloalto write in the adminguide that IP addresses of HA firewalls can only be configured locally ... @kiwi do you may have the answer?
Edit: @JoergSchuetter what PAN-OS version do you use? When I configure the HA IPs in panorama template stack, they are not applied to the firewall. All the HA config works, but when I check locally on the firewall the IPs aren't from the template...
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-23-2020 08:48 AM
@Remo : We are using this template stack since version 8.0 (works well with 8.1 and 9.0).
One initial step is to clean up the local stored config:
delete rulebase
delete zone trust
delete zone untrust
delete network virtual-wire default-vwire
delete network interface
delete network tunnel
delete network ike
delete network virtual-router default
delete deviceconfig system update-schedule
delete deviceconfig high-availability
delete deviceconfig system timezone
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-23-2020 01:18 PM
Did exactly that (besides the HA config I have nothing locally), but there is no value for HA IP address locally on the firewall ...
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2020 12:10 PM
What do you mean with "no value for HA IP address locally"?
It will not be listed on the CLI using "show ..."
Does it show up in the GUI of the firewall?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2020 01:10 PM
It really means there is no value locally, so does not show up in the GUI of the firewall - actually as described in the panorama template limitations.
- 12728 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- How to push Bulk IOC list in file format to panorama firewall? in Panorama Discussions
- IoT Devices in Panorama in Panorama Discussions
- Onboard production firewall to STRATA CLOUD MANAGER in Strata Cloud Manager
- EDL Capacity Reached but Lists Show Empty / Default Entry (0.0.0.0/32) – Panorama Multi-VSYS Setup Post: in General Topics
- SCM Device Restart Incidents — False Positive Notification in Strata Cloud Manager