- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Implementation of PA-500
- LIVEcommunity
- Discussions
- General Topics
- Implementation of PA-500
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Implementation of PA-500
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-12-2014 04:43 AM
Hi All,
Please I need your help to prepare a design document for the implementation of a PA-500 for one of our client, following is the existing architecture of the client site:
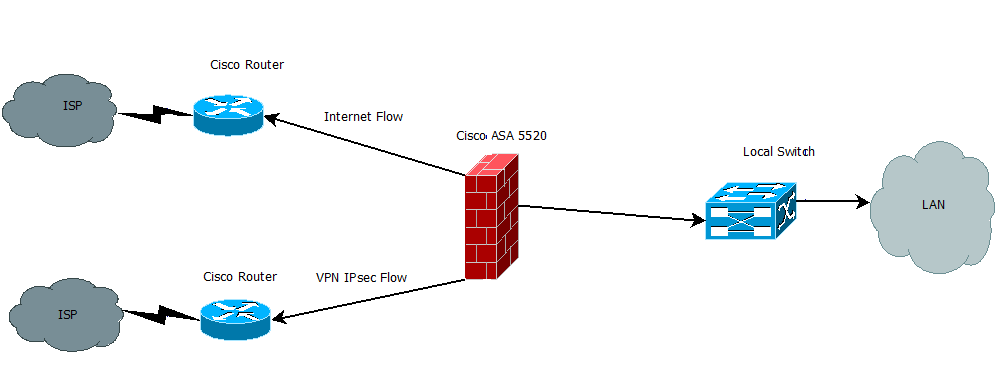
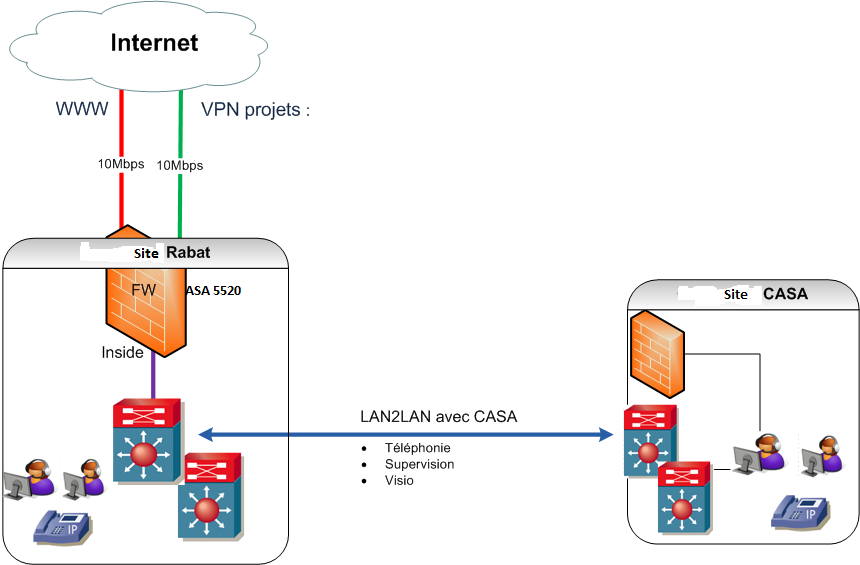
The customer need is to control the Internet flow so they can do the URL filtering and traffic shippement and also to have visibility into the nature of to flow to internet (youtube, facebook ...) and to control users and have statisctics of their connexions. for the other connexion of 10Mbps used for VPN flow with their client they need just to have visibility into it they don't have to control it so we proposed to them to implement PA-500 in virtualwire for the internet flow and in TAp mode for the other liaison of VPN flow since in my inderstinding they don't need any layer 3 features seeing that the VPN is already established at the level of the ASA Firewall ( please correct me if I am wrong), for the moment our customer is asking about the advantage and disadvantage of the following scenario and a test procedure to mesure the impact of put in the paloalto firewall in place:
Scenario 1: put the PA-500 before the ASA 5520 ( between ASA5520 and the LAN switch) so they can control both links with internet, since both internet links are linked to ASA and it's for ASA to destinguish between trafic to go to internet and the trafic that goes into VPN basing on the source and destination address. I think in these case we will put the PA-500 in the virtual mode and we can control both trafics but in my understinding we will not be able to distinguish between the two flows.
Scenario 2: putting the PA-500 after the ASA 5520 ( between ASA5520 and the ISP routers). so we put PA-500 in a combination of Vw mode and Tap Mode.
Please let me know wish of those scenarios is better and what will be the impact on service during the implementation of each scenario and the impact on the system performance after putting in place the firewall. also i need to have an idea about the latence, and the delay that will be caused in both scenarios and all the possible other KPIs that can help us evaluate the two different scenarios.
Also note that we will need to connect the PA-500 with the Active directory of the customer so we can get informations using LDAP about users in order to control their trafic. and for the VPN liaison is there any method to see the amount of throughtput that every VPN tunnel is consuming knowing that every tunnel is defined with an IP address source and destination and if it's possible in wish scenario can we perform it.
Thank you in advance.
Best Regards,
- Labels:
-
Configuration
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-12-2014 07:14 AM
Why in the world wouldn't you just replace the ASA with the PA-500? That's the most elegant, simple solution. The PA-500 is capable of IPSec tunneling.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-12-2014 07:21 AM
Hi Eric,
it's the client recommendation they won't change the ASA so we need to comply with their needs, they want for the first steep to test paloalto firewalls if they are satisfied with them then after they could think to change the ASA but for the moment they want to keep ASA and add the PA-500.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-12-2014 07:25 AM
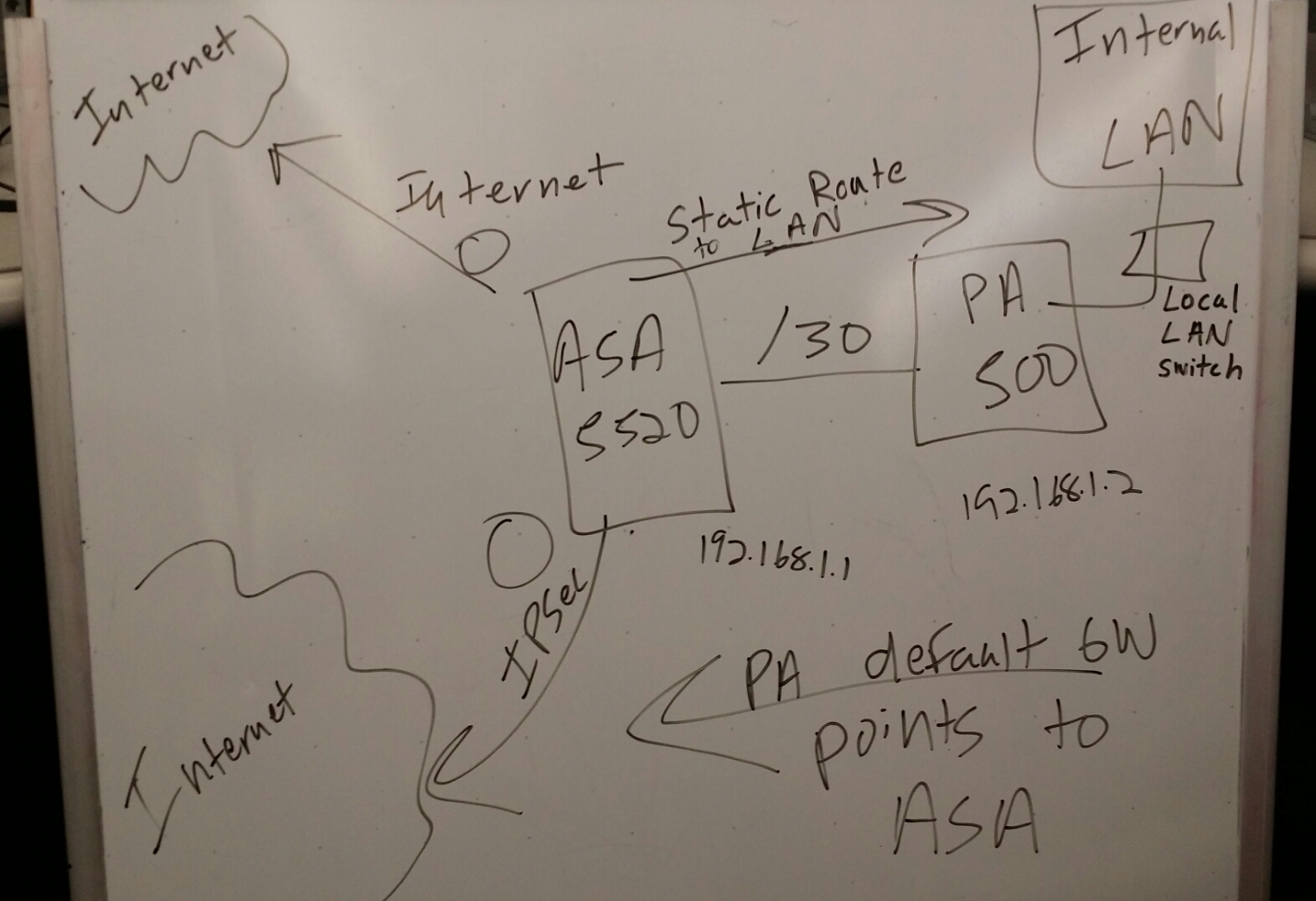
In that case, I would leave the ASA on the edge, let the IPSec tunnel continue to land on it, and make the PA-500's default gateway the ASA. That way the ASA is still the "edge firewall," and the IPSec tunnel lands on it just fine. Create a /30 link between the PA and the ASA, and have a static route on the ASA that points to the internal LAN that sits behind the PA.
If you want me to draw that out just ask, might be easier to see if I draw it out.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-12-2014 07:37 AM
Please can you send me the draw I would be grateful, other thing why should I create a link between the ASA and the PA-500 since I can have an idea about the users trafic and perform trafic control and URL filtering in the virtualwire mode in this case we will not have to do any change in the client architecture (Or it's necessary to deploy the PA-500 in layer 3 Mode in order to do control and URL filtering?).
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-12-2014 08:20 AM
Due to some licensing thing going on at work, they took Visio from us. So please bear with me ![]()
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-12-2014 08:22 AM
I would say you avoid Vwire mode, because if you ever want to do DHCP from your PA-500, you can't do it with Vwire. It just feels more "clean" to me to have an actual layer 3 routed interface on your PA-500. Let your PA-500 take over as the internal LAN default gateway, and have a /30 as the interconnect to the ASA.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-12-2014 08:36 AM
Thanks Eric and sorry if i keep asking but personnaly since it's my first installation I prefer to go for the Virtualwire so in case I faced some troubels it will be easy to roll back and retry after troubleshooting. I hope you are understinding my worries. please note that i will need to connect with the LDAP server to retrieve users informations so Can I do it in the Vwire mode?
other thing the customer is asking to know the difference and benefits of each of the possible scenarios so they can decide whether to put it before or after the ASA.
Thanks,
- 5078 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA-445 VERSION 11.2.7-h8 in General Topics
- Palo Alto for email security in Next-Generation Firewall Discussions
- Identifying Source IP Addresses for Routing Palo Alto Firewall Logs to an Azure Collector via IPSec Tunnel in General Topics
- Proper User-ID Configuration in General Topics
- Failed logins from 127.0.0.1 in VM-Series in the Public Cloud




