- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
internal routing being blocked
- LIVEcommunity
- Discussions
- General Topics
- internal routing being blocked
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 10:10 AM
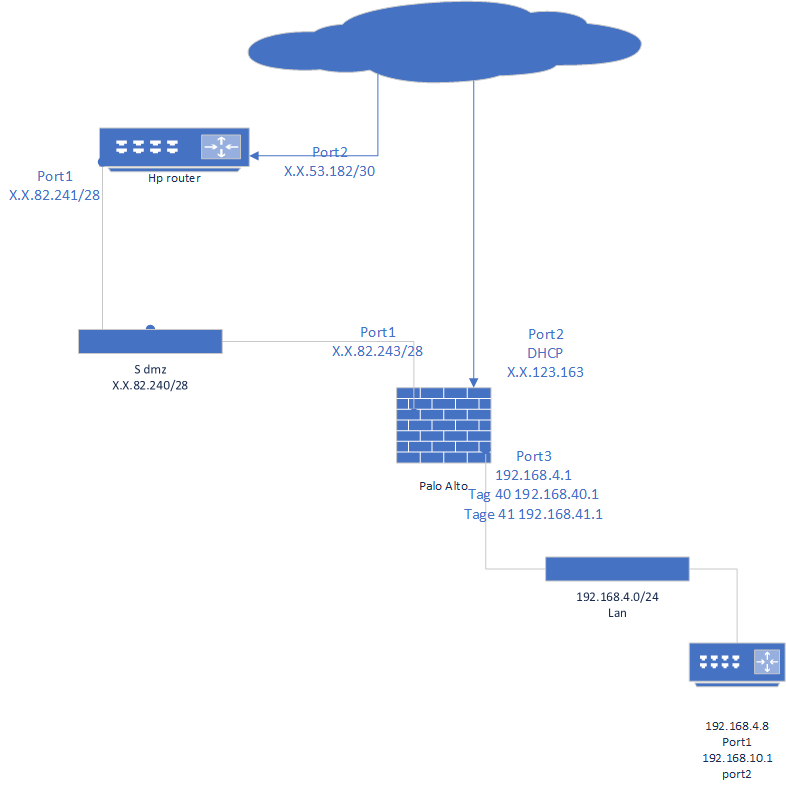
I'm having an issues with some internal routing I have two virtual router that have statics routes for an internal phone network on a different router in my trusted zone I can ping from computers in my lan but when i try and access any websites or management tools it doesn't work if I add a persistent route on the desktops it start to work but when i remove it it goes back to acting strange
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 04:20 PM
I would advise against disabling this behavior.
There are only a few choices with what you can do.
- Put static routes on every machine on 192.168.4.0
- Make 192.168.4.8 the default gateway for that network, making sure that router has a default route to .1
- Move 192.168.10.0 to a spot where traffic has to cross the firewall to reach it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 02:39 PM
It's sounds like asymetric routing but I'll need some clarification on things. ICMP will work asymmetric but traffic needing a three-way handshake won't. The firewall needs to see the entire flow or it will drop traffic.
Can you reference the drawing you included to explain what does and doesn't work? I can't tell what's trying to access what.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 02:42 PM
I'm trying to get clients from the 192.168.4.x network to access clients in the 192.168.10.x network but it only work when i add persistent routes to the client in the 192.168.4.x network
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 02:48 PM
So when you add the static route on the clients, you point 192.168.10.0 to 192.168.4.8?
Does the Palo Alto have a route for 192.168.10.0 that points to 192.168.4.8?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 02:51 PM
yes my virtual router has a static route of 192.168.10.0/24 to 192.168.4.8
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 03:02 PM
Then the problem is asymmetry.
Here's an example of traffic flow without the static route on a client:
192.168.4.100 sends a syn to 192.168.10.100. This goes to the PA, which then sends it to the router at 192.168.4.8
192.168.10.100 sends a syn-ack to 192.168.4.100. This goes to the router at 192.168.10.1, which then sends this directly to the client without passing through the PA.
192.168.4.100 sends an ack to 192.168.10.100, which then goes to the PA. The PA did not see the syn-ack so it drops the traffic.
When ICMP works but tcp traffic fails, it's generally asymmetric routing.
By adding the static route, all traffic bypasses the PA so it will work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 03:10 PM
now how would i go about fixing that generally its better to add routes the the default gateways if i'm not mistaken correct? I looked up asymetric routing and it seems that disabling the protection on the firewall is generally not recommended
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2018 04:20 PM
I would advise against disabling this behavior.
There are only a few choices with what you can do.
- Put static routes on every machine on 192.168.4.0
- Make 192.168.4.8 the default gateway for that network, making sure that router has a default route to .1
- Move 192.168.10.0 to a spot where traffic has to cross the firewall to reach it.
- 1 accepted solution
- 5710 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Enforce GlobalProtect Access Based on Microsoft Intune Compliance Status in GlobalProtect Discussions
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- traffic disruption on routing change in Next-Generation Firewall Discussions
- How to make Router BGP ping into IP inside Palo Alto in Next-Generation Firewall Discussions
- Is DoS Protection Detection Possible in TAP Mode? in General Topics