- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
mail/dns/www/ftp server in DMZ - need advice
- LIVEcommunity
- Discussions
- General Topics
- Re: mail/dns/www/ftp server in DMZ - need advice
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
mail/dns/www/ftp server in DMZ - need advice
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-04-2013 08:49 AM
Hello
I'm preparing to move my server that is mail/dns/www into DMZ zone. I did some tests and it seems to be working - but as good as I can test...
Do I should use application (dns,smtp,pop3,imap,ftp,web-browsing) or use a services on ports 53,25,110,21,80,465,993,995)?
What are you using and why?
My NAT rule:

My security policy:
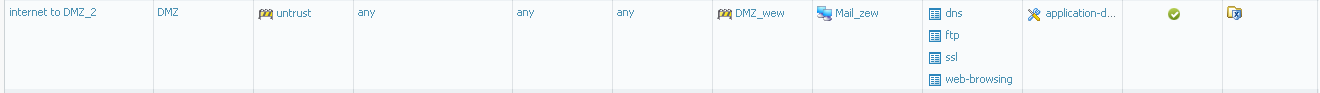
I have of course U-turn policy to allow acces to this server from my local zones.
What about profiles?
I did one group for servers:
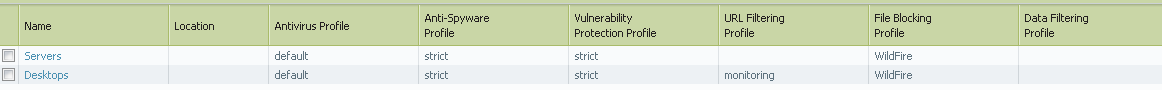
Is it make sens to scan trafficwith this all profiles?
Could someone share their policies - please?
I didn't see such topic in this forum and it could be very useful for every new PA user.
With regards
SLawek
- Labels:
-
Configuration
-
Networking
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-04-2013 09:00 AM
Hello Slv,
I would like to answer to the question about using apps or services. The advantages of using Apps is that the PAN would inspect the traffic at application layer and allows only those ports required by that application. ( We should select the service as "App-default" to allow only those ports what the app needs ). I see your security policy with apps and app default and that is the right way.
In regards to the group of profiles, that is used when there is a need to have same set of profiles for multiple security rules making configuration simpler and is completely fine. Rather than individually selecting the profiles for each security rule we can use a group. If needed to customize profiles then we can use profiles selectively.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2013 11:00 AM
Thats good that my polices are OK. But I scared that I missed some aplication ...
ie - I moved www server to DMZ few days ago, and I see that I have to add also new appliocations: rss, web-crawler. Until now I think that it should be in web-browing, but after I checked few times traffic logs for denied applications I realized that I'm wrong.
I agree with you about group of profiles. But is is correct to scan traffic using antivirus/anti-spyware/volnerability/data filtering? or maybe one of them is enought? every profile is taking some resources of PAN, and I'd like to use only that are nessasary.
p.s. - sorry for my bad english
Regards
SLawek
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2013 03:02 PM
Hi SLV,
Since you're dealing with new policy, you might want to have a "lose deny" rule below the new one, that way you can verify that the traffic you want is matching and you can tune the deny rule as you see how it's going. So if you are certain you do not what to host FTP or SSH, add those to the deny rule, watch the monitor and add additional service to the allow or deny rule as needed. Once you think you have a stable policy, make the deny a 'deny all' rule and that should do it.
Mike
- 3316 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- XSIAM - Data Patterns in General Topics
- PAN-308564 Known Issue in Advanced SD-WAN for NGFW Discussions
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- XQL - Hostfirewall events in Cortex XDR Discussions




