- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
OpenSSL Heartbleed bug: CVE-2014-0160
- LIVEcommunity
- Discussions
- General Topics
- OpenSSL Heartbleed bug: CVE-2014-0160
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
OpenSSL Heartbleed bug: CVE-2014-0160
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2014 10:35 PM
Hi,
Just wondering if any Palo Alto versions are affected by this bug in OpenSSL?
Regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 06:14 AM
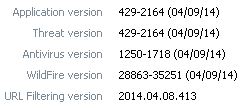
Application and Threat Content Release Notes
Version 429
Notes: A critical vulnerability in OpenSSL (CVE-2014-0160: OpenSSL Private Key Disclosure Vulnerability) was recently disclosed, affecting servers running OpenSSL 1.0.1 through 1.0.1f. This vulnerability allows arbitrary memory readout, which effectively exposes primary key material and compromises the integrity of the secure channel.
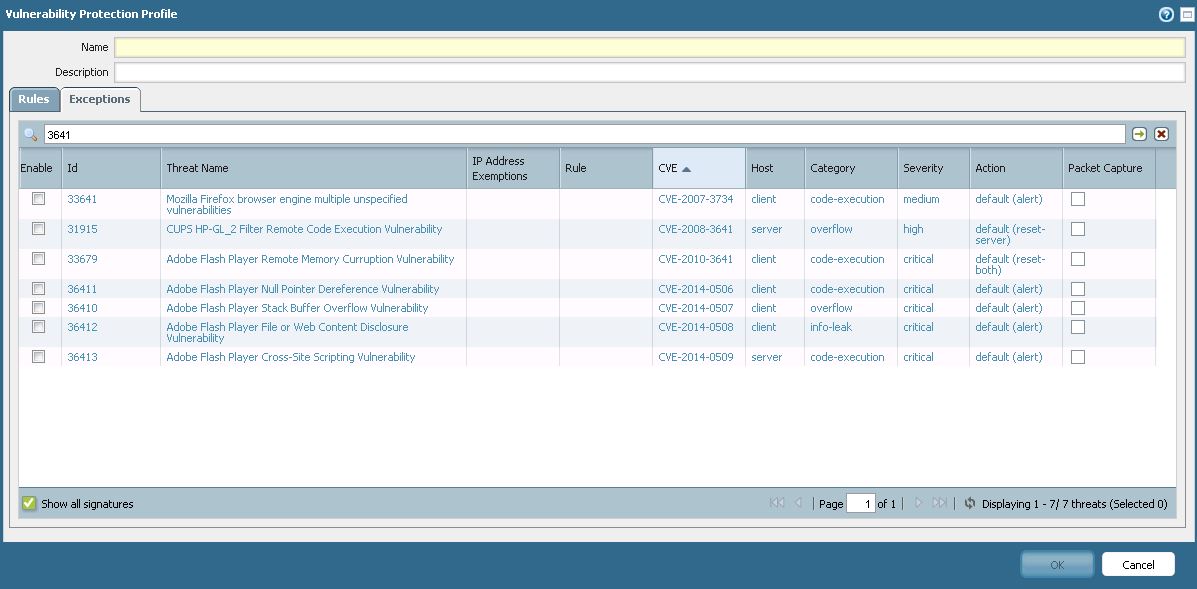
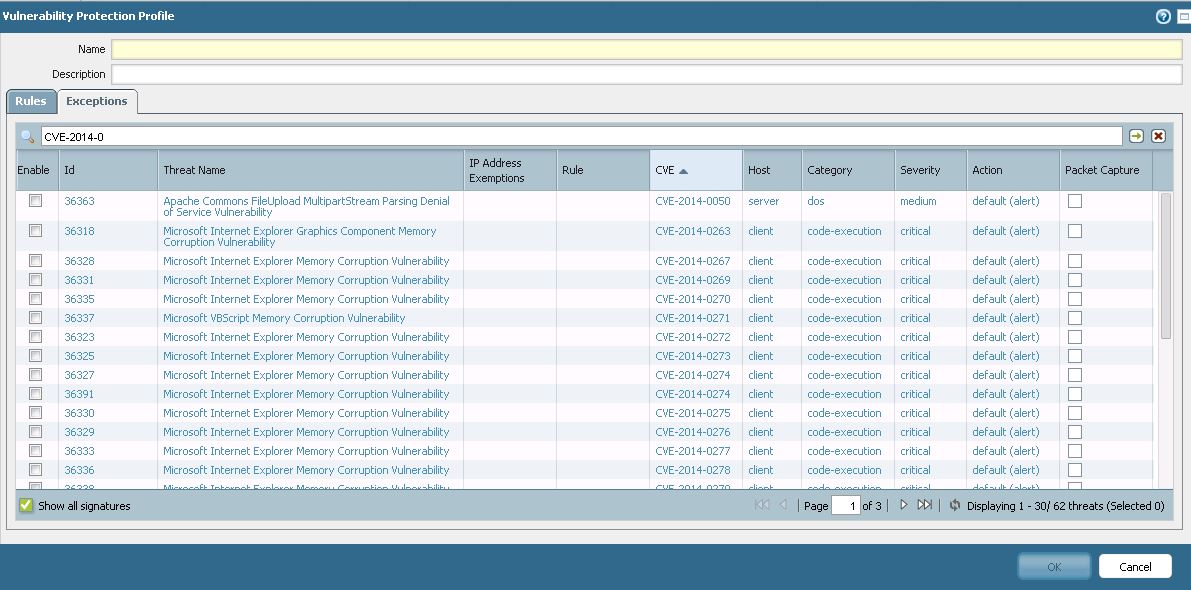
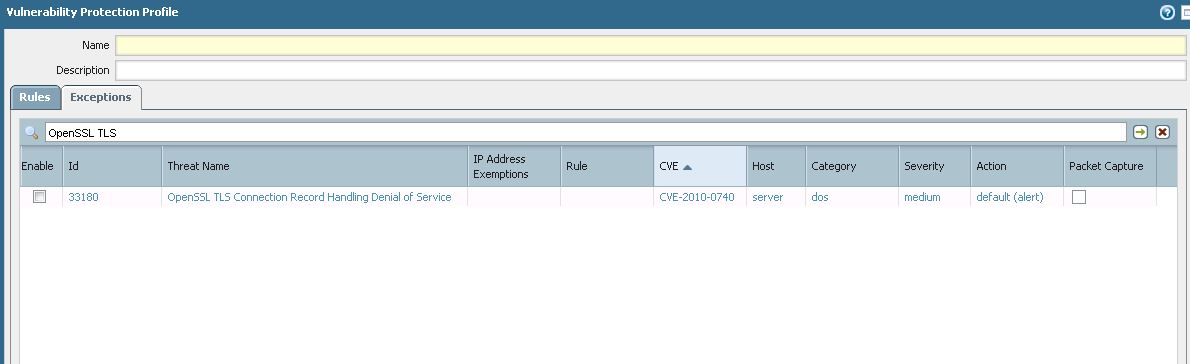
To address this vulnerability, Palo Alto Networks has released an emergency content update that provides detection of attempted exploitation of CVE-2014-0160 with IPS vulnerability signature ID 36416 ("OpenSSL TLS Heartbeat Information Disclosure Vulnerability") with critical severity and a default action of block. Palo Alto Networks customers with a Threat Prevention subscription are advised to verify that they are running the latest content version on their devices. If you have any questions about coverage for this advisory, please contact Support.
Modified Decoders (1)
Name |
ssl |
New Vulnerability Signatures (1)
Severity | ID | Attack Name | CVE ID | Vendor ID | Default Action | Minimum PAN-OS Version |
critical | 36416 | OpenSSL TLS Heartbeat Information Disclosure Vulnerability | CVE-2014-0160 | reset-server |
|
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:24 AM
Anyone else not able to get this update to show up in dynamic updates? Or am I missing something?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:26 AM
I have installed Application and Threat Content Release 429 but I cannot find the Signature....?
Anyone else ?
I just checked on the Dynamic Updates Website on Support, it's not there.... Withdrawal ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:34 AM
Version 429 isn't showing up for me either.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:43 AM
Ok I have deleted the Content Image 429 on the Firewall and hit the Check now button again, not coming down the line anymore ...
Something screwed up 429 ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:46 AM
Hello gafrol,
If you have an issue with 429 not being able to see the new tid, can you log out of the device then log back in again and see if you see it.
Regards,
Jahnavi.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:46 AM
Did not help either. For some reason 429 is not available for download anymore.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:47 AM
I just was told that they revoked the 429 update... New release time is unknown
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:55 AM
openssl version does not work on my windows server
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 07:57 AM
Windows has its own implementation of SSL they are not using openssl. To check openssl version simply enter "openssl version" on the cmd line.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 08:00 AM
Hello gafrol,
Contents 429 has been pulled, it is not available for download anymore.
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 08:01 AM
Content 429 has been pulled and PAN engineering team is working on it. We will keep you updated on this.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 08:03 AM
yes I tried that command and it did not work on my windows servers
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2014 08:04 AM
Looks like it's available again...just a minute ago.
- 40326 Views
- 64 replies
- 5 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- XDRC Connection Error in Cortex XSIAM Discussions
- Renew Palo Alto Global Protect Certificate issued by Public CA in General Topics
- VPN Gateway fails to authenticate clients with new certificate uploaded in General Topics
- error when try to install cortex on redhat 10 in Cortex XDR Discussions
- NGFW Global Protect 6.2.7 Global Counters Negotiation Error TLS 1.3 MAC-OS in GlobalProtect Discussions




