- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Precedence of Routing\NAT\Policy
- LIVEcommunity
- Discussions
- General Topics
- Re: Precedence of Routing\NAT\Policy
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-02-2023 05:26 PM
Dear All,
Dear All,
I want to know what is correct precedence among Routing\NAT\Security Policy
So If a packet hits on the outside zone of the Firewall then whether below process is correct?
1. Whether FW has route for the destination\5.5.5.5 ( If YES)
2. Whether there is any NAT policy (If YES) ( Assume -> After NAT, 5.5.5.5 translated to 6.6.6.6)
3. Then security policy should allow original destination IP(5.5.5.5) or Translated destination IP (6.6.6.6)
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-02-2023 05:43 PM
Hi @ManinderNegi ,
Great question! A good general rule is "Pre-NAT IP, post-NAT everything else." For example, in this document -> https://docs.paloaltonetworks.com/pan-os/10-1/pan-os-networking-admin/nat/nat-configuration-examples... the IP in the security policy is pre-NAT, while the destination zone is post-NAT. Scroll down to the bottom to see the NAT and security policy rules.
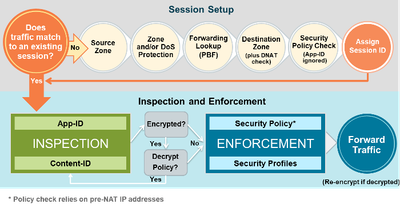
With regard to precedence, a good diagram is this one taken from the PCNSE study guide on Beacon.
Of the order you mentioned, the route lookup is done 1st (Forwarding Lookup). Then the NAT policy lookup is 2nd (DNAT check). However, NAT is not applied to the packets until the egress interface (Forward Traffic). The forwarding/NAT lookup is necessary to determine the destination zone. Then the security policy is checked last. That is why the IP address in the security policy is pre-NAT.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-02-2023 05:43 PM
Hi @ManinderNegi ,
Great question! A good general rule is "Pre-NAT IP, post-NAT everything else." For example, in this document -> https://docs.paloaltonetworks.com/pan-os/10-1/pan-os-networking-admin/nat/nat-configuration-examples... the IP in the security policy is pre-NAT, while the destination zone is post-NAT. Scroll down to the bottom to see the NAT and security policy rules.
With regard to precedence, a good diagram is this one taken from the PCNSE study guide on Beacon.
Of the order you mentioned, the route lookup is done 1st (Forwarding Lookup). Then the NAT policy lookup is 2nd (DNAT check). However, NAT is not applied to the packets until the egress interface (Forward Traffic). The forwarding/NAT lookup is necessary to determine the destination zone. Then the security policy is checked last. That is why the IP address in the security policy is pre-NAT.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-09-2023 10:54 PM
Hi Tom
Thanks for your explanation. I like to ask if the same applies for inbound traffic from Internet, e.g. DNAT 5.5.5.5 to 172.16.1.5. If the public IP subnet (e.g., 5.5.5.0/29) is not configured as an interface on the firewall, based on the flow with route lookup done first, the traffic should drop since the firewall would not have the public IP subnet in its routing table. Am I interpreting it correctly?
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2023 05:56 AM
Hi @SimonLim ,
That is correct. Please refer to this article for the fix. https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClGZCA0
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2023 06:24 PM - edited 08-10-2023 07:22 PM
Hi Tom
Thanks for the KB link. I was testing out this scenario for a customer who had experience Internet outage when an interface where their public ip subnet was a sub-interface failed. This matches perfectly with the KB and my understanding. However, in my setup, I was unable to replicate the customer's problem AND the result was opposite of the KB and the precedence as explained. It messed with my head.
I have attached my setup and the results in here. I setup my lab to simulate customer's network when the interface (with the public ip subnet as sub-interface) was down, i.e. public ip subnet is not in the firewall's routing table (not even connected). SNAT and DNAT was working fine. SNAT for all outbound Internet was translated to 200.1.1.6 and DNAT for Inbound Internet to a server was translated from 200.1.1.2 to 172.22.22.22. I have only a static route on the router (ISP) referencing 200.1.1.0/29 with the firewall's external interface IP (110.99.99.1) as the next hop gateway. There is only default route from the firewall to the router (as shown). Besides the NAT rules, there are no traces of 200.1.1.x in other configurations. My PA is a 225 running 10.2.4.
Appreciate if you can review and see where I may have done wrong to have the opposite result.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-11-2023 06:25 AM
Hi @SimonLim ,
I don't see anything that you are doing wrong. I may be missing something.
Here are a couple of docs that don't mention routes needed for source NAT pools that do not overlap with the outside interface.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClhwCAC
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClOLCA0
I wonder if your source NAT somehow allows the traffic not to be dropped?
Very interesting. Thanks!
Tom
- 1 accepted solution
- 24489 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PAC Retention and URL Category Priority Behavior in Prisma Access in Strata Cloud Manager
- URL games allowed through while blocked in Next-Generation Firewall Discussions
- Weak Path Affinity in Prisma SD-WAN Discussions
- How to trigger a "Response page" on Palo Alto NGFWs using URL filtering & Decryption in Next-Generation Firewall Discussions
- GlobalProtect not allowing internet access when Parallels or Docker are running in General Topics