- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Remove Domain Name from LDAP user mapping IMPOSIBLE =(
- LIVEcommunity
- Discussions
- General Topics
- Re: Remove Domain Name from LDAP user mapping IMPOSIBLE =(
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Remove Domain Name from LDAP user mapping IMPOSIBLE =(
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-14-2022 10:24 AM
Hi
Someone know if there is a way to remove the domain name from the group mapping
The reason why is because i get from external source on palo alto the user id test1 or "test2" or "test3"
Goal is create a policy rule base on the source user that is being part of a domain group
In my case LDAP group mapping get this information:
show user group name emea.com\test
short name: emea.com\test
source type: ldap
source: test
[1 ] emea.com\test1
[2 ] emea.com\test2
[3 ] emea.com\test3
This is good but only need from the group mapping the name
"test1" or "test2" or "test3"
and not
emea.com\test1
emea.com\test2
emea.com\test3
i expend hours and there is no way to understand or found the reason why palo alto get from ldap group mapping "domain name + name"
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-15-2022 03:16 AM
Hi @alvaroarcaz ,
If I am not wrong, group mapping will always add domain, because it needs to cover cases where you have multiple domains or even domain forest.
So in my humble opinion you should try to append the domain to the user-ip-mapping so it can match the group mapping.
Can you share bit more information how you receive user-ip-mapping? How it is configured currently?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2022 03:11 AM
I receive the user logs from the Pulse Secure VPN appliance to the USER ID
agent located on windows server
With the regex i was able to just get the user id from the user connected.
My surprise was that I was not unable to map the user id with the domain
group on security policy, this is really a bad situation for us.
Is it possible to just avoid the domain name on the palo alto when trying
to search on ldap group?
I can not understand why yes or yes paloalto build this:
>From LDAP group PaloAlto get:
domainname\userid
With the UserID agent after the regex i get a mapping with IP+userid, and
on the firewall logs i can see this way:
source ip: ip from user
source user: userid
The security policy will never match!! as there is a difference between
domainname\userid => LDAP PaloAlto
userid => Information from my agent
Hours and hours spent here and no answer anywhere im totally frustrated ...
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-08-2022 03:27 AM
Hi @alvaroarcaz ,
I know there is a way to override the domain for Group Mapping, but not sure if there is a way to remove it completely.
As I mentioned for me it sound reasonable to have it as you may work in multi domain environment.
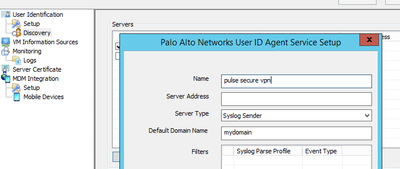
The solution for you to add the desired domain to the user-ip-mapping from the User-ID agent that is processing the Pulse Secure logs. In User-ID agent settings that is parsing the Pulse Secure syslog messages go to User Identification -> Discovery -> Servers -> Edit you Pulse Secure entry and add the domain the same way as you see it the group mapping
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-09-2022 03:46 AM
Thanks for the answer. This worked as expected for Windows users but
problems came for MAC users or Iphone Users.
In my company the IOS devices are not part of the active directory domain
and for instance there is no way where a USERID agent can find domain
events on the active directory.
For me the solution came to avoid this domain mapping on firewall level, i
have had a case with the vendor for more than a month and am still waiting
to find the way....
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2023 08:01 AM
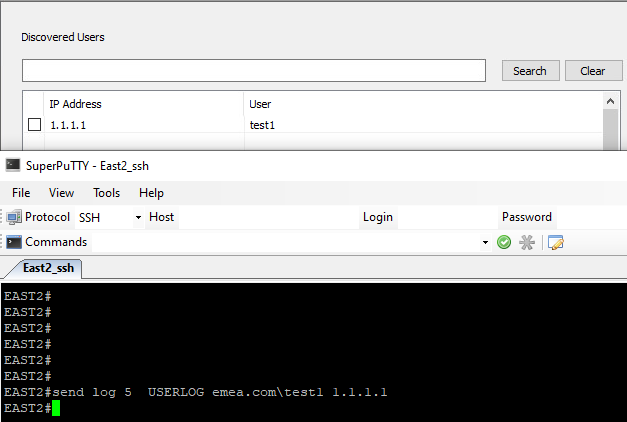
As @A_Astardzhiev stated above, you can add in whatever domain you want. Below, I'm using a syslog filter to capture the username via syslog, no domain added.
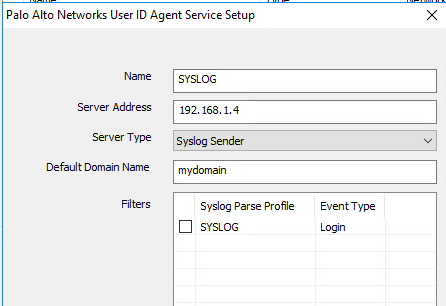
I update the syslog sender config to include a domain (mydomain).
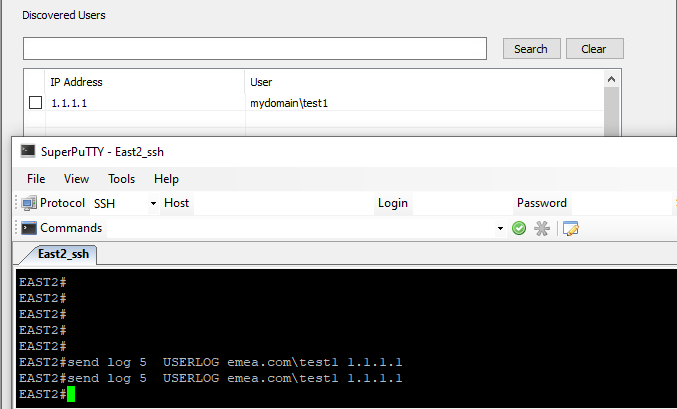
I trigger another syslog message, and the domain I specified is added.
- 6318 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cortex XDR MITRE ATT&CK v16 -- We're Now on v19. Can We Talk About This? in Cortex XDR Discussions
- GlobalProtect Name Normalization issue in GlobalProtect Discussions
- Limit User-ID Agent queries to cerain Windows event-IDs in Next-Generation Firewall Discussions
- UserID periodic empty groups issue in General Topics
- The user information linked in the CIE does not match the match criteria in the GP's application settings. in Prisma Access Discussions