- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Rules not applying to AD groups
- LIVEcommunity
- Discussions
- General Topics
- Re: Rules not applying to AD groups
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-01-2012 01:57 AM
Hi,
For some reason my Palo Alto 2020 has stopped recognizing rules that are applied to AD user groups. My 2 User ID agents are running on the Domain controllers and are showing green on my Palo Alto box.
It works if I apply the rule to a specific AD user, so I know it is able to communicate with the ID agent otherwise it wouldn't register the user as logged on. It also lets me add the AD user group to a rule so it must be discovering the groups somehow. But when it comes to the web browsing rule, in this example, it doesn't apply the rule that is set for a user group.
The only thing different was that I moved a server into a different ip range last night and changed the necessary security and NAT rules. Although the network range that is being affected I didn't touch at all and didn't make any changes to point to or away from that range either, or the range it points to.
Any ideas? Is there anything I can look at on the ID agent to see why it would not be applying rules to AD groups?
- Labels:
-
Networking
-
User-ID
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-01-2012 09:13 AM
Since the security rules work when you apply individual user to the security policy and not the AD groups, it means that your user-ip mapping (done by user-id agent) is working correctly but not the user-group mapping. Did you make any changes to your LDAP settings ? Can you please check if the user is being associated with the groups properly using the command "show user group name <value>" . Make sure that the user is present in the AD group.
Which version of the user-id agent are using ? I am assuming you are using agent version 4.1.X in which user-ip mapping is done by the user-id agent and user-group mapping is done by the firewall (Device -> User Identification -> Group Mapping Settings). So you might want to double check these setting on the firewall.
Tx,
Sandeep T
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-01-2012 09:13 AM
Since the security rules work when you apply individual user to the security policy and not the AD groups, it means that your user-ip mapping (done by user-id agent) is working correctly but not the user-group mapping. Did you make any changes to your LDAP settings ? Can you please check if the user is being associated with the groups properly using the command "show user group name <value>" . Make sure that the user is present in the AD group.
Which version of the user-id agent are using ? I am assuming you are using agent version 4.1.X in which user-ip mapping is done by the user-id agent and user-group mapping is done by the firewall (Device -> User Identification -> Group Mapping Settings). So you might want to double check these setting on the firewall.
Tx,
Sandeep T
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-02-2012 11:07 AM
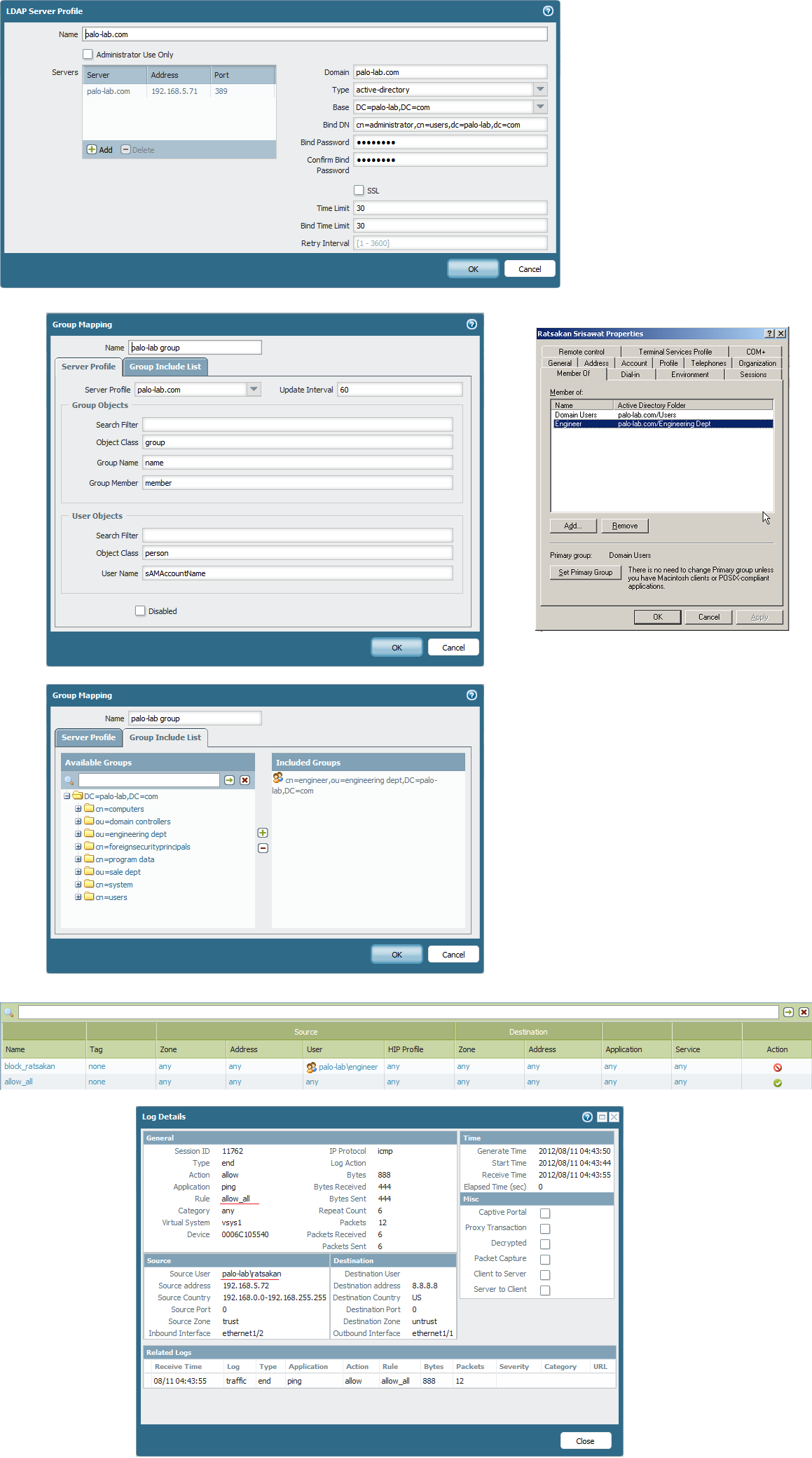
I ran into the same issue and found the problem was not with the userID agent, that's mapping things correctly as you mentioned, but with the bind point I had set within the LDAP server profiles on the PAN itself.
Device -> Server Profiles -> LDAP
I had the bind point set too low in the LDAP tree to enumerate userID's but high enough that it knew about the groups.
What I was seeing - I could apply policies to groups but users within those groups would not get the policy.
When I checked to see what users belonged to what groups (through CLI) I was not seeing any users as members of any groups.
Once I changed my LDAP bind point to be above both the group AND user OU's then PAN was able to map users to the proper groups and policies applied to groups started working fine.
YMMV, just something I ran into so maybe it helps. 😃
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-09-2012 10:07 PM
Hi rmgnetwork,
do you have an example ? I have run into this problem the same.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2012 12:19 AM
Setting the LDAP server profile and then the group mappings seems to have solved my problem.
Thanks everyone.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2012 12:27 AM
do you have any command on palo alto to check whether the user is in which group ?
i'm already set LDAP Server Profile and Group mapping but it doesn't work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2012 12:45 AM
One thing that I have noticed different on your configuration is that the Bind DN in the LDAP server profile. I put it in the format domain\administrator and then put in the admin password below it. Not sure if it would work for you but worth a shot.
I think there was a command you can use to check user groups, but I can't remember off the top of my head. I will see if I can dig it up for you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2012 08:15 AM
This command show the groups a given user belongs to:
show user user-IDs match-user palo\test-user
The following command shows the members of a given AD group:
show user group name "cn=domain users,cn=users,dc=palo,dc=local"
The 'group short name' works as well
show user group name "palo\domain users"
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2012 08:29 AM
It work fine now after I change domain in LDAP Server Profile to have no .com
Thank all
- 1 accepted solution
- 12444 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!




