- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
True test to verify dns sinkhole configuration is correct
- LIVEcommunity
- Discussions
- General Topics
- True test to verify dns sinkhole configuration is correct
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
True test to verify dns sinkhole configuration is correct
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2016 12:52 PM - edited 06-29-2016 01:01 PM
Hi Team,
We recently had a support case where a user followed all the guides on the kb and found that the sinkhole feature appeared to be not working. After a few quick tests we determined they had configured it correctly. The issue was the domains noted on some of the articles on the kb which used to be classed as malicious domains are no longer malicious.
For example the article here;
shows a nslookup against a malicious domain. This domain for whatever reason is no longer malicious. We can quickly verify this from the cli of the Palo Alto device.
admin@PA7050> test url sp-storage.spccint.com
sp-storage.spccint.com content-delivery-networks (Base db) expires in 0 seconds
sp-storage.spccint.com content-delivery-networks (Cloud db)
This caused the customer to think the configuration was incorrect.
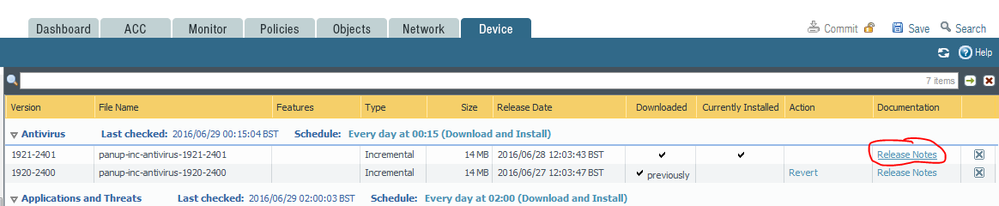
We advised the customer to check the release notes for the Antivirus dynamic updates installed on their device. This is a true test of the current malicious domains and we get the desired results.
Opening these release notes we get the new malicious domains as at todays date. It will include previous ones that are still malicious. But for testing we should use these.
There are articles that mention this. But its at the bottom of the article and can be overlooked. This article also lists domains that were malicious that are no longer classed as so. This can mislead users configuring this feature.
admin@PA7050> test url track.bidtrk.com
track.bidtrk.com not-resolved (Base db) expires in 0 seconds
track.bidtrk.com computer-and-internet-info (Cloud db)
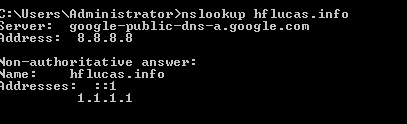
Checking the domains in the release notes we get the correct verdict and validate the configuration..
nslookups, digs or pings against the domains in the av release notes all return the correct verdict and get sinkholed. This is great for reporting as its there in the threat logs.
admin@PA7050> test url hflucas.info
hflucas.info not-resolved (Base db) expires in 0 seconds
hflucas.info malware (Cloud db)
This is a great feature to isolate infected hosts on the network and everyone with a PAN device should enable and configure this feature.
Hopefully this article clears up how to verify the configuration.
The links below shows how to enable it.
https://live.paloaltonetworks.com/t5/Configuration-Articles/How-to-Configure-DNS-Sinkhole/ta-p/58891
best regards,
Robert D
- 6409 Views
- 1 replies
- 3 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- MacOS uninstall password reset in Cortex XDR Discussions
- Difference in Session Synchronization configuration output in PAN-OS 11.2 Active/Passive HA in Next-Generation Firewall Discussions
- Config/System Logs Not Forwarding to Syslog Server in Next-Generation Firewall Discussions
- Upgrade from 10.1.12 to 11.1.13 in Panorama Discussions
- Inquiry Regarding CEF Configuration Guide and Custom Log Format Variables for PAN‑OS 11 in Next-Generation Firewall Discussions