- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
VPNC + PAN-OS 7.1
- LIVEcommunity
- Discussions
- General Topics
- Re: VPNC + PAN-OS 7.1
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-27-2016 04:00 AM
Does anyone use vpnc (As in the linux ipsec client) with xauth connecting to a PA?
We have a bunch o' PA's which we are in the middle of upgrading to 7.1 however once an upgrade from 7.0.6 to 7.1 is done, VPNC will no longer connect. Downgrading back to 7.0.6 again allows VPNC to connect.
The error in the logs is (ISAKMP_N_ATTRIBUTES_NOT_SUPPORTED)(13) which is not particularly informative. I have checked the globalprotect config and verified it is the same as our PA's running 7.0.6. At this point I have had to roll back the upgrade which has brought VPNC again into a working state.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-01-2016 03:23 PM
Use following command to resolve the issue:
set cli config-output-format set
configure
show | match "client-auth"
Now in output of last command you will get a line as follows:
set global-protect global-protect-gateway <gateway_name> client-auth <client_auth_name> os any
Change "any" to Any
set global-protect global-protect-gateway <gateway_name> client-auth <client_auth_name> os Any
commit
Hope this helps!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-02-2016 10:43 PM - edited 06-02-2016 10:57 PM
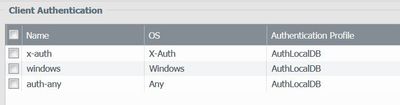
An additional work-around is to create an authentication reference pointed to the same authentication profile as the "Any" line specifically for X-Auth. The below worked in my proof-of-concept lab where I am testing 7.1.2.
EDIT: The orginal bug is indeed fixed in 7.1.2, however the bug-fix was not applied in my POC lab since I was upgrading from earlier 7.1 code. To truly fix the "Any" OS option if you find yourself in a similar corner-case rollback to 7.0.x and then re-upgrade to 7.1.2(+) so the migration script can slipstream the bugfix in.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2016 03:13 AM
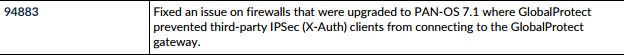
sound like the following bug which is fixed in PAN-OS 7.1.2:
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-01-2016 03:23 PM
Use following command to resolve the issue:
set cli config-output-format set
configure
show | match "client-auth"
Now in output of last command you will get a line as follows:
set global-protect global-protect-gateway <gateway_name> client-auth <client_auth_name> os any
Change "any" to Any
set global-protect global-protect-gateway <gateway_name> client-auth <client_auth_name> os Any
commit
Hope this helps!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-02-2016 10:43 PM - edited 06-02-2016 10:57 PM
An additional work-around is to create an authentication reference pointed to the same authentication profile as the "Any" line specifically for X-Auth. The below worked in my proof-of-concept lab where I am testing 7.1.2.
EDIT: The orginal bug is indeed fixed in 7.1.2, however the bug-fix was not applied in my POC lab since I was upgrading from earlier 7.1 code. To truly fix the "Any" OS option if you find yourself in a similar corner-case rollback to 7.0.x and then re-upgrade to 7.1.2(+) so the migration script can slipstream the bugfix in.
- 3 accepted solutions
- 6871 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Upgrade PANOS and SDWAN Plugin in Prisma SD-WAN Discussions
- PA-410 commit shows internal error and found that logdb-quota shows abnormal in General Topics
- OpenSSH CVE-2025-61984 on PANOS in Next-Generation Firewall Discussions
- HA failover on Acitve Passive concerns in Next-Generation Firewall Discussions
- Enable user context cloud service in IoT Security Discussions