- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Difference Between GlobalProtect Portal and GlobalProtect Gateway
- LIVEcommunity
- Discussions
- Network Security
- GlobalProtect Discussions
- Difference Between GlobalProtect Portal and GlobalProtect Gateway
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2023 02:36 AM
Read few of the docs but never understood the difference between the GP Portal and GP GW. Is there any way we can compare this with other vendor products and co-relate it? For example Cisco Anyconnect, Checkpoint Endpoint Security.
I wanted to know the actual difference and why few customers configure both Portal and Gateway.
Is it really necessary to configure both?
Regards,
Sanjay S
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-26-2023 11:15 AM
I am not familiar with Cisco Anyconnect (I have used Cisco ASA a tiny bit for site-to-site and user VPNs, but never did any user side config), but from your description I believe you are right. The GP Portal sets all the user side restrictions and options. There are a couple user configuration options through the GP Gateway (user VPN IP address, split tunnel networks, etc), but everything else comes from the GP Portal.
The basic config options for the user can be found under:
Network -> GlobalProtect -> Portals -> [portal_config] -> Agent -> [agent_config] ->
App - GP client settings including VPN mode (on-demand/always-on), Portal config lifetime, password policies, user bypass options, etc.
External - GP Gateways the client will connect to with preference/geolocation options
Internal - Internal network VPN bypass and internal gateways for HIP data collection
Network -> GlobalProtect -> Gateways -> [gateway_config] -> Agent -> Client Settings -> [client_config] ->
Authentication Override - whether to accept/generate cookies for overriding user authentication for Portal/Gateway login
IP Pools - IP subnet to allocate client VPN IPs from
Split Tunnel - Networks/domains to always split-tunnel and exclude from forcing through the VPN
Network -> GlobalProtect -> Gateways -> [gateway_config] -> Agent
-> Network Services - client DNS servers
Network -> GlobalProtect -> Gateways -> [gateway_config] -> Agent
-> Connection Settings - GP Gateway connection lifetime
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2023 08:00 AM
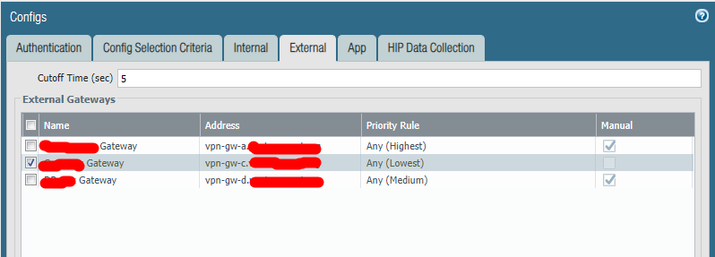
You enter one or more gateway addresses in the GP Portal config under:
Network -> GlobalProtect -> Portals -> [portal_config] -> Agent -> [agent_config] -> External
Every Portal config can have one or more agent configs, which send different config options to the client based on authenticated userID, hardware checks, etc. Each External Gateway entry for an agent config has the following options:
- A name (which will appear in the GlobalProtect client "Gateway" selection if you allow users to choose gateways)
- An address which can be a FQDN or IP address
- A gateway selection priority with option to set priority by client source address region (the client will evaluate all available Gateways for their region and connect to the "best" based on several factors)
- A manual enable checkbox that will allow the user to manually select that Gateway (the user can change to a different gateway)
There is also a tab for Internal Gateways. If you enable internal host detection the client will attempt to determine if the PC is locally connected to an internal company network and, if so, bypass the External Gateway and connect the user directly. If an Internal Gateway is set the client will connect to the Internal Gateway instead, though there doesn't need to be one for internal-only connections.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2023 08:28 AM
I don't know if you can really compare it to Cisco/Checkpoint, but yes both the Portal and the Gateway are required. The GP Portal is where the GP client connects to get its configuration data: client side settings/network restrictions and a list of which Gateways to connect to. The GP Gateway is where the GP client connects to establish the tunnel that client VPN traffic will actually flow over.
The reason these are separate is that the GP configuration point and the data point can be on completely separate interfaces or devices. So you can have one or more GP Portals that push different configurations to different clients with a set of preferred Gateways. Those Gateways can be scattered across the world with the client choosing the best Gateway for its connectivity. You can also have different Gateways for different types of clients, based on the Portal config, i.e. your corporate users go to one Gateway, your contractors go to a different Gateway, with the same Portal.
In most cases PA users are probably using a single Portal and Gateway setup. In my setup I have multiple PAs with 4 different public interfaces, each running a Portal and Gateway. End users being users... most people always select the first VPN Portal in their GP client. If you only had a single Portal/Gateway association then all the clients would be on the same public interface/PA. With multiple Gateways I can make the GP clients automatically load balance across all the available Gateways (and fail to a different Gateway if the primary is unavailable) regardless of which Portal the user selected. This also means that I can remove a Gateway from the Portal client config and have users automatically move off it (over time) to perform maintenance or test new configurations, without having to tell every end user to change their VPN Portal setup.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-23-2023 12:29 AM
Thank you Adrian for the detailed information.
I believe GP Portal is very much similar to the XML profile in Cisco Anyconnect. As XML profile will control all user controllable settings of Anyconnect Client. GP Portal does the same in Palo Alto Global Protect Client.
Hope my understanding is right now?
Regards,
Sanjay S
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-26-2023 11:15 AM
I am not familiar with Cisco Anyconnect (I have used Cisco ASA a tiny bit for site-to-site and user VPNs, but never did any user side config), but from your description I believe you are right. The GP Portal sets all the user side restrictions and options. There are a couple user configuration options through the GP Gateway (user VPN IP address, split tunnel networks, etc), but everything else comes from the GP Portal.
The basic config options for the user can be found under:
Network -> GlobalProtect -> Portals -> [portal_config] -> Agent -> [agent_config] ->
App - GP client settings including VPN mode (on-demand/always-on), Portal config lifetime, password policies, user bypass options, etc.
External - GP Gateways the client will connect to with preference/geolocation options
Internal - Internal network VPN bypass and internal gateways for HIP data collection
Network -> GlobalProtect -> Gateways -> [gateway_config] -> Agent -> Client Settings -> [client_config] ->
Authentication Override - whether to accept/generate cookies for overriding user authentication for Portal/Gateway login
IP Pools - IP subnet to allocate client VPN IPs from
Split Tunnel - Networks/domains to always split-tunnel and exclude from forcing through the VPN
Network -> GlobalProtect -> Gateways -> [gateway_config] -> Agent
-> Network Services - client DNS servers
Network -> GlobalProtect -> Gateways -> [gateway_config] -> Agent
-> Connection Settings - GP Gateway connection lifetime
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2023 11:46 PM
Hi Adrian,
This explains me everything i needed. Thank you very much for spending time for me and explained soo well.
Last question. Where do i configure the FQDN for the gateway IP address in GP portal or GP gateway? So that users should use the FQDN to connect to GP.
Regards,
Sanjay S
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2023 08:00 AM
You enter one or more gateway addresses in the GP Portal config under:
Network -> GlobalProtect -> Portals -> [portal_config] -> Agent -> [agent_config] -> External
Every Portal config can have one or more agent configs, which send different config options to the client based on authenticated userID, hardware checks, etc. Each External Gateway entry for an agent config has the following options:
- A name (which will appear in the GlobalProtect client "Gateway" selection if you allow users to choose gateways)
- An address which can be a FQDN or IP address
- A gateway selection priority with option to set priority by client source address region (the client will evaluate all available Gateways for their region and connect to the "best" based on several factors)
- A manual enable checkbox that will allow the user to manually select that Gateway (the user can change to a different gateway)
There is also a tab for Internal Gateways. If you enable internal host detection the client will attempt to determine if the PC is locally connected to an internal company network and, if so, bypass the External Gateway and connect the user directly. If an Internal Gateway is set the client will connect to the Internal Gateway instead, though there doesn't need to be one for internal-only connections.
- 2 accepted solutions
- 21116 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Globalprotect Client 6.2.7 disconnects multiple times in GlobalProtect Discussions
- Global Protect count current users not match statistics in GlobalProtect Discussions
- Enforce GlobalProtect Access Based on Microsoft Intune Compliance Status in GlobalProtect Discussions