- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Whatsapp File transfer Block
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- Whatsapp File transfer Block
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Whatsapp File transfer Block
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-15-2022 12:21 AM
i work as a security specialist engineer at a moderate
enterprise.
recently my superiors have asked me to block whatsapp file transfer only(meaning chat would still work).
however i've tried anything using our Fw's but to no avail.
from what i have read on some forums and various sources, i need to url block
mmi.whatsapp
mms and mmv..
i tried doing that yet it didn't seem to help.
i can still upload/download files from both
whatsapp web and the desktop application.
is it possible to
get support from you on this matter please?
is blocking ft even achievable?
thank you so much,
best regards,
Thomas.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-15-2022 07:00 AM
Hi Thomas,
You would need to be blocking the Whatsapp file-sharing application, are you able to see this application on your firewall? To be able to you will need to be decrypting the Whatsapp traffic.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2022 02:40 AM
Hi Thomas,
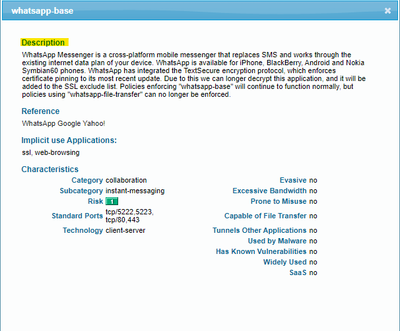
On the firewall, the application description says,
WhatsApp has integrated the TextSecure encryption protocol, which enforces certificate pinning to its most recent update. Due to this we can longer decrypt this application, and it will be added to the SSL exclude list. Policies enforcing "whatsapp-base" will continue to function normally, but policies using "whatsapp-file-transfer" can no longer be enforced.
Unfortunately firewall cannot see what is sent by the client in an encrypted packet (chat/upload, etc). Furthermore, the application does not like to get decrypted as it uses end-to-end encryption. This means that even if we do SSL inspection we won’t be able to see the content of a message.
Although you can block the URLs to which the traffic is traversing provided we have the SNI information, however from my personal experience, these URLs keeps changing from time to time.
Regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2022 03:30 AM
Hi Michael,
thanks for your reply.
unfortunately,
i have already tried blocking both whatsapp file sharing and
whatsapp-base applications on the
fw yet that didn't seem to do anything.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2022 03:31 AM
Hi Ahandoo,
thank you.
i actually tried to block these applications, yet
to no avail.
also, can you please elaborate on the SNI Information?
what exactly is it? and how do i obtain it?
thank you .
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2022 04:50 AM - edited 08-17-2022 11:55 PM
Hi Thomas,
SNI is the Server Name Identification field present in the Client Hello of SSL/TLS Handshake. It allows the client to indicate the hostname which it is trying to connect. For more information , you can refer to this link.
You will have to take network trace or packet capture to know this information.
We can find multiple videos on youtube on how to find the SNI from a packet capture. You can check this video.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-21-2022 04:04 AM
Hello,
i still haven't managed to sort this issue out,
we're considering using a different solution
as it appears to be un-solvable by the looks
of it.
thank you all for your contribution.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2022 12:29 PM
Hi @Thomasevig
There is a lot of work associated with blocking/allowing URLs, not only for this but for a wide variety of scenarios. It can be tricky sometimes.
My lab experience using the URL Filtering profiles allowed me to block Whatsapp upload of images & videos while allowing the messages to be sent. I am sharing it if it can help.
Created a URL Category including
mmg.whatsapp.net/
*.cdn.whatsapp.net
Created a URL filtering profile and set the above created URL category to block.
Added the URL filtering profile to the rule which matches the Whatsapp traffic.
Note: In order to get the list of the URLs to block, I took a packet capture on the host which was running the Whatsapp application or the Whatsapp web.
Regards,
Arnesh
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2022 09:31 AM
We are seeing the same behavior with our policy.
It looks like at the moment Palo-Alto is unable to provide solution to block whatsapp file transfers.
The method suggested above using URL categories also doesn't seem to work.
If anyone have some other solution for this problem it would be very helpful.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2022 01:23 AM
hello,
is there any other workaround we can implement?
has anyone tried anything
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-08-2022 05:48 AM - edited 12-08-2022 06:48 AM
I know this thread seems to be a few months old, but I wanted to add that I had to do this exact thing this morning on one of our FWs and it worked fine.
Whats-app chat and calls are still allowed.
however, file transferring (even voice notes) is not.
The rule I used looks like:
Basically, everything WhatsApp needs to work is allowed in this rule, except the 'whatsapp-file-transfer' application
Our catch-all-block-rule at the end of our security policies will catch the file transfers, which is not explicitly allowed anywhere, and block them.
We don't have any special decryption configured either. Palo Alto correctly classifies all this traffic so we could create this rule without issue.
We are using a PA460, on Firmware 10.2.3 if this helps.
@Thomasevig perhaps check your monitoring on the FW, while doing a file transfer on WhatsApp to see if your traffic is correctly classified. If yes, then this rule should work for you.
tbh - I was trying to get only uploads on WhatsApp blocked, with downloads still working. But I was unable to get this working. It is either a block all file transfer or nothing it seems.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2023 02:40 AM
You can test if enabling SSL decryption just for the destination FQDN/IP addresses of WhatsApp out of working hours if it starts working.
Also there is an application debug that have described in the discussion below, so if you want to play again outside working hours you can try "Other use case that I know is to see the application shift if there is an issue how the Palo Alto changes the matched application by enabling the "appid" debug. "
- 24152 Views
- 11 replies
- 2 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!