- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
AWS IPSEC VPN ISSUES with redundant tunnels
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- Re: AWS IPSEC VPN ISSUES with redundant tunnels
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2018 08:34 AM
Hi
We have around 6 different IPSEC tunnels configured on the PAN with AWS. However we are trying to troubleshoot an issue, which we think could be related to as asymmetric routing. For e.g if traffic is send from one tunnel, and AWS sends it via the 2nd tunnel, the PAN will be dropping these.
So we have temporary disabled one of the active tunnels - we have tried enabled ECMP on the palo alto, don't think this is working either.
We have configured the tunnel on different security zones, so not sure if this is correct way?
Anybody have any experience with setting up 2 redundant tunnels with AWS, that works. The suggested options are enabling BGP - which we don't have experience with.
Kind Regards
Anu
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2018 04:35 AM
The issue was we were trying to seperate the 2 vpn tunnels in 2 seperate zone - which can make the pan think - packets are spoofed. Moving them to the same zone, did the trick
Thanks for the help.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2018 02:14 PM
in order for ECMP to work it must be configured on both ends and at this stage it is not supported in the AWS VGW unless something has changed.
in Github for our transit VPC architecture we do have a manual deployment guide. In that manual deployment guide it will walk you through
1. How configured VPN tunnel from PAN with AWS
2. How to configure BGP for the transit VPC architecture
The use case may not be completely the same but it should be close enough to get you going. Here are the links
Here is a link on how to propagate the default route after you have configured BGP
Hope this helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2018 01:54 AM
Thanks JPerry, for taking the time to suggest the 2 options. Am fairly new to the aws world, so excuss me if i use the wrong terminology. So from what I imaging, the transit vpc is using a VM series palo alto FW's in the AWS enviroment to connect to the on prem Palo alto's. So this will need to be an investment from our end to purchase the licences for this series. Is that correct.
Kind regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2018 01:02 PM - edited 11-15-2018 01:03 PM
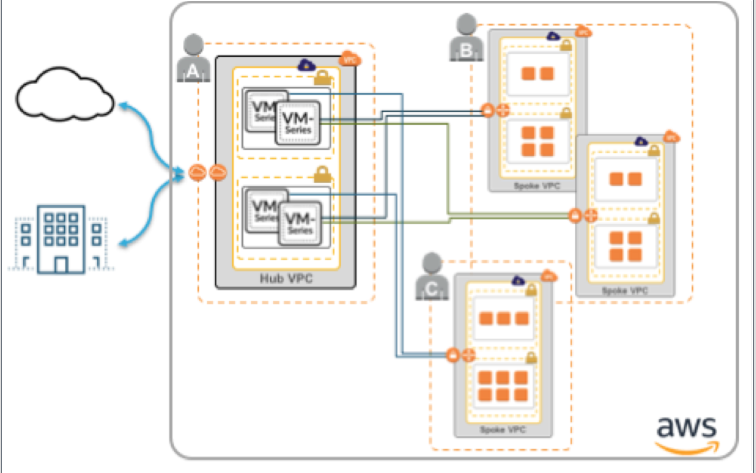
Transit VPC is using two firewalls in a "Transit VPC Hub" to terminate VPN connections back to one or many VPC Spokes using the AWS VGW. If you choose to connect your Transit VPC Hub back to an On-Prem location you can use any IPSec device you have on premises to accomplish this.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2018 04:35 AM
The issue was we were trying to seperate the 2 vpn tunnels in 2 seperate zone - which can make the pan think - packets are spoofed. Moving them to the same zone, did the trick
Thanks for the help.
- 1 accepted solution
- 17157 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Request Advice – BGP Failover Route-Based IPsec VPN With WatchGuard (WG) in Next-Generation Firewall Discussions
- SPlit tunneling issue on GlobalProtect in GlobalProtect Discussions
- Intermittent IPSec Tunnel Monitoring Issue in Next-Generation Firewall Discussions
- GP Split Tunnel in Windows 11 Issue in GlobalProtect Discussions
- UserID Redistribution Filters working weirdly in Next-Generation Firewall Discussions