- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Palo VM300 Azure routing issues?
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- Palo VM300 Azure routing issues?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Palo VM300 Azure routing issues?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2018 09:50 AM
Working with a Palo VM300 series in Azure and have some issues that I just can't figure out...
We have the VM inside of a 10.x.x.x/16 subnet. 1 subnet (10.x.x.x/24) carved for each of the interfaces (trusted, un, mngmt) and 4 more subnets for various other VMs and such. We have UDRs setup for all 3 interfaces as well as a UDR setup for the other subnets. The plan is to push all traffic in, out, and between subnets through this single Palo unit.
We have 2 virtual routers built out; 1 for trusted, and 1 for untrusted interface. Trusted VR receives traffic internal and pushes internet traffic to the Untrust VR, and all traffic meant for subnet cross traffic is supposed to be forwarded to the Trust interface gateway and then should get to the correct subnet (barring any rules).
What we see is when trying a ping; the icmp is allowed through the rules, but then ages out so no reply back from the second VM. I believe there's an issue in these VRs but I can't seem to track it down. I've seen a lot of docs showing that Palo can be run in 1 vnet/multiple subnets with 1 interface but not really sure how this works. My only other FW experience is SonicWall so 1 port 1 zone makes sense but the 1 port many zones sure doesn't.
Anyone know what to look for in either the Palo or Azure? I'm really not even sure the Azure UDRs are correct but everything I've read points to them being right (Palo documentation and online forums) so really I'm kinda at a brick wall on where to go next. Hopefully all of this makes sense as this is my first rodeo working with Palo and Azure.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2018 10:45 AM
Question 1. Is there a particular reason that you are using two separate VRs?
If not I am not a fan for unecessary complexity but if you have a valid reason then please feel free.
If you use a VR you have to be sure to route traffic between VR's correctly by using the "Next VR" setting etc or you could have a black hole.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2018 10:56 AM
We are a small company right now and don't have a full time Network Engineer/Admin/etc. so there's 2 of us that are trying to make all of this work with a consultant. The consultant built 2 VRs as I assume for some sort of extra security but I don't understand what they really do. I assume they are similar to say a SonicWall's route section; just done in something called Virtual routers but I can't be sure (the different lingo Palo uses is confusing to me as well but that's no biggie).
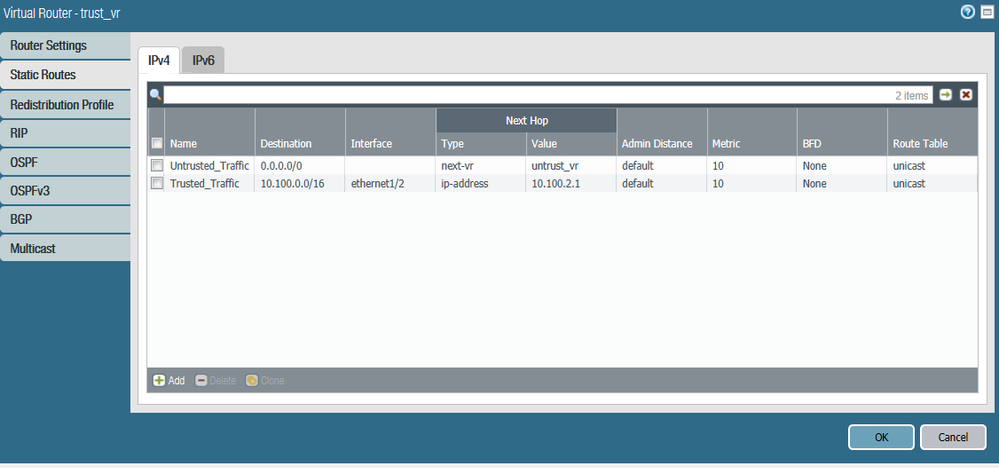
Here's the Trust VR settings:
This looks like it shunts all internet traffic over to the Untrust interface VR to handle, and then shunts all inter-subnet traffic to the gateway that the Trust interface is attached to. I would assume that gateway would know where the other subnets are once traffic hits that but it looks like we're missing something somewhere as traffic just dies at some point..
Maybe we are missing routes? I understand Palo can do all this with 1 interface as we've been thinking about dropping extra NICs on the VM into each subnet to see if that helps but would hate to do that since it's not what Palo docs say for this type of setup.
Thanks!
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2018 11:41 AM - edited 09-14-2018 11:50 AM
Are you using Azure load balancers in this scenario?
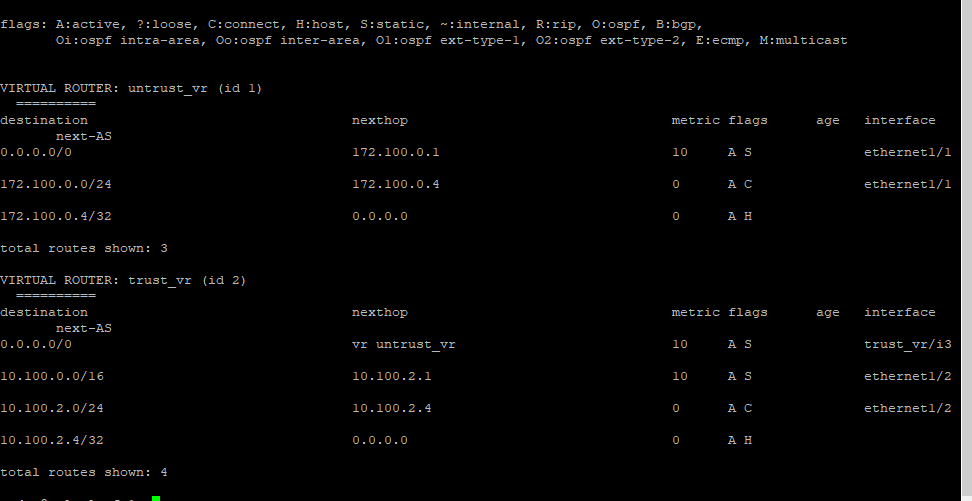
Also if you can go to your CLI and run the command
>show routing route
Paste the output
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2018 12:04 PM
We are not using any load balancers right now.
After running the command provided here's what I see:
Thanks!
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2018 01:10 PM
Your untrust VR needs to have routes for "NextVR" in order to understand how to get back to the 10.x.x.x networks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-18-2018 08:51 AM
Hello,
I second @jperry1 recommendation of a single VR, unless there is an absolutle compelling reason to use multiple. Especially for a small shop such as yours. The simpler it is setup the easier it will be on you to manage it.
Regards,
- 8310 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect Name Normalization issue in GlobalProtect Discussions
- Azure to OnPrem Connectivity issue in Next-Generation Firewall Discussions
- Issue after onboard Azure VM into SCM in Strata Cloud Manager
- Panorama managed - Global protect SAML cert renew - IDP xml import wrong expiry in GlobalProtect Discussions
- Azure Virtual Desktops integration with Global Protect nightmare in GlobalProtect Discussions