- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Paloalto Firewall and VPC peering
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- Re: Paloalto Firewall and VPC peering
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Paloalto Firewall and VPC peering
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2022 03:43 AM
i am confuse AWS network firewall and peering section.
As per AWS documents, it said
**AWS Network Firewall cannot be deployed to inspect traffic between VPCs that are peered together; **
this mean AWS network firewall cannot support.
So let me know paloalto can support below scenario ?
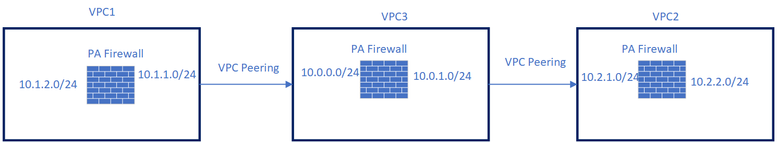
i did vpc peering VPC 1 (10.1.1.0/16)and VPC2 ( 10.2.1.0/16).
VPC 1 have one private subnet ( 10.1.2.0/24) behind the PA firewall
VPC 2 have one private subnet ( 10.2.2.0/24) behind the PA firewall
I have the one private route table destination 10.2.2.0/24 next hop is firewall interface in VPC 2.
I add one route to go 10.2.2.0/24 next hop is peer ID in VPC one private route.
I have the one private route table destination 10.1.2.0/24 next hop is firewall interface in VPC 1.
I add one route to go 10.1.2.0/24 next hop is peer ID in VPC 2.
let me know this traffic will pass firewall ?
can we use PA firewall to inspect traffic of private network(10.1.2.0/24 and 10.2.2.0/24) of two vpc which it is peering?
I don't want to use transit gateway.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-24-2022 08:10 AM
Hi @sthornton ,
Sorry for misunderstanding. I want to go VPC1 to VPC2 passthrough VPC3 PA firewall without using transit gateway and VPN.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-24-2022 11:25 AM
This is a very odd setup. Why do you have a firewall in every VPC? By default subnet-2-subnet traffic within a VPC is not going to be inspected by the PA. it would be more practical to use VPC3 as the primary "Security VPC" inspecting traffic passing between VPCs.
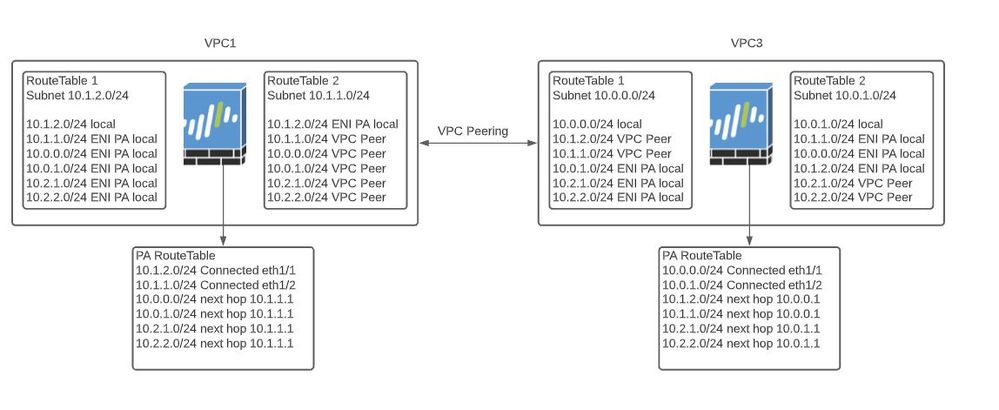
With that said, your design CAN work but you would need a RouteTable in every subnet, please see below. I only included VPC1 and VPC3, you can duplicate the configuration for VPC2.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-24-2022 11:29 AM
Another thing to keep in mind is that if you added more subnets within the VPCs you would need to consider the PA VM instance size. I believe you need a C4xLarge just to have the proper number of interfaces to place in each subnet. With more than 4 interfaces you would need to go to bigger instance size and it will start getting pricey.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-24-2022 06:25 PM
Hi @DanaHawkins ,
When i read Doc, all are said need Transitgateway. I want to do VPC3 as security VPC and traffic VPC1 to VPC2 pass through VPC3 for inspection. is it possible without using Transit gateway ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2022 06:15 AM
You achieve what you want with VPC peering using a design similar to the picture I posted above. Transit Gateways give you the benefit of Availability Zone redundancy and using BGP for route propagation between the firewalls and AWS. Using VPC peering all route table configurations are manual for both the firewall and AWS.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2022 09:48 AM
I do not believe this is possible. This would be transitive routing and would require an intermediary to accomplish.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2022 02:22 PM
The firewall is acting as the intermediary. VPC peer allows for connecting of resources between VPCs. @sthornton You are right that, if there was no firewall, or another intermediary, within the VPC then you would not be able to communicate from VPC1 to VPC2 via VPC3.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2022 02:31 PM - edited 02-25-2022 02:33 PM
Unsupported VPC peering configurations
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-28-2022 09:39 AM
This would be true if you were only using AWS native constructs but introducing the Palo Alto FW in the "Transit" VPC would allow you to pass traffic/inspect traffic by sending traffic to a VPC subnet ENI resource to another subnet ENI resource. In effect, the Palo Alto FW becomes the "transit router" for the VPC.
VPCs as AWS native constructs are non-transitory in nature but a FW can act as the bridge.
- 8466 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Alto Networks PSE Hardware Firewall Professional (Strata) in Next-Generation Firewall Discussions
- Panroma using public ip in Panorama Discussions
- Step by Step Radius Configuration for PA-1410 in Next-Generation Firewall Discussions
- About BUG PAN-226361 for PA-820 device running version 10.2.10-h9 in Next-Generation Firewall Discussions
- Microsoft WNS App ID in Next-Generation Firewall Discussions