- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Tips and Tricks: Filtering the Security Policy
- LIVEcommunity
- Articles
- General Articles
- Tips and Tricks: Filtering the Security Policy
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
The content you are looking for has been archived. View related content below.
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 01-16-2024 12:30 PM
Digging into the depths of policy details can be quite the task, especially after a long and tiring day. But fear not, handy search tools are here to lighten your load!
Here's how it works: Simply pop in a keyword related to what you're hunting for. This could be the name of a policy (just squish it into one word), an IP address or object name, maybe an application, or even a service.
Keep in mind though, wildcards (like *) aren't supported. You'll need a partial or an exact match.
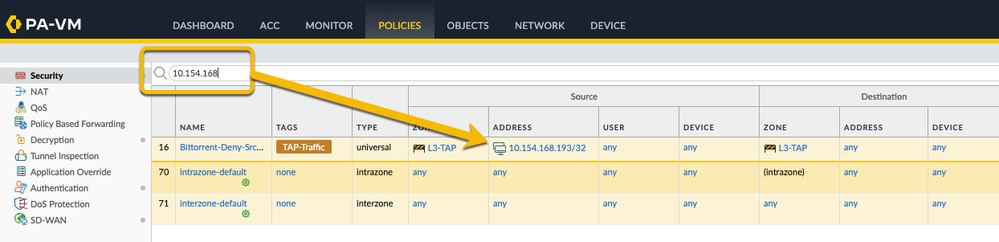
Add a partial IP address and you'll get all the partial and exact matches in the result:
Want to narrow things down even further? You can target your search to specific fields like the source zone or application. And guess what? There’s a super handy drop-down function that sets up your search filter in a snap. Easy-peasy!
You can also create a search string manually. I've provided a list of all fields below:
Name: (name contains 'unlocate-block')
Tags: (tag/member eq 'tagname')
Type: (rule-type eq 'intrazone|interzone')
Source Zone: (from/member eq 'zonename')
Source Address: (source/member eq 'any|ip|object')
Source User: (source-user/member eq 'any|username|groupname')
Hip profile: (hip-profiles/member eq 'any|profilename')
Destination Zone: (to/member eq 'zonename')
Destination Address: (destination/member eq 'any|ip|object')
Destination User: (destination-user/member eq 'any|username|groupname')
Application: (application/member eq 'any|applicationname|applicationgroup|applicationfilter')
Service: (service/member eq 'any|servicename|application-default')
URL Category: (category/member eq 'any|categoryname')
This is a destination category, not a URL filtering security profile
Action: (action eq 'allow|drop|deny|reset-client|reset-server|reset-both')
Action send ICMP unreachable: (icmp-unreachable eq 'yes')
Security Profiles:
(profile-setting/profiles/virus/member eq 'profilename')
(profile-setting/profiles/spyware/member eq 'profilename')
(profile-setting/profiles/vulnerability/member eq 'profilename')
(profile-setting/profiles/url-filtering/member eq 'profilename')
(profile-setting/profiles/file-blocking/member eq 'profilename')
(profile-setting/profiles/wildfire-analysis/member eq 'profilegroupname')
(profile-setting/group/member eq 'profilename')
Disable server response inspection: (option/disable-server-response-inspection eq 'yes')
Log at session start: (log-start eq 'yes|no')
Log at session end: (log-end eq 'yes|no')
Schedule: (schedule eq 'schedulename')
Log Forwarding: (log-setting eq "forwardingprofilename')
Qos Marking: (qos/marking/ip-dscp eq 'codepoint')
(qos/marking/ip-precedence eq 'codepoint')
(qos/marking/follow-c2s-flow eq '')
Description: (description contains '<keyword>')
Disabled policy: (disabled eq yes|no)
policies will only respond to 'no' if they have been disabled before
As you can see in the examples above the operands are 'contains' and 'eq' (=equals).
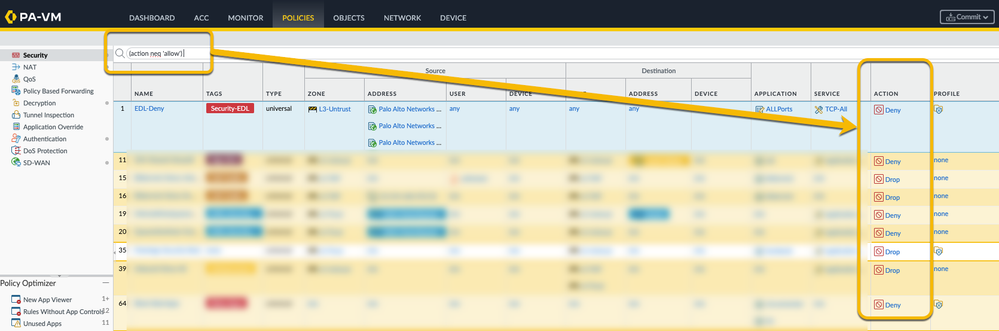
Note that you can also use the negate option using the operand 'neq' (=not equals).
For example, here's how you can use the negate option to list all the rules that do NOT have a ALLOW action: (action neq 'allow'):
Tag Browser can also come in very handy if you're able to tag all your security policies. It can be used in a similar way as the search function and display only the selected tags.
More information and a tutorial video on the Tag Browser can be found here: Tutorial: Tag Browser
Hope this was helpful, feel free to ask questions or post remarks below.
Thanks for taking time to read this blog.
Don't forget to hit that Like (thumbs up) button and don't forget to subscribe to the LIVEcommunity Blog.
Stay Secure,
Kiwi out!
Hi @BYates ,
You can filter on the columns. Click the arrow next to the column name. From there select "Columns" and you can check/uncheck all the columns you would like to see.
You can also drag/drop the columns to change the order you would like to see.
As far as I know there is no filter option in the search bar at the top to filter out certain columns that way.
Still not what you need ? In that case custom reports also allow you define specific colums in the report.
Hope this helps,
-Kim.
If you want to filter for Rule ID which is called UUID the filter is:
(uuid eq xyz)
Hi @J_Healy ,
You can't seem to add a filter based on modified date on the policies tab.
However, knowing the modified date should allow you to do a Config Audit (Device tab > Config Audit) for that date/config version and verify all the changes in the config (including the rules).
If that doesn't provide you the requested information then a feature request might be in order.
Hello Team,
Can I create filter to see only rules in specific Device Group. I have device group which have 3 parent Device Groups and there are 500 rules coming from them. This is pre-rules, so every time I have to scroll down to the local rules for the Device Group. Can I filter only for local rules in this Device Group without seeing all the rules coming from parents?
Kind Regards
- 62403 Views
- 10 comments
- 18 Likes
- Tips & Tricks: Palo Alto Global Counters for Layer 1 to Layer 4 issues troubleshooting like MTU and DOS in General Articles
- Support FAQ: Flood Attacks - Configuration & Troubleshooting Best Practices in Support FAQ
- Tips & Tricks: App-ID Debugging in General Articles
- Demystifying Selective Push on Panorama in General Articles
- Support FAQ: How to Troubleshoot BGP on Palo Alto Networks Firewalls in Support FAQ
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
1 -
AI Security
1 -
AIOPS
1 -
Ansible
1 -
antivirus
1 -
API
1 -
App-ID
1 -
applications
2 -
APS
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
3 -
aws
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
6 -
Block List
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud ngfw
1 -
cloud security
1 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Configuration
8 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
CPSP
1 -
Custom Signatures
3 -
cyber elite
1 -
cyberelite
11 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
2 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
3 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector Design
2 -
Logging
1 -
login
1 -
Logs
3 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
network security
34 -
Network Security Management
1 -
network-security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
30 -
NGFW Configuration
11 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
16 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Prisma Access
1 -
Panorama
11 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
5 -
Prisma AIRS
1 -
Prisma SD-WAN
1 -
proactive insights
2 -
Radius
1 -
Ransomware
1 -
region
1 -
Registration
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Site-to-Site VPN
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
2 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Terraform
2 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
6 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
7 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next





