- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Block List not working
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Re: Block List not working
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Block List not working
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2022 06:58 AM
hey,
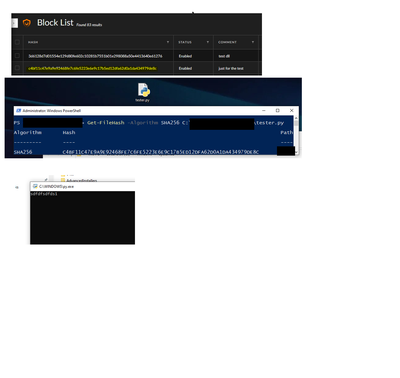
just for testing I created python file and extract the hash. after that added the hash to the "Block List".
click on "check-it now", run the python file and nothing happened!.
someone know what could be the problem?
thanks 🙂
First pic - the rule.
Sec pic- the hash
Third pic - the prove about non block file. (the python script himself)
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2022 07:15 AM
Hi Oriavs,
The reason this is not working is .py files are not supported for the hash block/allow lists. See the documentation here for supported file types by operating system for this functionality.
Thanks,
Ben
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2022 07:34 AM
Bbucao is correct, what is executing is not the .py file, but the python interpreter, so you can't blacklist a python script directly.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2022 10:03 AM
Hi Oriavs,
I imagine these hashes came from some type of threat intel feed? If that is the case and you want to leverage them in Cortex XDR I recommend creating IOC rules by navigating to Detection Rules > IOC > + Add IOC, then you can select to create these rules individually for each hash, or upload via a file. When these rules are created, Cortex XDR will alert anytime these hashes are seen in your logs. Now to be clear, this will not block anything, but will alert you if one of these hashes is seen so you can investigate the traffic. If you are just wanting to search for and remove files based on hash, you can use the File Search and Destroy feature if you have the "Host Insights" add-on license.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2022 10:59 PM
Hi, and thanks Ben.
there is way to block IOCs?
bc alert doesn't help me, in case of attack I don't need to know about it, I need to block it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2022 06:22 AM
Hi Oriavs,
As data is streamed into the XDR cloud tenant from your XDR agents or other sources, the IOC rules are applied against that data to identify any matches. Since this is happening in the cloud versus at the agent there is no ability to perform blocking actions on IOC rules.
Cortex XDR uses a multi-method approach to stop both known and unknown threats including behavioral prevention and malware sandboxing which look at the actual behavior a file creates on a system. This is inherently more reliable then tracking static IOC's because one of the easiest things a threat actor can do is change a file hash which makes that IOC useless. It is much harder for the threat actor to change the overall behavior of their malware, or their Tactics Techniques and Procedures. Because of how easy it is to change a files hash, or file name, or change an IP address, static IOC's are known to have a very short shelf life before they become irrelevant compared to more modern and advanced detection methods. I find IOC's are most beneficial in a real-time use-case, where I am responding to an active threat and am pulling these IOC's from the identified malicious traffic in my network, then adding them as rules into Cortex XDR to help identify the scope of the Incident. You can view a list of the endpoint protection modules Cortex XDR leverages here.
Best Regards,
Ben
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2022 06:43 AM
Thanks about the answer.
I know behavior is much better then hashes.
But still, why I should care about who many hashes in the block list?
I have very good sources to receive hashes when attacker release payload to the big world, so why not?
why Palo Alto don't give me the option to block any type of file?
thanks again.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2022 12:48 PM
Hi @Oriavs
If I am following this threat correctly, then you are looking for a way to block file exception based on file hash. You can add sha-256 hashes to the block list within the action center. This workflow is documented in the Manage File Execution tech. doc.
- 7375 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Is there an API to add IPs to Cortex XDR EDL programmatically? in Cortex XDR Discussions
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- Issue with IOC not blocking MyPDFSwitch executable in Cortex XDR Discussions
- Cortex Pop-ups Triggered for StoreDesktopExtension.exe Despite Being Blocklisted in Cortex XSIAM Discussions
- Block Execution of Specific Applications Regard of version in Cortex XDR Discussions