- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Extract Domains from Phishing Attached Email
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XSOAR Discussions
- Extract Domains from Phishing Attached Email
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Extract Domains from Phishing Attached Email
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-29-2022 06:31 AM
Hi Team,
I hope all are doing well; how can I extract the domains from the phishing attached files?
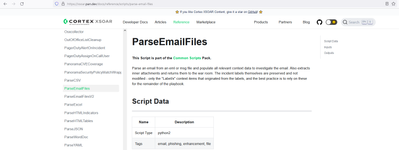
I extracted the email using " ParseEmailFilesV2 "; exported all the email parameters such as HTML and others successfully; however, once I tried to convert HTML XML output to JSON using "ConvertXmlToJson" automation, it did not work as expected.
I need to convert HTML - XML format to JSON with all domains available to be appended; any idea, team, how I can achieve it?
Thanks
Basel
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2022 01:55 AM - edited 11-02-2022 01:56 AM
Hi Basel,
If you run the ParseEmailFilesV2 automation with the "auto-extract=inline" argument, all domains will be extracted from the email too, into the ${Domain.Name} context.
Alternatively you can also run "extractIndicators" on the ${Email} key (after running ParseEmailFilesV2), then the domains will be extracted under ${ExtractedIndicators.Domain}. Attached an example:
Regarding the conversion, I'm not sure what XML you are referring to, we would need to see the XML, the command you ran, the expected result and the actual result.
Let me know if that helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2022 07:03 AM - edited 11-07-2022 07:06 AM
I never knew there were so many premade parsing scripts. @ivandijk is right about this. Better try ParseEmailFilesV2 as Ivan mentioned but there is an old one on python2 just in case but python2 is just supported for existing scripts and intergrations so you may not create a new script using the original one https://xsoar.pan.dev/docs/integrations/code-conventions so better use the V2.
- 3083 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- WHOIS Integration - Connection Refused Errors in Cortex XSOAR Discussions
- Cloud Identity Engine: New Agent Version Alert in Cortex XDR Discussions
- Phisphing feeds and enrichment in Cortex XSOAR Discussions
- Automate Reported Phishing Email Attachments to CrowdStrike Falcon Sandbox w/ XSOAR in Cortex XSOAR Discussions
- Help with feeds in Cortex XSOAR Discussions