- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Keeping Your Google Cloud VPC Networks Highly Resilient and Secured
- LIVEcommunity
- Articles
- General Articles
- Keeping Your Google Cloud VPC Networks Highly Resilient and Secured
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 07-10-2023 10:06 AM
This document describes the use-cases, architecture design and traffic flows for Palo Alto Networks VM-Series deployed in Active-Passive mode in Google Cloud. The Active-Passive architecture provides several advantages over the Active-Active architecture like stateful failover, eliminates several source NAT requirements, and can be used for static IPSec termination. This document is intended for network administrators, solution architects, and security professionals who are familiar with Compute Engine, Load Balancing and Virtual Private Cloud (VPC) networking.
About VM-Series Next-Generation Firewalls
The VM-Series NGFW helps enterprises secure their applications, users, and other data deployed across Google Cloud and other virtualization environments.
Palo Alto Networks delivers zero-trust security capabilities for all enterprise networks by using the following approaches to threat prevention:
- Securing all applications with Layer-7 inspection, granting access based on user identification, and preventing known and unknown threats.
- Segmenting mission-critical applications and data using zero-trust principles to improve security posture and achieve compliance with various security standards—for example, PCI DSS.
- Using Panorama to centrally manage both physical and virtual firewalls. Panorama helps provide a consistent security posture across all hybrid and multi-cloud environments.
- Using tooling to automate the deployment and configuration of VM-Series NGFWs.
- Using predefined and custom network tags within security policies to dynamically update objects as Cloud workloads are created, moved, and destroyed.
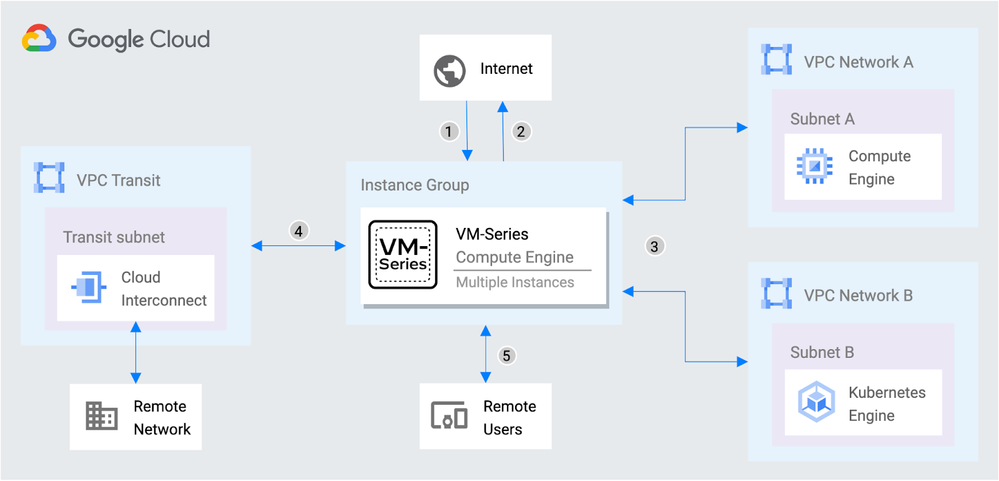
The VM-Series NGFW helps secure workloads deployed across both your VPC networks and your remote networks. Consider the following ways that the VM-Series NFGW can help to secure network patterns. The items in the following list correspond to the numbers in the following diagram.
- Prevent inbound threats from the internet to resources deployed in VPC networks, on-premises, and in other cloud environments.
- Stop outbound connections from VPC networks to suspicious destinations, such as command-and-control servers, or malicious code repositories.
- Prevent threats from moving laterally between workload VPC networks and stealing data.
- Secure traffic between remote networks connected through Cloud Interconnect, Network Connectivity Center, or Cloud VPN.
- Help extend security to remote users and mobile devices to provide granular application access to Google Cloud resources.
For more information, see VM-Series Virtual Next-Generation Firewalls.
Architecture
The architecture is very similar to the traditional Load Balancer (LB) architecture recommended for GCP in which the external LB points manages the untrust traffic and an internal LB manages the trust/egress or east-west traffic.
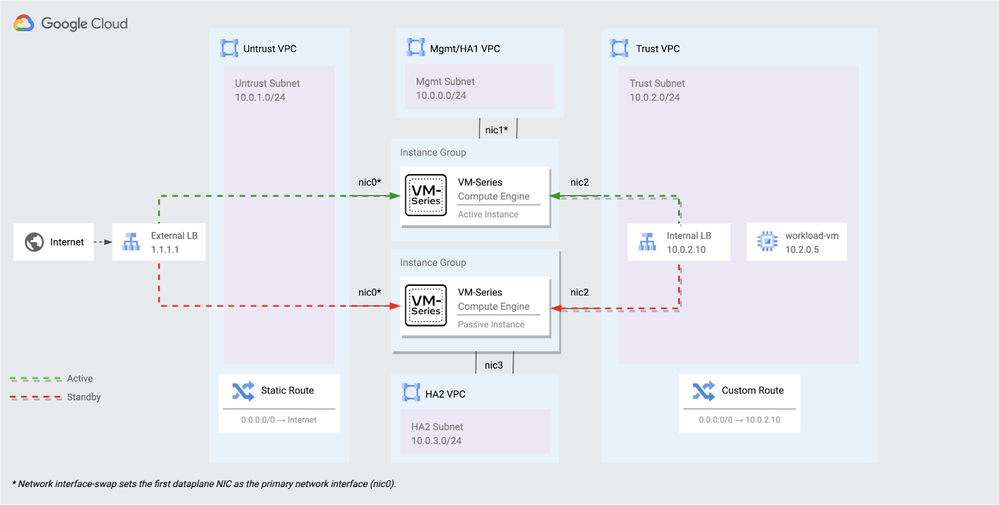
In the above architecture diagram, the VM-Series firewalls are deployed in an Active-Passive pair. Each firewall belongs to an Unmanaged Instance Group that is deployed to separate zones within the same region. Each firewall has four interfaces: MGMT/HA1, untrust, trust, and HA2, and each interface is connected to a dedicated VPC network.
Components
The following sections explain the network components in more detail.
Unmanaged Instance Groups
Each firewall is associated with an Unmanaged Instance Group, deployed across different zones to ensure redundancy and fault tolerance. The Instance Group allows the VM-Series to function as the backend service for Google Cloud's network load balancers. In the load balancer configuration, each instance group is designated as an active backend service. However, the health check performed by the load balancer towards the passive firewall will fail since its dataplane is inactive.
Backend Service
The Backend Service contains a crucial piece of configuration that would enable session stickiness on failover. The “Connection Tracking Policy” on the Backend Service configuration should have the following values:
- Tracking Mode – Per Session
- Connection Persistence on Unhealthy Backends – Never Persist
- Idle Timeout Seconds – 600 seconds
It must also be noted that the Session Affinity on the Backend Service configuration should be set as “None” for best results.
External Load Balancer
The external TCP/UDP load balancer forwards inbound traffic from the internet to the untrust interface of the active VM-Series firewall. It also serves as the internet gateway for egress traffic from Google Cloud resources protected by the VM-Series. For the VM-Series to receive traffic from any external load balancer, a management interface swap must be performed. The swap enables the untrust interface to serve as the primary interface of the compute instance.
Internal Load Balancer
The internal TCP/UDP load balancer forwards outbound traffic from Google Cloud resources to the trust interface of the active VM-Series firewall. Custom routes are defined in the workload networks to use the internal TCP/UDP load balancer’s forwarding rule as the next hop.
HA2 Network
In addition to the three VPC Networks that are required for Management, Untrust and Trust traffic arriving at the VM-Series firewalls, we need another VPC Network, HA2, that will be specifically used for session synchronization between the active and passive firewalls. The configuration synchronization will be performed using the Management network.
VM-Series Configuration
The VM-Series firewalls are configured as an Active-Passive pair. Configuration changes are automatically synced across the firewalls. It is crucial that the firewalls have identical licenses and are running the same PAN-OS version. This ensures consistency and compatibility between the firewalls, enabling seamless failover and synchronization of configurations and policies.
Traffic Flows
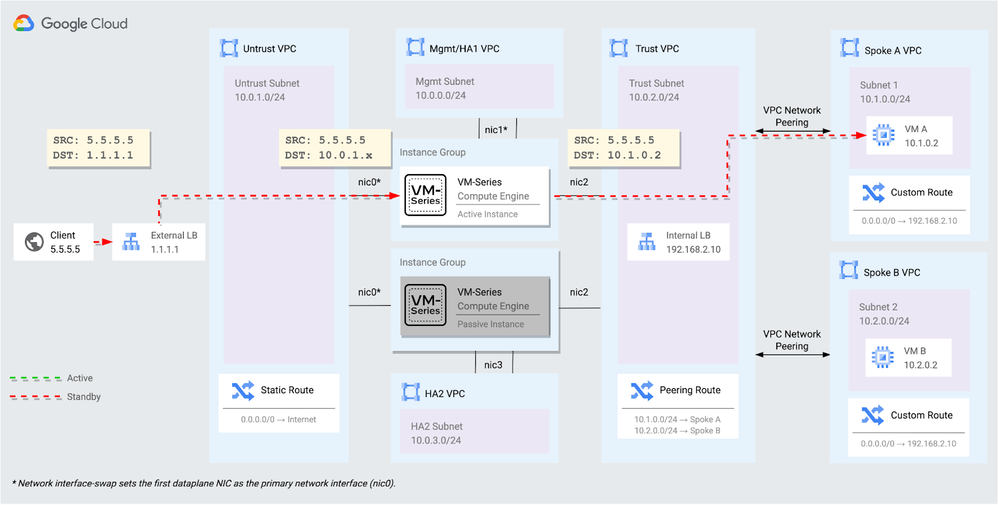
Incoming traffic flows
The diagram below illustrates how incoming traffic flows are processed with the Active-Passive architecture. The External Load Balancer, being a pass-through service, passes the flows onto the Active VM-Series firewall. The VM-Series firewall performs Destination NAT on the traffic to forward the flows to the intended destination after processing. Because the workload network has a default route returning the internal load balancer, source NAT is not required.
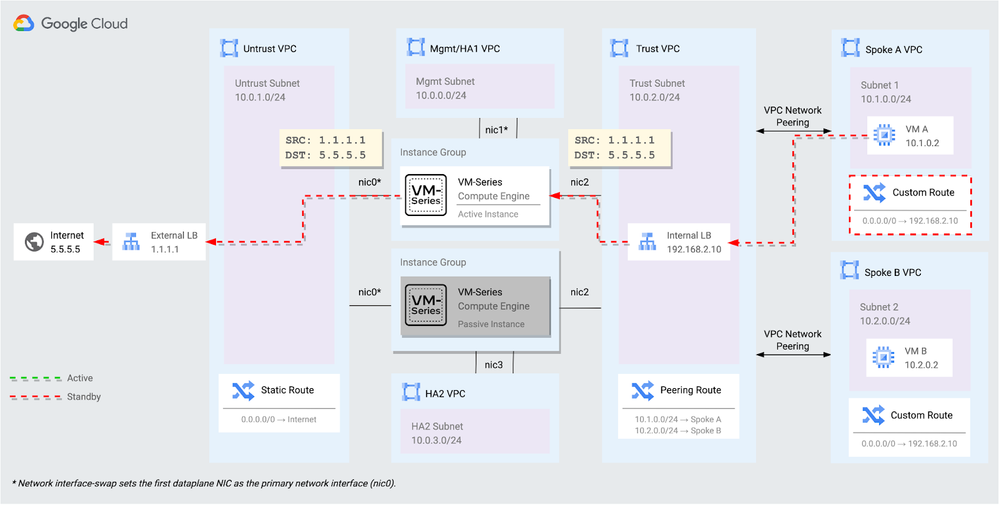
Outgoing traffic flows
The diagram below illustrates how outgoing traffic flows are processed with this architecture. All traffic flows originating from the internal networks are forwarded to the Internal Load Balancer through custom routes. The VM-Series applies a source NAT to translate the traffic to the external load balancer’s forwarding rule.
Use Cases
The Active-Passive architecture design for VM-Series Next-Generation Firewalls provides solutions for some of the requirements that cannot be achieved through the Active-Active design with Autoscaling like;
Session synchronization and Stateful failover
With this design, we can achieve Session Synchronization and Stateful failover in case the Active Firewall goes down. Furthermore, the stateful failover can be achieved as quickly as 3 seconds.
IPSec termination of Site-to-Site VPN Tunnels
By using the public IP address of the External Load Balancer as the VPN Gateway, we can now terminate the IPSec tunnels directly on the VM-Series firewalls, thereby achieving highly available and resilient VPN connections.
No SNAT Solution
Some legacy applications may need visibility into the original source client IP address. With this design, there is no inherent need to apply Source Network Address Translation on the incoming traffic flows as traffic symmetry is always maintained.
Costs
The VM-Series firewall supports the following license types:
- BYOL
- PayGo
It also supports the following two licensing models:
- Software Next Generation firewall credits: Flexible configurations that you specify with a deployment profile
- Fixed VM-Series Model configurations
Both models license security services and other features.
For more information on licensing, see VM-Series Firewall Licensing.
The VM-Series uses the following billable components of Google Cloud:
For more information, see License the VM-Series Firewall. To generate a cost estimate based on your projected usage, use the pricing calculator. New Google Cloud users might be eligible for a free trial.
Performance
Palo Alto Networks Single-Pass Architecture processes the following items only once:
- Network policy enforcement
- Application identification
- User controls
- Content inspection
This check significantly reduces the processing overhead required to perform multiple functions on a single device. For more information, see VM-Series on Google Cloud Performance and Capacity.
What’s Next?
- Learn about how to automate the VM-Series Active-Passive design on Google Cloud using Terraform.
- Learn about the VM-Series on Google Cloud.
- Learn about VM-Series licensing on all platforms.
- Learn about Performance and Sizing for VM-Series on Google Cloud.
- Watch the VM-Series capabilities in Google Cloud.
Hi community,
Regarding IPSec termination of Site-to-Site VPN Tunnels
"By using the public IP address of the External Load Balancer as the VPN Gateway"
You mean VPN Gateway at the Palo Alto site when you create the IPSec Tunnels pointing to the GCP External LB public IP?
Not the VPN Gateway concept for the Cloud VPN google cloud managed service.
Right?
Thanks in advanced
Hello Fran,
Thank you for your comment.
Yes, assuming you have IPSec tunnels originating from any source, including other Palo Alto NGFWs, the remote IP address for tunnel termination will be the public IP address of External LB on this active-passive architecture.
Thank you!
Thanks for your reply @shv .
We already have implemented this Palo Alto HA reference architecture. Let me kindly share our issues with the following Palo Alto configuration:
- 2x virtual router:
vr-trust:
- ethernet 1/2
- Loopback.1: 100.64.0.1/32
- Static Routes for GCP probes for Internal LB to ethernet 1/2
- Static default 0.0.0.0/0 to next vr-untrust
- NAT policy from GCP probes to ethernet 1/2 and DNAT loopback.1
vr-untrust:
-ethernet 1/1
-Loopback.3: 100.64.0.2/32
-Loopback.2: IP External LB GCP
-Static Routes for GCP probes for External LB to ethernet 1/1
- Static default 0.0.0.0/0 to ethernet 1/1
-NAT policy from GCP probes to ethernet 1/1 and DNAT loopback.3
With this design We have incoming traffic flowing to the spokes in GCP through the External LB and Health check traffic from Google probe successfully running. NAT rules for inbound and health checks are OK
For Outgoing traffic If We configure loopback 2 for the source NAT policy to translate the traffic to the external load balancer’s forwarding rule the NAT policy for health-check prob untrust with the loopback.3 fails and all the ingress traffic and health checks fails. Traffic from the health probes to the External LB trying to DNAT using loopback.2 instead of loopback.3.
Do you know How can we solve this issue?
And the last one related to IPSec termination from any source to the external LB We understand that passthrough Network Load Balancers are not proxies. Load-balanced packets are received by backend VMs with the packet's source and destination IP addresses, protocol, and, if the protocol is port-based, the source and destination ports unchanged. Load-balanced connections are terminated at the backends. Responses from the backend VMs go directly to the clients, not back through the load balancer. So the traffic flow from the source peer VPN Gateway to the External LB and the response is directly from the untrust Interface, not the external LB IP. Do we need to NAT outgoing traffic from untrust zone to untrust zone to the loopback.2 as well? Source vpn Gateway are waiting to recevie traffic from the Public IP of the External LB.
Thanks in advanced! We appreciated your support on these issues.
- 17243 Views
- 3 comments
- 2 Likes
- Google Cloud Network Security Integration (NSI) in General Articles
- Achieving Defense-in-Depth with Advanced DNS Security and Remote Browser Isolation in General Articles
- Why It's Essential to Secure Your Management Interface in General Articles
- Empowering and Securing Banking and Financial Organizations in General Articles
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
ADNS
1 -
Advanced DNS Security
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
2 -
AI Security
1 -
AI Threat
1 -
AIOPS
1 -
Analytics
1 -
Ansible
2 -
antivirus
1 -
API
2 -
API & SDK
1 -
App-ID
1 -
applications
2 -
APS
1 -
Artificial Intelligence
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
6 -
AWS
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
8 -
Block List
1 -
Cardinality
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CI CD Integration
1 -
CICD integration
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud logging
1 -
cloud ngfw
1 -
Cloud security
2 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Compliance
1 -
Configuration
9 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Container
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
Cortex XSIAM
1 -
Cortex XSOAR
2 -
CPSP
1 -
Custom Signatures
3 -
custom-featured-post
1 -
cyber elite
1 -
cyberelite
13 -
Cybersecurity
1 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
DLP
1 -
Docker
2 -
Dual Forwarding
1 -
dual forwarding behavior
1 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
End to End Encryption
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
fire and forget logging
1 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
3 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
GKE
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
4 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
HyperLogLog
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector
1 -
Log Collector Design
2 -
Log Collector vs SLS
1 -
Log Management
1 -
Logging
1 -
Logging & Reporting
1 -
login
1 -
Logs
3 -
logs missing in SLS
1 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
Network Security
35 -
Network Security Management
1 -
Network-Security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
31 -
NGFW Configuration
12 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Dual Forwarding Mode
1 -
PAN-OS log forwarding
1 -
PAN-OS log loss
1 -
PAN-OS logging
1 -
PAN-OS logging architecture
1 -
PAN-OS migration to SLS
1 -
PAN-OS Prisma Access
1 -
Panorama
12 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
7 -
Prisma AIRS
1 -
Prisma SASE
2 -
Prisma SD-WAN
1 -
proactive insights
2 -
Prompt Poaching
1 -
Public Cloud
1 -
Python
2 -
Radius
1 -
Ransomware
1 -
RBI
2 -
region
1 -
Registration
1 -
Remote Browser Isolation
3 -
Reporting
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Single Forwarding
1 -
Site-to-Site VPN
1 -
SLS best effort delivery
1 -
SLS log delivery
1 -
SLS log fidelity
1 -
SLS missing logs
1 -
Software Firewalls
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
3 -
Strata Logging Service (SLS)
1 -
Strata Logging Service troubleshooting
1 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Technical Architecture
1 -
Terraform
3 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
7 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
Upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
8 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WhatsApp
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next





