- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Nominated Discussion: VLAN Confusion
- LIVEcommunity
- Articles
- General Articles
- Nominated Discussion: VLAN Confusion
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 04-04-2023 10:56 AM - edited on 11-04-2024 05:32 PM by JayGolf
This Nominated Discussion Article is based on the post "VLAN Confusion" by @bgre033 and responded to by @seb_rupik and @Raido_Rattameister . Read on to see the discussion and solution!
I’ve recently got a PA-440, and trying to make sense of the VLAN logic on PAN-OS has got me stumped.
First of all, I get creating a layer 3 sub interface and assigning a VLAN tag, easy. A bit odd that the 'tag' doesn't then show up as a VLAN under Network > VLANs, but I can let that slide.
It's an access port where things really don't make sense. I follow the steps below, and even though it works it just doesn't make sense.
- Mark an interface as layer 2, and assign a layer 2 zone to it, ok.
- Create a VLAN (Network > VLANs) - sure, but you don’t specify a VLAN ID, just a name. What is the point of this construct?
- Assign created VLAN (from step 2) to the physical layer 2 interface - again, ok, but given the VLAN hasn’t got an ID, does this achieve anything?
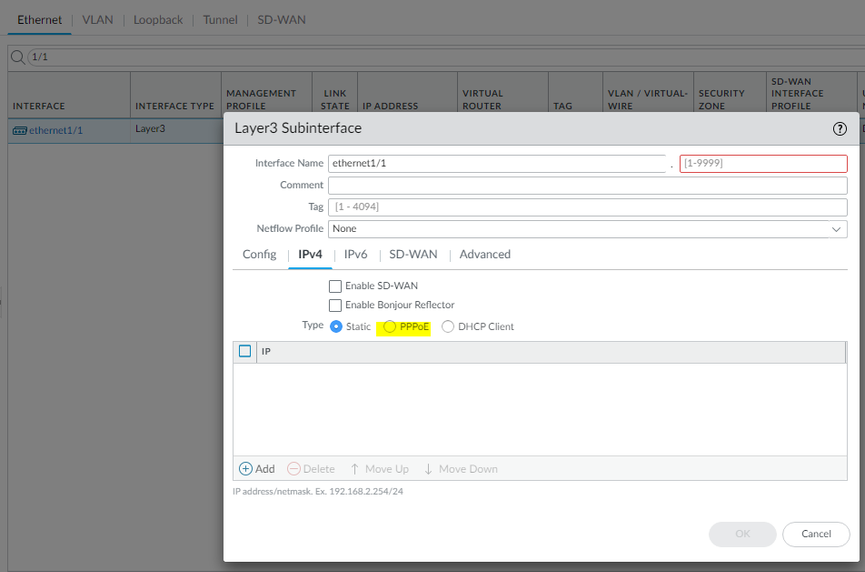
- Create a VLAN Interface (with an ID between 1-9999) and assign a VLAN to it. I assume this is like an SVI, but I don’t need a layer 3 VLAN interface, why is this necessary? Also, it seems like the ID is meant to be the VLAN tag (but the range is not right, 1-9999 rather than 1-4094)?
I'm hoping someone can explain this to be, as the documentation isn't clear.
- What is the point of VLANs under Network > VLANs? Given you don't specify a VLAN ID.
- Is the ID under the VLAN interface actually a VLAN tag, rather than an interface ID? If so, why is the range 1-9999 (rather than 1-4094)?
Palo Alto has taken the approach of decoupling the VLAN ID from the VLAN virtual-bridge construct. When you create a VLAN object under Network -> VLAN, the name is the UID not a VLAN ID as would be the case on a cisco. The object you create here is a virtual-bridge which is used to bind the various Layer 2 interfaces defined Network -> Interfaces -> Ethernet and a single SVI under Network -> Interfaces -> VLAN.
The ID number which is required by a sub-interface or VLAN/SVI interface is arbitrary. The tag number, which is selected under the sub-interface, is the VLAN ID and is used for the 802.1Q encapsulation. The sub-interface ID and tag number do not have to match, but it can help with readability!
It is worth noting that this decoupling of VLAN ID from the VLAN object means that sub-interfaces, which uses different 802.1Q tags, can use the same VLAN virtual-bridge effectively performing VLAN tag rewriting.
This would suggest that an access port cannot exist (for example) in VLAN 20 unless a sub-interface has been created with tag '20' and both of these objects have been associated with a VLAN object (Network > VLAN)? Suppose this doesn't really matter, as an access port VLAN ID isn't relevant unless a trunk port exists somewhere on the said device (which it won't unless sub-interfaces have been created).
Finally, I take it a VLAN sub-interface (Network > Interfaces > VLAN) isn't needed unless inter-VLAN routing is required?
It is always easier to set interfaces in Layer3. The main interface will be untagged and sub-interfaces will tag packets.
- Layer2 makes sense only if you deploy firewalls in small office with few devices and you don't have a dedicated switch (all devices connect directly to Palo) and you need multiple interfaces to be in same subnet/vlan
- Other reason to use Layer2 is if you have existing setup. Let's say a web server and database servers were historically deployed in a single VLAN. You want to separate them and place a firewall in between
What you can do is connect web server and database server directly to the PA Firewall. Set the firewall interfaces in Layer2 and create a policy in between to permit only specific traffic. As a result, no re-IP needed but security posture improved.
Once you configure a Layer2 sub-interface you are creating a trunk link and 802.1q will be enabled, using the 'tag' value as the VLAN ID on the encapsulated frame. An access port doesn't really need a VLAN tag, as it is never imposed on the frame, they arrive and leave untagged. The VLAN tag/ID is there purely to identify which virtual-bridge the frames belong to.
The object created under Network -> Interfaces -> VLAN is not a sub-interface. I understand the confusion as it prepends a digit to the interface name. The interface here is a SVI/IRB . If you have configured your firewall interfaces all as Layer2, then yes you will need these for inter-VLAN routing. You can have a mix of routed Layer 3 interfaces (dedicated or sub-interface) and VLAN interfaces for inter-VLAN routing, depending on your topology.
Once you get to PAN-OS 11.x you can configure PPPoE on sub-interface.
- 6458 Views
- 0 comments
- 0 Likes
- Nominated Discussion: Configure Split Tunneling by Domain in General Articles
- Nominated Discussion - Sorting Question in General Articles
- Nominated Discussion: Using the REST API to Create a Bunch of Address Objects in General Articles
- Nominated Discussion: Check Which IP Address (or User, AD Group) is Utilizing More Bandwidth in General Articles
- Nominated Discussion: PDF Report Generated and Date Is Not In Order in General Articles
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
ADNS
1 -
Advanced DNS Security
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
2 -
AI Security
1 -
AI Threat
1 -
AIOPS
1 -
Analytics
1 -
Ansible
2 -
antivirus
1 -
API
2 -
API & SDK
1 -
App-ID
1 -
applications
2 -
APS
1 -
Artificial Intelligence
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
6 -
AWS
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
7 -
Block List
1 -
Cardinality
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CI CD Integration
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud ngfw
1 -
Cloud security
2 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Configuration
8 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Container
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
Cortex XSOAR
2 -
CPSP
1 -
Custom Signatures
3 -
custom-featured-post
1 -
cyber elite
1 -
cyberelite
13 -
Cybersecurity
1 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
DLP
1 -
Docker
2 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
End to End Encryption
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
3 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
GKE
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
4 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
HyperLogLog
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector Design
2 -
Log Management
1 -
Logging
1 -
login
1 -
Logs
3 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
Network Security
35 -
Network Security Management
1 -
Network-Security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
31 -
NGFW Configuration
12 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Prisma Access
1 -
Panorama
12 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
7 -
Prisma AIRS
1 -
Prisma SASE
2 -
Prisma SD-WAN
1 -
proactive insights
2 -
Prompt Poaching
1 -
Public Cloud
1 -
Python
2 -
Radius
1 -
Ransomware
1 -
RBI
2 -
region
1 -
Registration
1 -
Remote Browser Isolation
3 -
Reporting
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Site-to-Site VPN
1 -
Software Firewalls
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
2 -
Strata Logging Service (SLS)
1 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Terraform
3 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
7 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
Upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
8 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WhatsApp
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next