- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Upgrading VM Series Firewalls Behind Load Balancer in AWS
- LIVEcommunity
- Articles
- General Articles
- Upgrading VM Series Firewalls Behind Load Balancer in AWS
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-28-2023 09:49 PM - edited 09-28-2023 10:28 PM
Have you ever encountered discussions about planning a VM series upgrade or wondered about the fate of existing connections during a firewall upgrade? How can firewalls be upgraded with minimal impact and downtime? This article aims to address these queries and provide guidelines for an upgrade process.
Modern businesses employ the Gateway Load Balancer framework to incorporate security insertion. You have the ability to customize health check preferences for specific target groups. By default, general settings are in place unless changed during the initial creation of the target group or in subsequent adjustments. The Gateway Load Balancer actively monitors the well-being of targets within active Availability Zones and routes requests to those healthy targets.
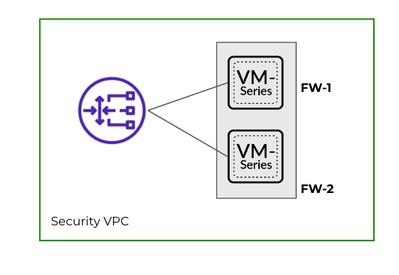
For the purpose of this article, let us consider a topology where we have 2 VM Series firewalls: FW-1, FW-2 as part of a target group, deployed behind a GWLB . Both these firewalls show as healthy in the target group.
To upgrade the firewalls, You can take into consideration below factors to ensure minimal downtime.
1. De-Register FW-2 from the Target Groups (Check if the firewall is part of multiple ALB target-groups and de-register it from all). When you deregister a target, it is taken out of your target group. The Gateway Load Balancer ceases to direct traffic to a target immediately upon de-registration. The target enters the draining state. The GWLB waits for the de-registration delay timer (attribute of Target Group) to change the state of a de-registering target from draining to unused. The default value is 300 seconds (5 min). It can be modified in the target group settings. The range is 0-3600 seconds.
During this time of de-registration delay timer any new connections would not be forwarded to it by GWLB.
Existing connections get specified seconds to complete. Post the delay timer, existing connections will be forcefully terminated as well. Hence if there are any remaining sessions they will experience disconnection.
2. After waiting for the de-registration delay timer, FW-2 should stop receiving any traffic. and now we can upgrade the VM series and reboot. There is no downtime since the FW-1 will handle all the connections.
3. Once the FW-2 is back, register it in the target group. This Firewall should show up as healthy in the Health Check of. FW-2 is ready to accept the connections at this stage.
4. The new connections can now be forwarded to FW-2 by GWLB.
We can now repeat the same steps from step 1-3 and deregister FW-1 from GWLB so that it enters the de-registration delay timer. We will upgrade the firewall, reboot and add it back to the target group to start processing traffic.
There is very minimal downtime experienced if the upgrade is carried out in this manner. You can follow these guidelines for multiple firewalls. It is always recommended to take backup of configuration before performing any maintenance activity.
Note: For more information on how to rebalance existing flows in case the target is in de-registration / unhealthy state, please refer to the AWS article: Introducing AWS Gateway Load Balancer Target Failover for Existing Flows
- 12500 Views
- 2 comments
- 2 Likes
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
ADNS
1 -
Advanced DNS Security
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
2 -
AI Security
1 -
AI Threat
1 -
AIOPS
1 -
Analytics
1 -
Ansible
2 -
antivirus
1 -
API
2 -
API & SDK
1 -
App-ID
1 -
applications
2 -
APS
1 -
Artificial Intelligence
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
6 -
AWS
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
8 -
Block List
1 -
Cardinality
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CI CD Integration
1 -
CICD integration
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud logging
1 -
cloud ngfw
1 -
Cloud security
2 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Compliance
1 -
Configuration
9 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Container
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
Cortex XSIAM
1 -
Cortex XSOAR
2 -
CPSP
1 -
Custom Signatures
3 -
custom-featured-post
1 -
cyber elite
1 -
cyberelite
13 -
Cybersecurity
1 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
DLP
1 -
Docker
2 -
Dual Forwarding
1 -
dual forwarding behavior
1 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
End to End Encryption
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
fire and forget logging
1 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
3 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
GKE
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
4 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
HyperLogLog
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector
1 -
Log Collector Design
2 -
Log Collector vs SLS
1 -
Log Management
1 -
Logging
1 -
Logging & Reporting
1 -
login
1 -
Logs
3 -
logs missing in SLS
1 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
Network Security
35 -
Network Security Management
1 -
Network-Security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
31 -
NGFW Configuration
12 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Dual Forwarding Mode
1 -
PAN-OS log forwarding
1 -
PAN-OS log loss
1 -
PAN-OS logging
1 -
PAN-OS logging architecture
1 -
PAN-OS migration to SLS
1 -
PAN-OS Prisma Access
1 -
Panorama
12 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
7 -
Prisma AIRS
1 -
Prisma SASE
2 -
Prisma SD-WAN
1 -
proactive insights
2 -
Prompt Poaching
1 -
Public Cloud
1 -
Python
2 -
Radius
1 -
Ransomware
1 -
RBI
2 -
region
1 -
Registration
1 -
Remote Browser Isolation
3 -
Reporting
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Single Forwarding
1 -
Site-to-Site VPN
1 -
SLS best effort delivery
1 -
SLS log delivery
1 -
SLS log fidelity
1 -
SLS missing logs
1 -
Software Firewalls
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
3 -
Strata Logging Service (SLS)
1 -
Strata Logging Service troubleshooting
1 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Technical Architecture
1 -
Terraform
3 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
7 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
Upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
8 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WhatsApp
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next