- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Cisco ISE integration for UserID
- LIVEcommunity
- Discussions
- General Topics
- Cisco ISE integration for UserID
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2021 03:58 PM
Greetings all,
I'm wondering if anyone else is using Cisco ISE for network access control and has experience integrating it to publish User ID to the Palo Alto firewalls?
I saw a support article for it but the regex appears to be out of date. I found another guide somewhere else that suggested using field identifiers instead of regex which is what I did. I now can get User ID for devices logging in to an 802.1x SSID, for example.
My next challenge is device that use MAC authorization, or MAB. I know this isn't really a recommended practice but since we have on-campus housing, we need to support some SSIDs/networks that utilize this for all of those consumer devices that don't support better security like 802.1x. I believe ISE is publishing these RADIUS connections to the firewall, however, they appear as device MAC addresses which is going to make user-based firewall rules difficult.
I know the username for the device when logging in to a MAB protected network technically is the MAC address, but we've used a previous solution for network access control that would instead publish the owner's username (i.e. the username they used to register/enroll the device) and I'm wondering if there is another way to implement the ISE/Palo connection that would give us the owner's username for these connections vs the MAC address?
Thanks!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2023 06:17 PM
Hi @AhmedAlRashed ,
It works for me. This URL has instructions for ISE guest, but it works for all authentications -> https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Cm5sCAC. There is another URL in @raji_toor 's response as well. @jsalmans told you what filters he used to get it working.
I use these filters:
Event Regex: ([A-Za-z0-9].*CISE_Passed_Authentications.*Framed-IP-Address=.*)|([A-Za-z0-9].*CISE_RADIUS_Accounting.*Framed-IP-Address=.*)
Username Regex: User-Name=([a-zA-Z0-9\@\-\\/\\\._]+)|UserName=([a-zA-Z0-9\@\-\\/\\\._]+)
Address Regex: Framed-IP-Address=([0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3})
It works great. It gets wired and wireless. It gets the domain/ma-c0-0a-dd-re-ss of MAB devices. MAB (MAC authentication bypass) will not give you a username because EAP is bypassed. If someone wants something more descriptive for devices, they may look into Device-ID.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2021 04:17 PM
This might help you with integrating userid from ISE with PA, this is what I had followed. But I am not sure if using a device registered under MAB would use the userid or MAC.
http://k12itdir.blogspot.com/2016/02/paloalto-user-id-from-cisco-ise-nodes.html
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-26-2021 08:45 AM
Thanks for the link! I think I had actually found it already and was using it as a reference.
What I determined is that the radius messages sent by ISE actually contain multiple username fields. UserName tends to be the actual user's ID and User-Name seems to be the machine's ID. In the case of 802.1x then they're both the user's ID but with devices registered through ISE's MyDevice's portal and that use MAB authentication the fields are different. Here is what I ended up doing so far:
Event Identifier: NOTICE Radius-Accounting:
Username Regex: (?<=UserName=)(?!([[:xdigit:]]{2}[:-]){5}[[:xdigit:]]{2})(.*?)(?=@|,)
Address Regex: (?<=Framed-IP-Address=).*?(?=\s*,)
The Username regex is basically looking for the UserName field entry and taking the information after it if is not a MAC address and it takes everything else up until an @ or , which means it will only take the username prefix if the ISE log contains a username in username@domain format.
What I'm trying to figure out now is how to do these so that I can still publish MAC addresses/IP mappings to the traffic logs if we want but without prefixing them with the domain. We want the domain on there for authenticated users so that we can use user-id based policy but any devices that we have as guests won't have a domain account but we'd still want to see that user account info in the firewall. Unfortunately, the default domain isn't assigned at the syslog filter and is set in the server instead and you can't add multiple instances of the same server.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2023 06:17 PM
Hi @AhmedAlRashed ,
It works for me. This URL has instructions for ISE guest, but it works for all authentications -> https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Cm5sCAC. There is another URL in @raji_toor 's response as well. @jsalmans told you what filters he used to get it working.
I use these filters:
Event Regex: ([A-Za-z0-9].*CISE_Passed_Authentications.*Framed-IP-Address=.*)|([A-Za-z0-9].*CISE_RADIUS_Accounting.*Framed-IP-Address=.*)
Username Regex: User-Name=([a-zA-Z0-9\@\-\\/\\\._]+)|UserName=([a-zA-Z0-9\@\-\\/\\\._]+)
Address Regex: Framed-IP-Address=([0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3})
It works great. It gets wired and wireless. It gets the domain/ma-c0-0a-dd-re-ss of MAB devices. MAB (MAC authentication bypass) will not give you a username because EAP is bypassed. If someone wants something more descriptive for devices, they may look into Device-ID.
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-24-2023 10:00 PM
Thanks @TomYoung!
Is there a way to apply user groups in security policies based on information received from ISE, i.e. currently we have group mapping profile and we have mapped the AD groups and we defined group-based policy rules.
Thanks,
Ahmed
Ahmed
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2023 04:35 AM - edited 10-25-2023 04:37 AM
Hi @AhmedAlRashed ,
That is a great question, and one I did not fully answer. In essence, you are asking about machine groups in AD. If you created one, I fear that the members retrieved would not match the domain/ma-c0-0a-dd-re-ss format that ISE sends, and the user would not match the group. We would need to test. I don't know what changes could be made so that the ISE user and AD group member match.
If you have Panorama, you could use the Plugin for Cisco TrustSec. ISE would have to assign SGTs in the policy set. It would then communicate these SGTs through pxGrid to Panorama. These SGTs could then be used to for Dynamic Address Groups. The theory is fantastic! The NGFW is able to use information from ISE for security policy. I have never used it. I saw a thread on Reddit from someone who has and they said (1) it can sometimes be 5-7 seconds slow, (2) sometimes does not catch every device, and (3) now means Panorama needs to be up during operational hours in order for the mappings to work. That's not my feedback. Again, this would need to be tested.
It would be nice if we could create static User-ID groups. We can create static User-ID mappings through the XML API.
If the devices have static IP addresses or DHCP reservations, you could create static address groups. I know that takes a lot of manual work.
Device-ID is another potential solution. It works best when the NGFW can observe the DHCP traffic. It can classify devices to be used in the security policy.
The last option is to integrate Device-ID with ISE through Cortex XSOAR, but that is expensive.
I would love to hear if anyone has solved this problem, or if they have good success with the TrustSec Plugin, or anything else. That is what this community is all about!
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2023 01:24 PM
If I'm understanding what you're asking for... If you are associating MAC addresses to domain usernames via the MyDevices portal then the filter I showed earlier in the thread I think should capture the domain username and allow the Palo to do the username-to-IP-mapping and security enforcement based on AD user or groups. You just need to make sure the capture on the syslog messages from ISE is looking at the appropriate field in that message... quoted from my earlier post:
"What I determined is that the radius messages sent by ISE actually contain multiple username fields. UserName tends to be the actual user's ID and User-Name seems to be the machine's ID."
So what I believe we did is require device registration for non-802.1x devices in the MyDevices portal (we don't use it as part of a BYOD flow, just standalone by itself) and the authentication on that portal is set to use an AD join point. So the user logs in with their domain user account and registers the MAC addresses for their devices. When one of those devices connects, the syslog generated and sent to the firewalls contains all of the info including the username that was associated with that device via the registration process (which is their AD username). The Palo is set to extract the AD username and IP address for the mapping which then allows user-based policy to be enforced including any groups that user is assigned to.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2023 04:10 PM
Hi @TomYoung
Fantastic knowledge sharing! We have a user-id agent mapping IP addresses to usernames and I've setup Panorama to connect to the User-ID agent and redistribute the data to the firewalls.
The customer is wanting to integrate Cisco ISE for SGT enforcement. I've done some research and yes, you are correct, Cisco TrustSec plugin would work with DAGs and the last can be applied to security policies.
There is another solution though, but it needs GridMeld to be integrated and that is not supported by Palo Alto as far as I know.
I will try to setup a syslog filter on the User-ID agent and add the MnTs to the monitored servers, but this won't let me to enforce user groups security policies from Cisco ISE, it will still need an LDAP server profile and group mapping profile.
Thanks,
Ahmed
Ahmed
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-06-2024 04:46 PM
Hi @TomYoung,
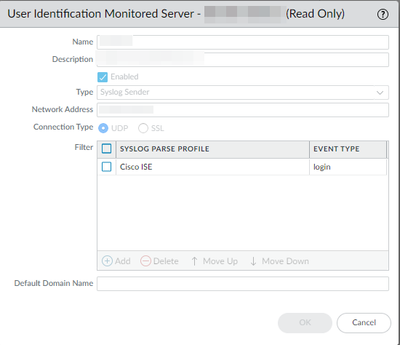
I've got the syslog server monitor sorted and now I can see dot1x auth. The filter that I used is for login events, however, I was wondering if I need to setup another filter for logout events?
In Traffic logs, it appears that for different sessions from the same IP address, there are source user populating and sometimes it doesn't, any idea? I can see the user to ip mapping under User-ID log and the event un Live logs in ISE.
Thanks,
Ahmed
Ahmed
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-09-2024 02:41 PM
Hi @AhmedAlRashed ,
I only have the login event also. With regard to the source user populating, you could increase the User Identification Timeout (min).
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2024 07:50 AM
I'm using the same regex and they work great. But I've noticed I'm getting some mappings from ISE for domain-joined desktops that are not logged in. They are in the format "host/hostname.mydomain.com", so for example the User-ID map in the Palo is showing them as "mydomain\host/desktop123.mydomain.com". How can I remove the "host/" and the trailing "mydomain.com" so it just says "mydomain\desktop123" ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-12-2024 03:25 AM
Sorry @Maxstr I don't have an answer to your question as I've deployed this to one of our clients, we don't manage the client anymore, so I don't have access to that environment to check/validate your question.
Hope someone else can help you find a solution.
Ahmed
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-12-2024 02:29 PM
I am also having this issue. Did you happen to have any luck on this?
Also, is anyone else running into an issue using the above RegEx where the username is prepended by and extra forward slash "mydomain\\username"? Any help would be much appreciated.
- 1 accepted solution
- 31299 Views
- 13 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma Access CIE and User-ID mapping not working for groups in Prisma Access Discussions
- [Proposing Solution] Failure to extract zip file downloaded from ThreatGrid integration command in Cortex XSOAR Discussions
- Regarding the support for Cisco ISE integration with PAN-OS 12.x. in Next-Generation Firewall Discussions
- On-Boarding of Cisco SDWAN to Prisma in Prisma Access Discussions
- Problem with Cisco WSA Proxy integration in Cortex XSOAR Discussions