- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
datapalne issue
- LIVEcommunity
- Discussions
- General Topics
- datapalne issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
datapalne issue
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2022 10:32 PM
I have 2 Paloalto firewalls working as ha active-passive, yesterday we had HA test so try to pass the traffic to the passive device buy suspend the active, the passive become active everything works fine till now my issue is the interface of the firewall 2 is not responding to anything ping or anything my network is down in Cisco switches showing interface up but not showing lldp Although lldp is enabled on Paloalto, now I’m rollback to firewall 1 Everything work fine, but the second firewall still its interfaces not working it’s up but not passing any traffic even when I try to connect PC directly to Interface There is no ping
even I tried to factory reset and still the same issue and upgraded the device to the latest pan-os 2.0.1
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2022 11:02 PM
The passive device does not respond to anything (besides on the mgn interface). That's due to moving the IP and MAC to the active node, the passive node has no IP on the "traffic" interfaces.
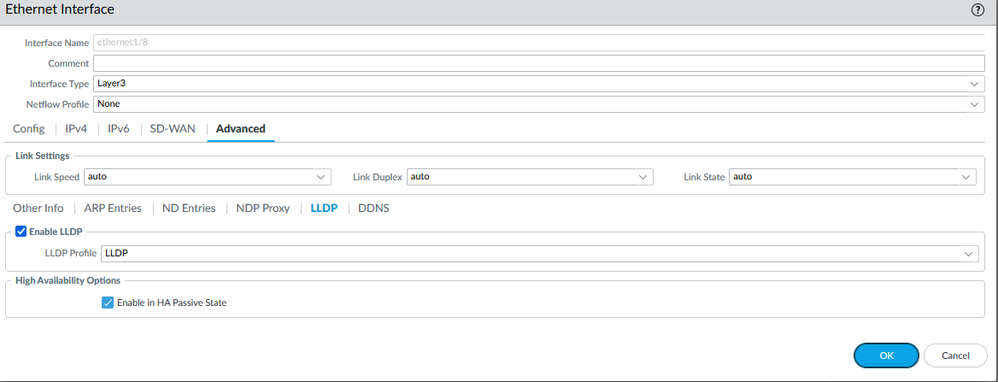
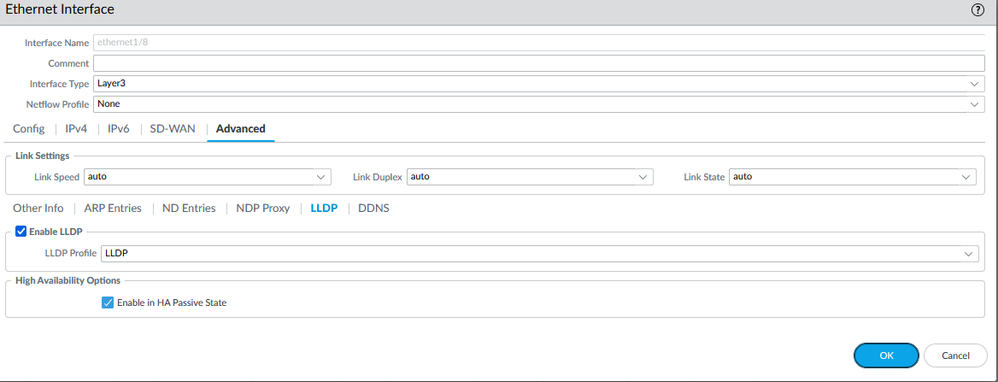
If you have LLDP enabled, please verify that "Enable in HA Passive State" is ticked (Interfaces --> Ethernet --> your Interface --> Advanced --> [x] Enable LLDP -- [x] Enable in HA Passive State)
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2022 11:12 PM
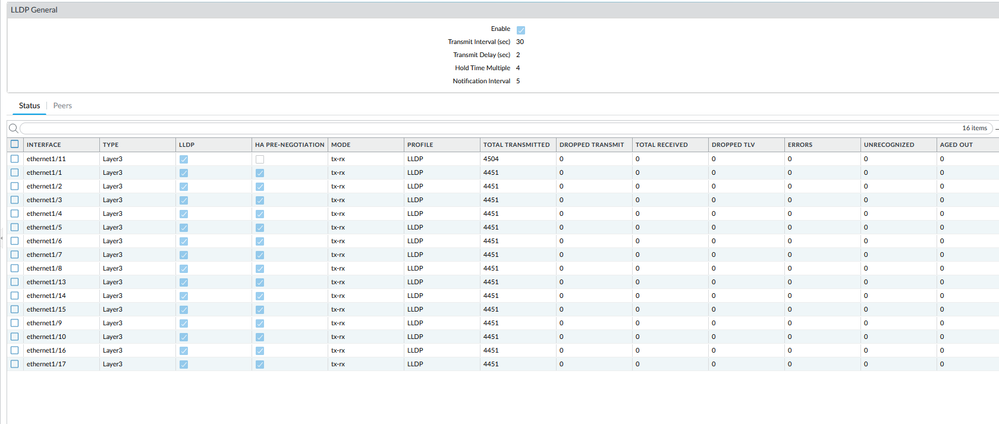
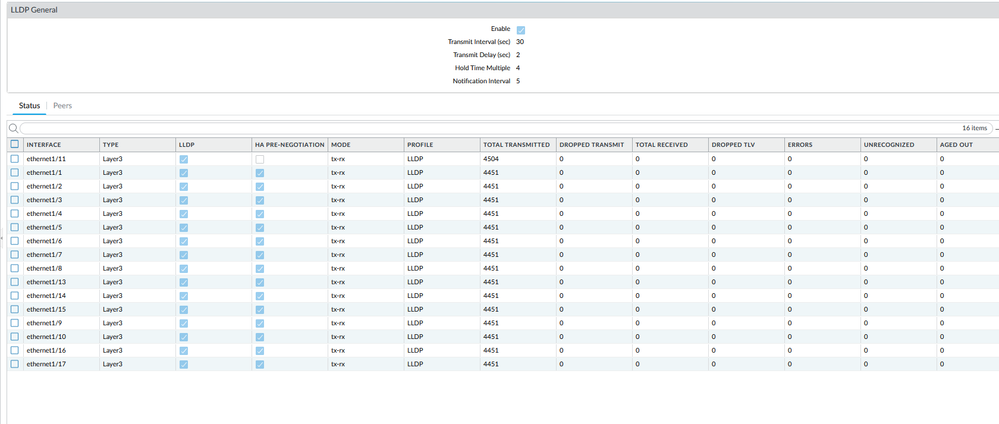
the LLDP is enabled on the Passive firewall kindly check the attachment for that, I try to make the passive to be active but still have the same issue, I try to factory reset the firewall and try to do basic configuration just to check the issue is related to ha or we have a hardware issue in the data plane.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2022 11:24 PM
the LLDP Is enabled on the passive firewall, I try to suspend the local device for ha in the active firewall to move the traffic to the passive but the device does not forward any traffic, and it becomes active in ha, I also try to remove it from ha and upgraded the device to the latest pan-os 2.0.1 also factory reset the device but still same
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2022 11:36 PM
the LLDP is enabled on the passive firewall, I try to make the passive firewall become active but still faced the same issue also remove it from ha and check the interface but no luck, any idea
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2022 11:38 PM
I try to upgrade the device to the latest pan-os 2.0.1 and still the same also factory reset the firewall and setup the basic configuration to check the interface but still same
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-06-2022 01:35 PM
Can you confirm the version you're using?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-06-2022 07:08 PM
Hopefully you were able to resolve this over the weekend, however it seems like this is going to be harder to troubleshoot over a text based forum and things may not have been in a good spot before your test. Hopefully if you haven't already done so, you've engaged TAC to look at this with you to rule out any configuration or device issues.
A couple things that I have questions/observations on after a few of your comments:
- Have you ever done a failover before and have it work, or is this a new Active/Passive configuration?
- Attempting to ping an interface isn't really that great of a test with PAN, as there's moving parts to having the traffic allowed. When you did the factory reset on the passive firewall, did you remember to active an interface-management profile that allowed ICMP and actually allow it on your rulebase assuming you weren't relying on intrazone-default?
- On your passive firewall, what is the actual status of the device? When you go through and reset things and configure it, are you seeing the auto-commit and subsequent commits succeed?
- Lastly if you're actively facing an issue with an HA test without making other prior changes, I'd really recommend NOT upgrading PAN-OS. You're really just introducing another set of variables to the issue, and you've now moved into a state where you had a known working HA-pair to start with to one that's in an unknown state. When trying to solve an issue, introducing changes just increases complexity.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-06-2022 10:17 PM
Have you ever done a failover before and have it work,
yes we have tested the ha failover about 6 Months ago.
is this a new Active/Passive configuration?
no.
On your passive firewall, what is the actual status of the device?
the management plane works fine but the data plane is not working the data plane session count is zero.
When you go through and reset things and configure it?
after upgrading the passive i thought its a configuration issue so i factory rest the device to sure by using this command
request system private-data-reset and also do the factory rest by palo alto factory reset maintenance mode same thing no responses
on data plane
are you seeing the auto-commit and subsequent commits succeed?
yes, and I do some change and the commits working fine
Attempting to ping an interface isn't really that great of a test with PAN, as there's moving parts to having the traffic allowed. When you did the factory reset on the passive firewall, did you remember to active an interface-management profile that allowed ICMP and actually allow it on your rulebase assuming you weren't relying on intrazone-default?
yes i add icmp in the interface-management profile and apply this on the interface that was under test,and i creat new rule to allowed
the traffic to pass the firewall ,
i also try do downgrade to 10.1.5h2 after factory rest and no luck
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-07-2022 07:41 AM
Hi @dawoodJabbar ,
I am little confused by what is the acutal problem you are facing...
Am I understand correctly that:
- You have failovered to second member and no traffic was passing over the firewall
- You have removed this member from HA, factory reset it and try to use it as standalone but still no traffic is passing the firewall?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-07-2022 07:47 AM - edited 06-07-2022 07:48 AM
Yes exactly today Palo Alto TAC team investigate this issue with me about six hours they collect log and try everything downgrade but no luck actually they say that its data plane issue and will investigate more in the log they took and if they nothing found it’s RMA
- 5865 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- playbook completely stuck on a simple condition in Cortex XSOAR Discussions
- Is there a difference between issues and alerts in XQL queries? in Cortex XDR Discussions
- Palo Windows ARP Issue - Windows Hosts Not Installing ARP info in Next-Generation Firewall Discussions
- PAN‑OS versions affected by PAN‑307795 in Next-Generation Firewall Discussions
- HealthCheckServerConfiguration fails with TypeError on XSOAR Cloud v8.13.0 in Cortex XSOAR Discussions