- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect agent download from direct URL
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect agent download from direct URL
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
GlobalProtect agent download from direct URL
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 02:18 AM
Hi everyone,
Do you know if it's possible to block the download of the globalprotect agent via the direct URL ?
The goal here is to force users to authenticate in the portal web page to be able to download the agent.
Ex. for the 64bit agent :
https://<my-portal-address>/global-protect/getmsi.esp?version=64&platform=windows
If yes, could you please share the steps to solve it ?
Thanks a lot !
Fabien.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 07:30 AM
There are couple of steps to achieve this depending on the configuration that already exist on your appliance.
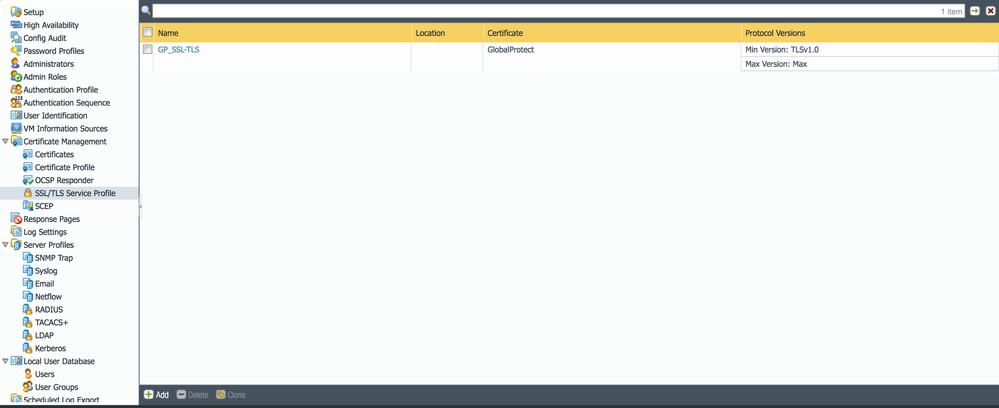
1. Go to device > Certificate mgt > ssl/tls service profile > add. It should look like the image (2) below when you are done.
2. Network > GlobalProtect > Portal > Add >On the General Tab > Add > name> external interface > IP Address
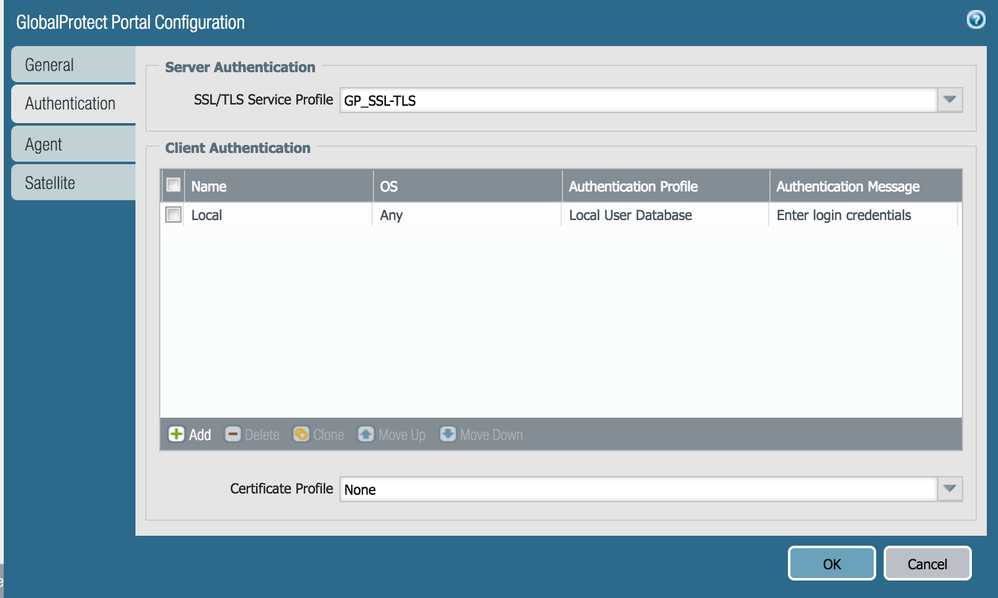
3. Then on the authentication Tab confiigure your PA appliance as shown below in Image 1. This forces the portal to request user credentials before they can access the portal to download the agent. FYI, my environment uses the Local User database for authentication, yours may be different.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 07:42 AM
You will also need to Generate a certificate or upload the certificate for Global protect using the public IP address of your untrust interface. see below
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 08:38 AM
I'm not positive of a way to actually do this and still allow the download to accomplish on the portal. It's kind of like the ASAs in the point where if you know where to direct it for the file itself you can get the download without authentication. You could put the link itself behind a captive portal if this is a big enough issue for you, but the user experiance if they go through the portal would be pretty bad.
The authentication to the portal itself I'm sure is working perfectly fine, the file however can still be downloaded even if you don't authenticate by going directly to the download link.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 08:39 AM - edited 07-25-2017 08:41 AM
I think @FabienJ has already done the steps you describe ... what he wants is to FORCE users to authenticate so nobody should be able to download the GP agent without log in
You probably want to ask your SE for a feature request.
I can think of a possibility to achieve this, but at the moment I don't know if this works and it also contains something that's normally not recommended ... I will first do a little test before I write some sensless stuff here
... and once again @BPry was faster 😉 ...
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 08:51 AM
@Oyin-Idowu Thanks for your quick answer but yes, all the basic configuration is ok.
@BPry Yes, same as Vsphere client an so on ... I'm agree that there are no "confidentials" infos insinde the GP client, so this is not so armfull but still not really clean from a security point of view.
@Remo I will ask to my SE. I've tried few things using security policies with URL filtering without sucess. I'm waiting for your test result 🙂
Thanks !
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 09:28 AM
What PAN-OS version are you using? I will probably try with 8.0.2 ...
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 11:52 AM
PAN-OS 7.1.10 and 8.0.x I think it will be the same with all versions
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 03:02 PM
first results: Wait for the SE to get this implemented the right way ... I'm not giving up, but it at the moment it looks like there are only two possibilitys: it is really not possible or if there is still a little chance, it will be really ugly ...
Right now it is even worse: I am still able to download the client with the direct url when the Login Page is DISABLED!
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-27-2017 08:34 AM
Ok I failed to get this done. What I tried:
- (I know this is really ugly) enable user identification on the Untrust/Internet zone. With this I was hoping that there will be a ip-user-mapping entry after a userlogin to the portal website. Then my plan was to only allow access to the download url for authenticated users. - Result: url filtering is possible but there is no ip-user-mapping
- I also tried with captive portal. Then my intention was to prepare the captive portal website to look like the GP Portal. And block the access to the upcoming GP portal URL, so I can place a block response page that looks like the GP portal after login. This way I would have a usermapping which could be used to allow only authenticated users to download the software - Result: if you configure a captive portal rule for accessing the GP portal IP --> GP Portal always comes first, captive portal does not show up
So you eithe wait for this feature request or place the GP software on your own webserver with either doing the authentication completely yourself on the webserver or use a captive portal rule there so your PA firewall at least handles the authentication/authorization part ...
PS: as I already wrote, when you disable the portal login website completely the download is still available with the direct url
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-27-2017 05:30 PM
Hi FabienJ,
This is possible.
You'd need an external web-server to host the GP software.
Now, if you can configure some sort of authentication there, that's all well and good. If not, you can make use of PAN OS 8.0 for the 'Authentication policy' feature (this is what I'll demonstrate). For authentication policy approach, you should be hosting the file on a http server. Using this method, you can even do MFA for just the download, so I guess that's a plus.
Well, here are the steps:
Login to the command line and issue the following commands:
- set global-protect redirect location <path of the external server repository of the file>
- set global-protect redirect on
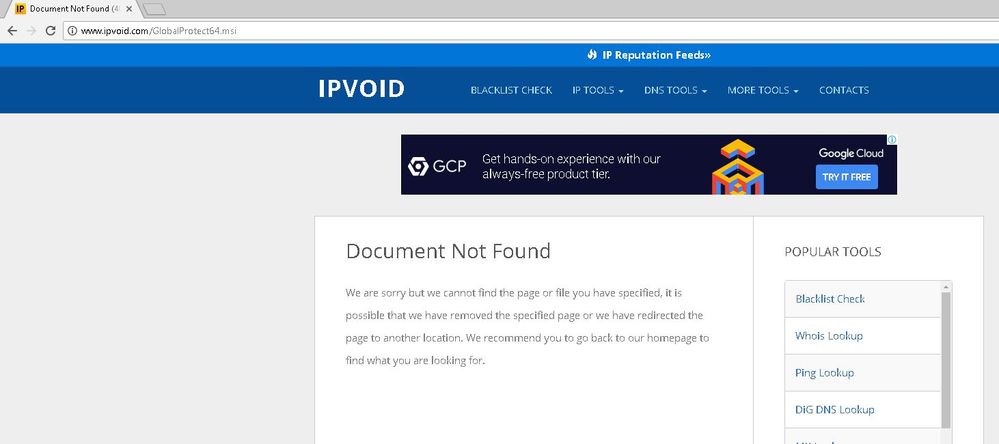
In my case, since I didn't have a http server, I just chose something random like: http://www.ipvoid.com
Run the command - set global-protect redirect show
You should see the output similar to mine:
cfg.global-protect.redirect.flag: True
cfg.global-protect.redirect.location: http://www.ipvoid.com
At this point, you are pretty much done if you are doing authentication on that external server.
Proceed if you want to use the Authentication policy approach.
1. Create a captive portal
Redirect host, in your case, will be the external facing address that can server the authentication page.
Choose an appropriate SSL/TLS profile and authentication profile.
2. Create an authentication policy
Please keep in mind that you'd have to choose the source zone as Outside. I am using Inside because of the way my lab setup is configured. Also, the destination zone would be something depending on where the file hosting server lies and if NAT is required or not. Destination adddress would be whatever address you have entered as the file server. You can choose Authentication Enforcement to use two-factor, if you want. I am just using a simple Web-form (captive portal).
Here's the demo:
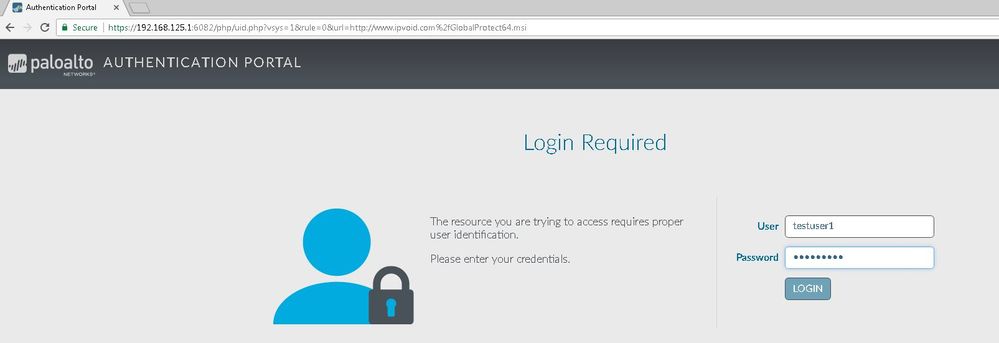
Whether I go to the GP-portal, login and then click on the download GP client links or directly enter https://<my-portal-address>/global-protect/getmsi.esp?version=64&platform=windows , I will get an MFA portal page (customizable btw, under Device->Response pages), which will look like this:
I would authenticate and then the firewall would redirect me to the file server (in this case it's just going to ipvoid.com).
Hope that helps.
Regards,
Anurag
ACE 7.0, 8.0, PCNSE 7
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-28-2017 12:05 AM
Hi @ansharma
But if someone knows the download url, he will still be able to go directly there and download the software ...
This is the point in this topic, that the download is available without login - if someone knows the download url - and that the download is still available when the portal is disabled ...
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-28-2017 04:01 AM
I though the user wanted to know a way to force authentication for people going directly to the download link rather than the portal first. This is what the method above provides.
Honestly, you can't prevent people from knowing the portal link. I mean, most companies use something simple like gp.acme.com or vpn.acme.com. And, besides Geolocation blocking, you could just find many of them accessible. So, what if you did - it's requiring someone to do a portal login to connect and/or using the Authentication policy to download the GP client from their portal.
Additionally, even if someone downloads the GP from the portal link, the only thing being taxed is the firewall's resource providing the download, which again you can enforce authentication using the method described. One can go to cisco's website from any valid (entitled) account and download Anyconnect client. A blank VPN client is just that, blank.
Regards,
Anurag
ACE 7.0, 8.0, PCNSE 7
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-28-2017 06:08 AM
Since you are setting the GlobalProtect redirect flag you won't be able to actually get to the client download package, that redirect will force you over to the server that you set and that's where the Captive Portal piece comes in to actually get this to work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-28-2017 06:12 AM
Out of curiosity and because I don't think it's been asked yet, what is your industry that you actually have to worry about people using the direct URL link? I can't get my users to remember the portal address itself, let alone the package URL.
- 17246 Views
- 19 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- High Bandwidth on Broker VM: Cluster Mismatch (v29 vs v28) & P2P in Cortex XDR Discussions
- GlobalProtect Agent constantly 'Not Responding'. in GlobalProtect Discussions
- GlobalProtect VPN Client windows 11 crash in GlobalProtect Discussions
- No Linux dowload available in General Topics