- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
can we allow sign in to webex only using defined company account ?
- LIVEcommunity
- Discussions
- General Topics
- can we allow sign in to webex only using defined company account ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
can we allow sign in to webex only using defined company account ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2021 12:31 PM - edited 07-18-2021 12:32 PM
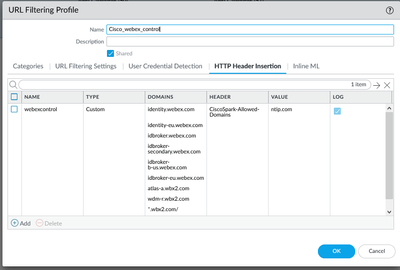
I have followed below article and tried to configure http header insertion in URL filtering profile , but still able to login using other company account.
Also in url filtering log, no logs showing for http header. We have enabled decryption for any destination and any service but no luck.
Also as per finding , cisco-spark app traffic is not showing decrypted in url filtering logs. It could be due to ssl decryption exclusion for cisco-spark.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-19-2021 10:17 AM
Have you taken a packet capture and verified that the header is actually being inserted when it traverses the firewall? WebEx is where that header actually gets read to determine if the account should be able to login or not, and if you're able to login with a domain not specified in the header it would point towards your insertion not working.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-11-2021 02:20 PM
We can't do pcap as traffic is https. I am suspecting header used in cisco webex login.
In my testing I am using http header "CiscoSpark-Allowed-Domains" , not sure whether this header correct or not.
Did decryption. Also in Device > decryption exclusion , disabled webex related domains to allow decryption for those domains, but no luck.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-16-2022 01:26 AM
++You need to configure decryption to be able to read http header insertion by firewall.
++Then follow below steps Ref Link : https://help.webex.com/en-us/article/m0jby2/Configure-a-list-of-allowed-domains-to-access-Webex-whil...
++Add the HTTP header CiscoSpark-Allowed-Domains: and include a comma separated list of allowed domains. You must include the destination domains: identity.webex.com, identity-eu.webex.com, idbroker.webex.com, idbroker-secondary.webex.com, idbroker-b-us.webex.com, idbroker-eu.webex.com, atlas-a.wbx2.com and your proxy server includes the custom header for requests sent to these destination domains.
For example, to allow users from the example.com domain, add:
-
CiscoSpark-Allowed-Domains:example.comfor domain(s):
identity.webex.com, identity-eu.webex.com, idbroker.webex.com, idbroker-secondary.webex.com, idbroker-b-us.webex.com, idbroker-eu.webex.com, atlas-a.wbx2.com++Create a rule for Webex and add webex in applications and applicable security policy which we created as ttp header insertionAttached few snap
- 5985 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Introducing the Strata Cloud Manager (SCM) Terraform Provider: Automate and Scale Your Network Security in Strata Cloud Manager
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- Request for Assistance: PA-850 Recovery Boot and Support Account Registration in Next-Generation Firewall Discussions
- License Forms in General Topics
- Header Insertion doesn't work in Next-Generation Firewall Discussions